What Are The Best SCEP Certificate Authorities (CAs) for Jamf Environments?
What Do I Need to Be Able to Push Certificates to My Jamf-Managed Devices?
If you want to push certificates to your Jamf-managed devices, you will need two main things:
- A Jamf subscription (Jamf Now, Jamf Pro, or Jamf School) to manage your Apple devices and deploy profiles that include certificate enrollment.
- A SCEP certificate authority (CA) that can integrate with your Jamf environment to issue the necessary certificates to your devices.
Together, the Jamf subscription and the SCEP CA allow you to automate the issuance and management of certificates for your Apple devices, which means all your users can securely connect to Wi-Fi, VPNs, and other resources without needing to manually install certificates on their devices.
But how do you choose the right SCEP CA for your Jamf environment? There are several options available, each with its own strengths and considerations. In this article, we will explore the best SCEP certificate authorities for Jamf environments and help you determine which one is the best fit for your organization’s needs.
What is SCEP and Why is it Important for my Jamf Environment?
Simple Certificate Enrollment Protocol (SCEP) is a popular protocol used to automate the issuance and management of digital certificates to users and/or devices. These certificates are used across various applications and services, such as Wi-Fi authentication, VPN access, email encryption, and more. If you have a work device that connects seamlessly to your office Wi-Fi network, SCEP is likely behind the scenes, ensuring that your device can authenticate securely without manual intervention.
When managing Apple devices with Jamf Now, Pro, or School, integrating a SCEP certificate authority (CA) is crucial for maintaining secure authentication and access control. A SCEP CA allows you to automate the issuance of certificates to your devices, ensuring that they can securely connect to your network and access resources without the need for manual certificate management.
Since Jamf doesn’t include a built-in SCEP CA, it’s essential to choose a reliable and compatible CA that can integrate seamlessly with your Jamf environment. The right SCEP CA will not only enhance security but also streamline device management, making it easier for IT administrators to maintain a secure and efficient network.
Do I Need to Deploy and Manage My Own SCEP Certificate Authority?
Nope! While just a few years ago deploying and managing your own SCEP CA on top of Windows Server and Active Directory Certificate Services (AD CS) was the primary option for creating your own SCEP CA, there are now several cloud-based SCEP CA solutions that eliminate the need for on-premises infrastructure. These cloud-based options offer ease of use, scalability, and often come with additional features that can enhance your certificate management experience.
Which Jamf Products Support SCEP?
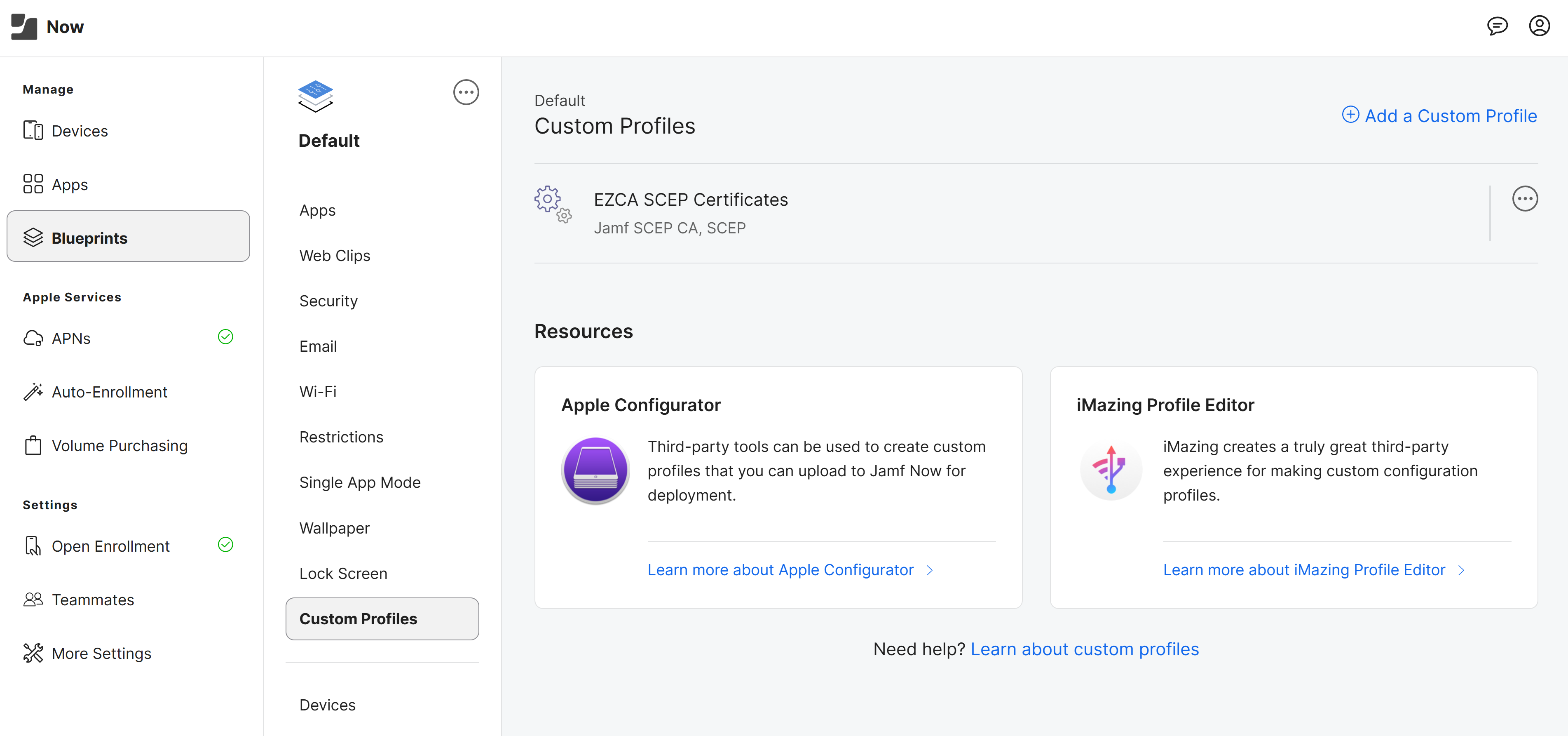
All of them! While Jamf Pro and Jamf School have integrated SCEP support for both user and device certificates, in Jamf Now you can use Apple Configurator or iMazing Profile Editor to create a Custom Profile that includes SCEP certificate enrollment and then deploy that profile to your devices. This means that regardless of which Jamf product you are using, you can leverage SCEP to automate certificate issuance and management for your Apple devices.
- Jamf Pro: ✅ Direct support for SCEP
- Jamf School: ✅ Direct support for SCEP
- Jamf Now: ✅ Support for SCEP via Apple Configurator Custom Profiles
What Cloud SCEP Certificate Authorities (CAs) are Available for Jamf?
There are several cloud-based SCEP CA solutions that can integrate with Jamf environments. Some of the most popular options include:
EZCA: The Favorite Cloud PKI for Microsoft Customers
If your Jamf environment exists inside a broader Microsoft or hybrid identity stack, EZCA is usually the strongest option. A lot of organizations use Jamf to manage Apple devices while still relying on Entra ID, Microsoft 365, Azure, or other Microsoft-centric services for identity and access. In those environments, the winning SCEP CA is rarely the one that can issue a certificate and nothing more. The better choice is the one that can support Jamf today without forcing you to re-architect everything tomorrow.
That is where EZCA stands out. EZCA is a cloud PKI built to remove the operational burden that usually comes with private CAs while still giving security teams the control they need. Instead of standing up and maintaining a traditional CA stack, you get a managed, modern private PKI that can issue SCEP certificates for Apple device management and extend into the rest of your certificate lifecycle needs.
For Jamf teams, EZCA is especially attractive because it is not limited to one narrow use case. You can use it for Jamf certificate enrollment, but you can also use it for broader private PKI requirements such as Wi-Fi authentication, VPN access, server certificates, app certificates, ACME certificates, and other certificate-driven workflows. That matters because many Jamf deployments start with device onboarding and quickly expand into passwordless authentication and network access.
Here are a few reasons EZCA is usually the best fit for Jamf environments:
- Built for cloud-first operations: EZCA helps you avoid the classic pain of deploying and maintaining AD CS, NDES, or other infrastructure-heavy certificate services just to make SCEP work reliably.
- No cloud infrastructure to deploy and maintain: With EZCA, you don’t have to deploy any Azure or AWS infrastructure into your own subscriptions/accounts. In just a few clicks you can deploy an HSM-backed CA in regions all around the world, with enterprise-ready SLAs and support.
- Strong fit for hybrid Apple and Microsoft environments: If your organization uses Jamf for Apple devices but still depends on Microsoft Intune for Windows management and Entra ID for identity, EZCA can support your SCEP needs without forcing you to adopt a separate CA strategy for your Apple devices.
- More than just SCEP: SCEP is important, but most organizations eventually need more than SCEP. EZCA supports a broader private PKI strategy including SSL certificates, TLS inspection, ACME support, and more so you do not outgrow your CA as soon as requirements expand.
- Security and control: For teams that care about HSM-backed key protection, compliance, and modern certificate management practices, EZCA offers a more complete long-term story than a narrowly scoped enrollment tool. Admin approvals, domain management, and complete audit logging with SIEM export are built-in at every later of EZCA.
- Low-cost pricing with unlimited SCEP certificates: EZCA is a low-cost option for Jamf teams because pricing is not based on the number of users or the number of certificates you issue. There is no per-user fee and no per-certificate fee, which makes budgeting much easier for organizations that expect certificate usage to grow. If you need to issue unlimited SCEP certificates for Jamf-managed devices, EZCA is usually one of the most cost-effective ways to do it.
- Integrates Natively with Cloud RADIUS: The value of certificates comes when they’re actually used for passwordless scenarios, such as network authentication via RADIUS. EZCA integrates natively with EZRADIUS, Keytos’ cloud RADIUS solution, to allow you to use your Jamf-issued SCEP certificates for secure Wi-Fi and VPN access in just a few clicks.
- Hybrid support for on-premises and cloud: If you have an existing on-premises CA and want to extend it to the cloud for Jamf SCEP, EZCA can integrate and chain with your existing infrastructure while also giving you a path to a more modern, cloud-native PKI strategy over time.
If you want the short version, it is this: for most Jamf customers, especially those with Microsoft, Entra ID, or hybrid enterprise infrastructure in the background, EZCA is the best overall SCEP CA because it combines ease of deployment, broader PKI functionality, a low-cost pricing model, and a cleaner path to long-term certificate management.
Learn More About EZCA for JamfAWS Private CA: A Popular Choice for AWS Users
AWS Private CA is a credible option, particularly for organizations that are already heavily invested in AWS and want their certificate services to stay close to the rest of their AWS infrastructure. If your applications, networking, automation, and security operations are already centered in AWS, AWS Private CA can be a logical choice for issuing private certificates at scale.
For Jamf specifically, though, AWS Private CA is usually best viewed as an AWS-native certificate backend rather than a Jamf-first SCEP CA experience. It can absolutely be part of a Jamf deployment, but the value proposition is strongest when your broader architecture already lives in AWS and your team is comfortable assembling the surrounding pieces needed to operationalize certificate enrollment and lifecycle management.
Plus, AWS Private CA charges per certificate issued, which can make it a more expensive option for Jamf environments that need to issue a large number of SCEP certificates to devices and periodically renew them. If your Jamf deployment is expected to grow significantly over time, the per-certificate pricing model of AWS Private CA can become a cost consideration compared to a platform like EZCA that offers unlimited SCEP issuance for a flat fee.
That means AWS Private CA tends to make the most sense when:
- You are already AWS-first: If AWS is your operational center of gravity, using AWS Private CA can reduce the number of platforms your team has to manage.
- You have in-house cloud engineering depth: AWS Private CA is more appealing when your team is comfortable integrating certificate services into existing AWS workflows and automation.
- Your Jamf deployment is one part of a larger AWS-native estate: In that case, consistency with the rest of your cloud tooling may matter more than having a purpose-built Jamf-centric PKI experience.
The tradeoff is that many Jamf environments are not purely AWS stories. They are often mixed estates with Apple endpoints, Microsoft identity, SaaS applications, and network authentication requirements that span more than one platform. In those situations, AWS Private CA can feel less like a complete cloud PKI strategy and more like one component that still needs additional integration work around it.
So while AWS Private CA is a solid option for AWS-native teams, it is usually not the best default recommendation for Jamf customers in general. If your goal is to get a flexible SCEP CA for Jamf without anchoring your certificate strategy to AWS-specific workflows, EZCA is usually the better fit.
SCEPMan: A Focused Option for SCEP-Centric Deployments
SCEPMan is one of the better-known names in cloud-based SCEP, and it is a reasonable option for organizations already using Azure that want a focused certificate enrollment tool and are already comfortable with its Azure-oriented model. For teams whose needs are centered very specifically around SCEP issuance, SCEPMan can do the job.
Unlike AWS Private CA and EZCA, SCEPMan is deployed to your own Azure subscription where you run, configure, and pay for the underlying infrastructure (Azure App Service + other Azure infrastructure). For teams already in Azure this can be a reasonable deployment model, but for Jamf teams with minimal-to-no Azure footprint this can introduce a difficult learning curve as soon as you need to manage multiple regions or deployments.
Additionally, Jamf buyers should think carefully about whether they want a SCEP tool or a broader PKI platform. Those are not always the same thing. In many Apple device management projects, the initial requirement sounds simple: issue certificates to devices. But once the deployment matures, teams often need more lifecycle automation like admin approvals + domain management, broader protocol support for IoT and ACME workloads, or additional certificate use cases across infrastructure and applications.
That is where SCEPMan can become a narrower fit than EZCA. If all you need is a SCEP-focused solution and your Azure environment already aligns with how SCEPMan is deployed and managed, it may be perfectly serviceable. But if you want a platform that doesn’t require maintaining the underlying Azure infrastructure and can support Jamf while also giving you room to expand into a more complete private PKI strategy, EZCA is usually the safer long-term choice.
In practical terms, SCEPMan can be a good fit when your requirement is tightly scoped to SCEP enrollment and you are comfortable with Azure infrastructure and a more specialized tool, but EZCA is usually the better long term choice when you want Jamf support without boxing yourself into a narrower certificate management path later on.
What is the Best SCEP Certificate Authority for Jamf?
For most organizations, especially if you are in the Microsoft ecosystem, EZCA is usually the best SCEP certificate authority for Jamf. It gives Jamf administrators what they need right now, reliable cloud-based SCEP issuance for Apple devices, without forcing the rest of the business into a narrow architecture decision later. It is also one of the easier options to justify financially because the pricing model is low cost, with no per-user fee and no per-certificate fee for issuing SCEP certificates.
AWS Private CA is a good choice for deeply AWS-centric teams. SCEPMan is a reasonable choice for teams that want a more narrowly focused SCEP solution. But if you are looking for the best overall combination of flexibility, security, cloud manageability, and long-term value for a Jamf environment, EZCA is typically the strongest option.
If you want a simple breakdown:
- Choose EZCA if you want the best all-around option for Jamf, especially in hybrid or Microsoft-connected environments, and you want a low-cost platform that does not charge per user or per certificate for unlimited SCEP issuance.
- Choose AWS Private CA if your organization is already standardized on AWS and you want your CA strategy to follow that same AWS-first model.
- Choose SCEPMan if your needs are tightly centered on SCEP and you are comfortable with a more specialized approach.
For everyone else, and especially for organizations comparing long-term flexibility, operational simplicity, and security posture side by side, EZCA is usually the best option.
If you want to see how EZCA can support Jamf certificate enrollment and broader private PKI use cases, talk to a PKI expert and map out the right approach for your environment.
How Can I Get Started with EZCA for Jamf?
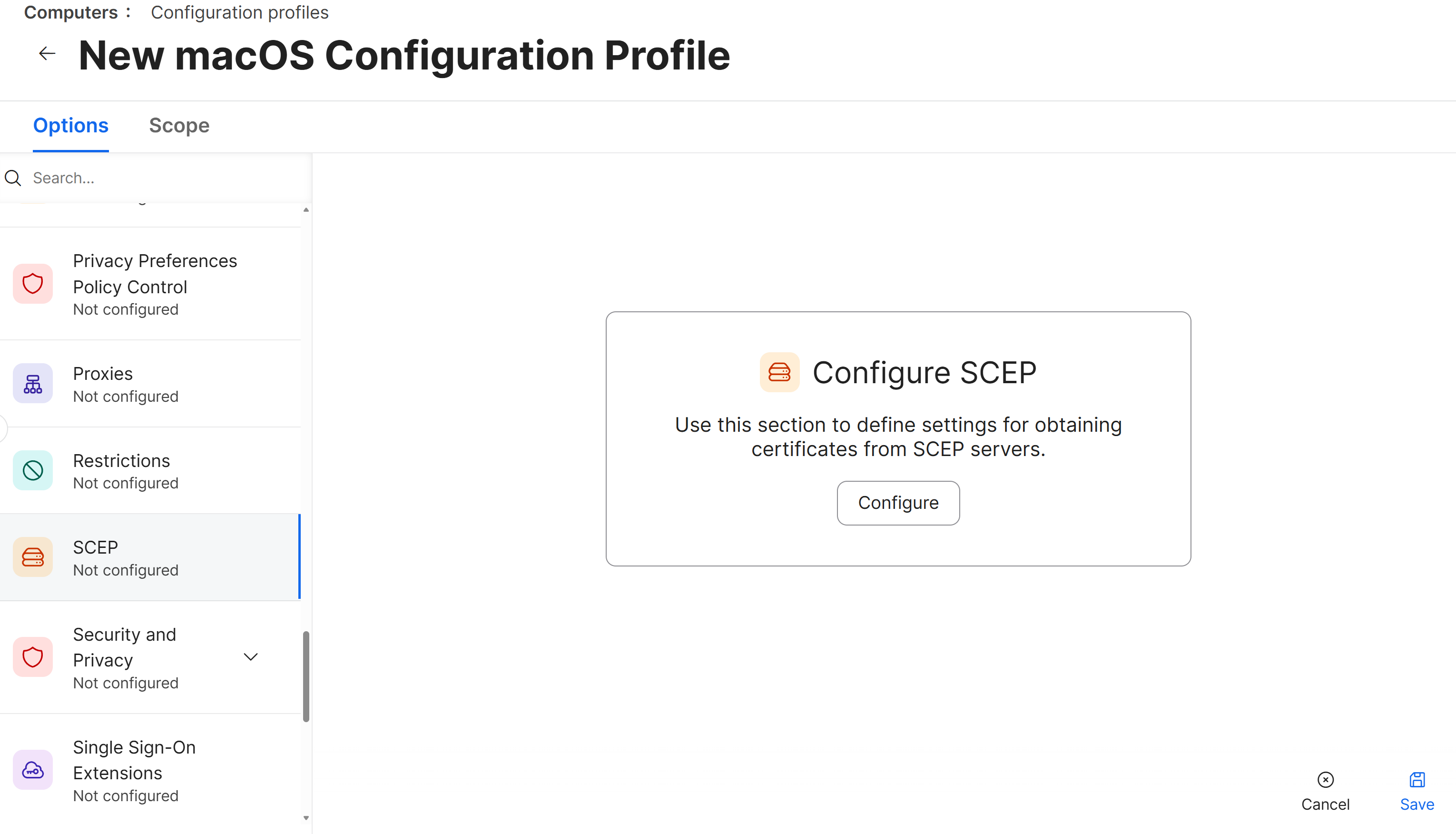
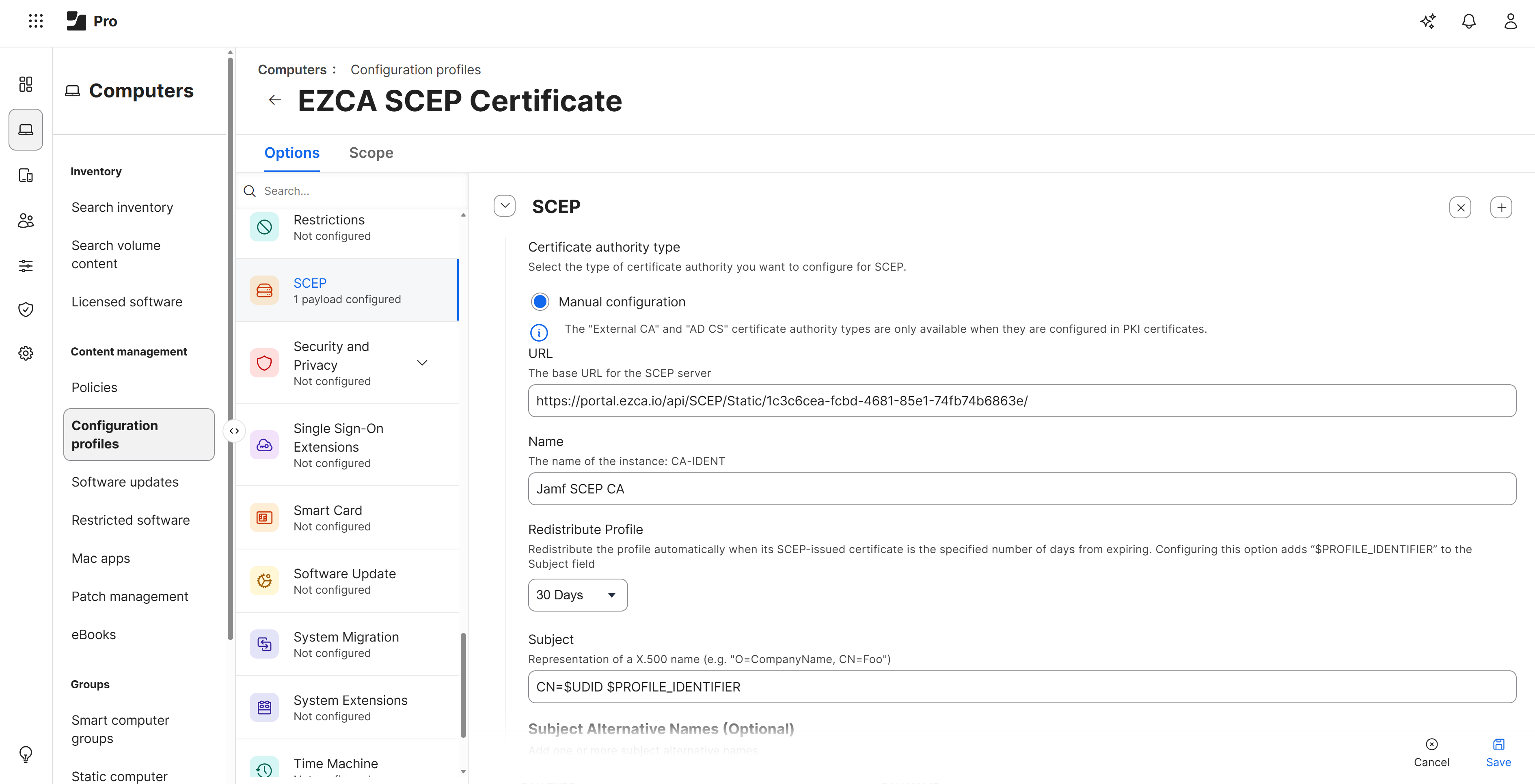
Whether you’re new to certificate management or looking to migrate from an existing CA, getting started with EZCA for your Jamf environment takes only a few minutes to set up. Simply deploy your first cloud SCEP CA, add it to your Jamf environment, and start issuing certificates to your Apple devices.
Start Your Free Trial of EZCAAlso make sure to book a call with one of our PKI experts to see how EZCA can support your Jamf deployment and broader certificate management needs.
Book a Call with a PKI Expert