
How We Secure our Infrastructure
How We Secure the Keytos Infrastructure
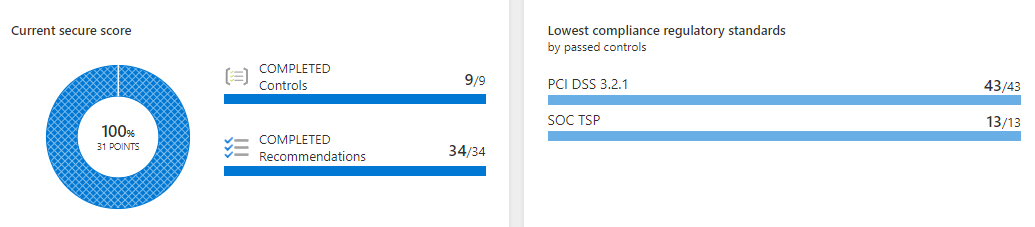
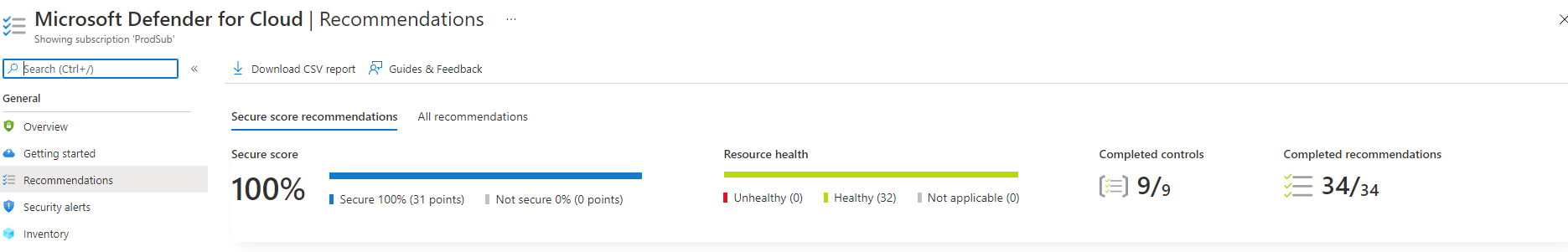
To meet our highly regulated customers needs, we exceed compliance requirements by running our infrastructure with strict security practices. In this post we will go over some key security measures we take to make sure our infrastructure is secure.
Identity Isolation
Leveraging Azure’s great identity security technology, we have created all our directories with cloud only identities with all the assurance and protection that Microsoft offers. To enhance this technology, we have added conditional access policies to require our users to have a FIDO2 hardware token to access any corporate access and blocked any password-based access.
While these steps help reduce our exposure to phishing attacks, we are going above and beyond by following Microsoft’s best practices and created our production resources in a completely different tenant with no trust to our corporate tenant. This enables us to completely isolate our production environment from our corporate environment while allowing us to have stricter requirements for users in this tenant such as: having smart conditional access policies that grant access based on risk factor that includes: smart login scores and device health.
Device Isolation
While having identity isolation is a great step on securing your resources, this only protects you for identity theft, but it doesn’t protect you from malware attacks that can silently steal your credentials or access your resources through your computer. This is why we have also implemented the Microsoft PAW model with a twist. Instead of using legacy technology with on-premises domain controllers we use Azure Intune to manage the devices and use conditional access to attest the device before each login. We also switched from having a large workstation with two VMs to having our developers have two workstations, one for corporate email and development work and a small lightweight machine for interacting with production.
Just in Time (JIT) Access
Although we are very confident on our identity story with isolated production devices and identities, we also believe humans should not access production unless it is necessary. This is why we have implemented no standing access to production, if an engineer needs to access any production resources, they must request access to the resource through Microsoft PIM.
Strict Monitoring
To monitor our services, we use the latest Azure monitoring products. While we believe that Azure products help protect our infrastructure, they do not meet our high standards for monitoring. To close that gap, we created CloudWatcher our own internal solution to monitor Azure RBAC to make sure only our Manage Service Identities have access to the resources and if any extra access is detected, alerts are sent to our security engineers to investigate and remediate the access change. Thankfully, we have never detected abnormal activity showing that other security practices have protected our infrastructure.





