
How to Set Up and Use a Yubikey in Microsoft 365
How to Start a Yubikey Deployment in Microsoft 365
Do you have a Microsoft 365 environment and want to go passwordless with YubiKeys for unphishable credentials? We’re here to help! At Keytos, we are passionate advocates for YubiKeys, with deep experience helping both large enterprises and small businesses take their security to the next level with unphishable FIDO2 and CBA credentials. Our team deeply appreciates the robust security that YubiKeys provide, and we are always eager to explore and promote cutting-edge passwordless solutions. Over the years, we’ve crafted numerous detailed guides filled with step-by-step tutorials and helpful screenshots to help you seamlessly integrate YubiKeys into your security setup.
Whether you’re a seasoned expert or a newcomer, our content has something for everyone. Our mission with this blog is simple: to make the powerful benefits of YubiKey accessible to the everyday security practitioner looking to implement secure login methods within Azure. We know that transitioning to hardware-based multi-factor authentication can seem daunting, so we’ve tailored this guide to help you understand and execute the setup process with ease. So, if you’re ready to enhance your security framework and step into the world of passwordless authentication, let’s get started!
Why Use a YubiKey in Microsoft 365?
Passwords are often the weakest link in your Microsoft 365 environment. They can be easily guessed, stolen, or phished, leaving your accounts vulnerable to attackers. Even with strong password policies and multi-factor authentication (MFA), users can still fall victim to sophisticated phishing attacks that trick them into clicking on malicious links, sharing their two-factor authentication codes, or entering their credentials on fake login pages. Despite all the training sessions and security awareness programs, users can still make mistakes, and attackers are constantly evolving their tactics to exploit human vulnerabilities.
YubiKeys, on the other hand, are compact, powerful devices designed to fortify your digital accounts against unauthorized access and phishing attacks. These devices offer a physical layer of security for authentication processes, making them more resistant to online threats than traditional password-only systems. Ideal for use across various platforms, including some legacy systems not yet supporting FIDO2, YubiKeys provide a versatile and cost-effective solution to secure your data.
This guide focuses on deploying YubiKeys in Microsoft 365 and Azure environments using the most secure methods: FIDO2 and Smartcard (PIV).
How to Choose Between FIDO2 and Smartcard (PIV)
When looking at phishing resistant authentication methods, you have two primary options: FIDO2 and Smartcard (PIV). Each has its strengths, and the choice depends on your specific needs and environment.
- FIDO2: This modern authentication method provides excellent phishing resistance but is still in the process of gaining mass adoption. While many devices support FIDO2, there are still some that do not, which can lead to compatibility issues. If your users primarily use modern devices and browsers, FIDO2 is a fantastic choice for its ease of use and strong security features.
- Smartcard (PIV): A great alternative for systems where FIDO2 isn’t available. Smartcard authentication has been used by governments and enterprises for over 30 years, so it is supported by most devices, solving the compatibility gap of FIDO2.
Before you go and buy an additional smartcard, it’s important to know that your YubiKey can function as both a FIDO2 passkey and as a smartcard, storing certificates and enabling authentication across diverse environments.
TL;DR: Set up your YubiKey to accommodate both FIDO2 and Smartcard (PIV), and you’ll never have to think about how you’re authenticating! Just plug in your key and log right in!
How to Set Up Your YubiKey with Microsoft 365
Now that you understand the benefits of using YubiKeys and the differences between FIDO2 and Smartcard authentication, let’s dive into the setup process for Microsoft 365 and Azure.
Step 1: How to Enable Passkey (FIDO2) Authentication for Your Users in Microsoft Entra
Let’s start with enabling Passkey (FIDO2) authentication for your users in Microsoft Entra. This will allow your users to register their YubiKeys as a secure authentication method for accessing Microsoft 365 services.
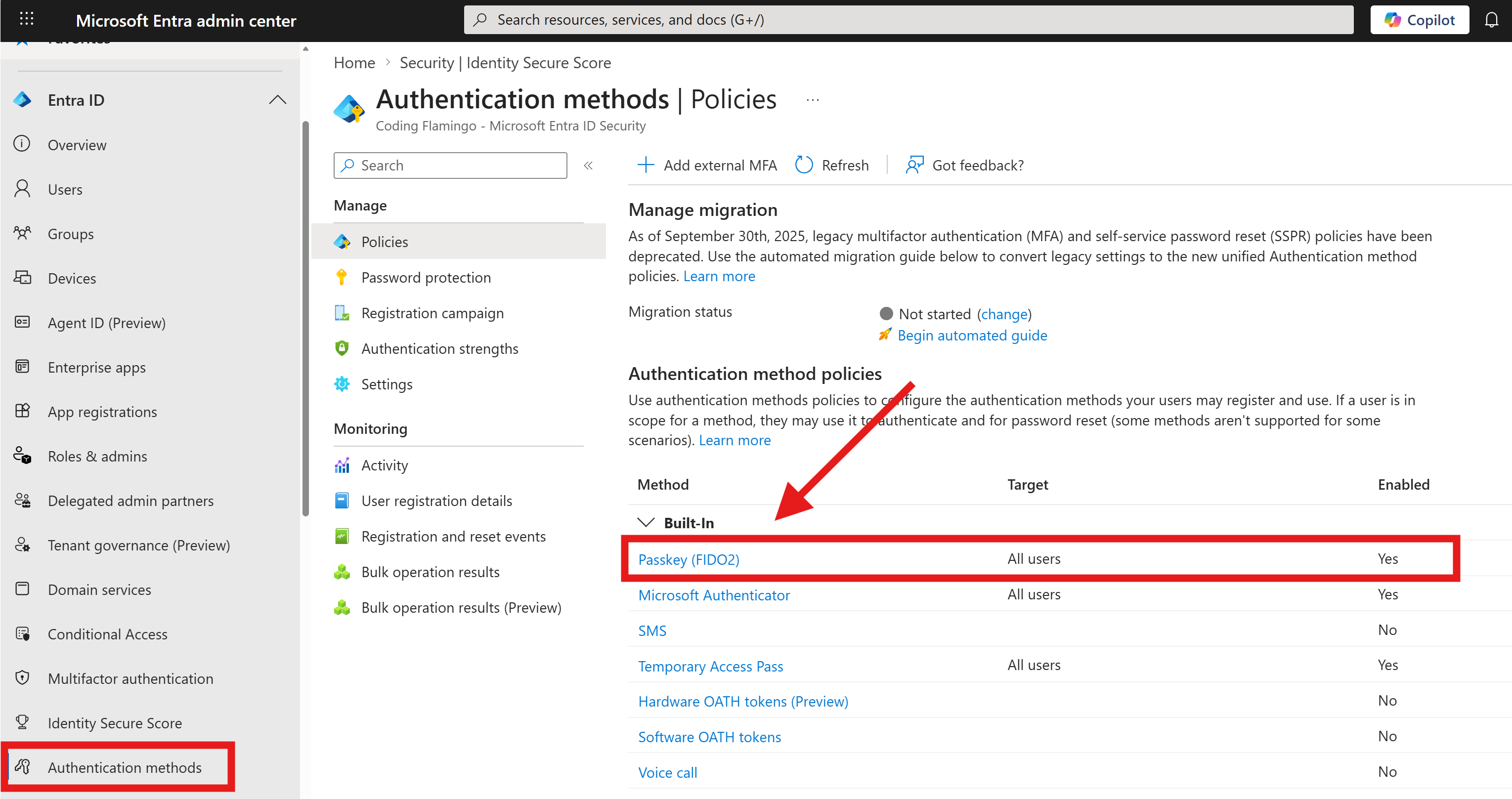
- Sign in to the Microsoft Entra admin center with your administrator account.
- In the left-hand navigation pane, expand Entra ID and click on Authentication methods.
- Enable Passkey (FIDO2) and specify which users can use this method. You may want to start with a pilot group to test the setup before rolling it out to the entire organization.
Step 2: How to Self-Register a YubiKey for Passkey (FIDO2) Authentication in Microsoft 365
Now that FIDO2 authentication is enabled, users can register their own YubiKey for passwordless authentication. This process is straightforward and can be done by the users themselves.
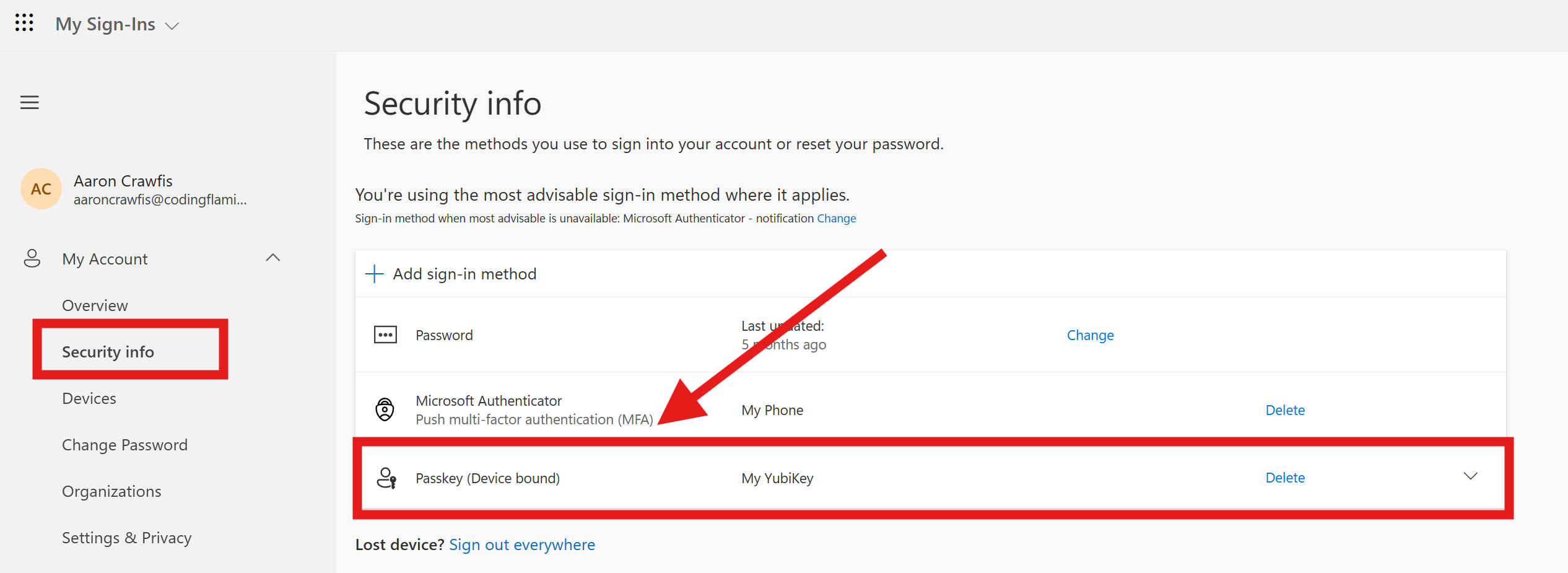
- Navigate to myprofile.microsoft.com.
- From the left-hand menu, select Security info.
- Select + Add sign-in method and choose Security key from the list of options.
- Follow the prompts to plug-in your YubiKey and complete the registration process.
- The YubiKey can now be used for passwordless authentication when signing in to Microsoft 365 services, providing a secure and convenient way to access your accounts without the need for passwords.
While this manual process is great for your most security-conscious users or for testing, we recommend using EZCMS for streamlined management of YubiKeys and certificates. With EZCMS, you can automate the distribution and onboarding of YubiKeys at scale, making it easier to onboard users and manage their credentials without the need for manual registration.
This is especially important when dealing with larger organizations where manual processes can become cumbersome and inefficient. Additionally, you can even move to fully passwordless authentication by eliminating the chicken and egg problem of setting up passwordless authentication.
Step 3: How to Set Up Smartcard (PIV) Authentication for Microsoft 365
In addition to Passkeys (FIDO2), we recommend setting up a smartcard as a reliable alternative when FIDO2 is not available or feasible. This requires setting up a Certificate Authority (CA), either hosted in Azure or on-premises, and integrating the CA certificates within Azure for secure authentication.
Learn more about setting up smartcard authentication in our overview video below:
Integrating EZCMS for Easier YubiKey Management at Scale in Microsoft 365
Incorporating YubiKeys into your Microsoft 365 setup enhances security significantly. By adhering to the outlined steps, you can shield your organization’s data against a multitude of security threats without a complex deployment process. Using EZCMS simplifies the management of YubiKeys, facilitating the distribution and administration of certificates seamlessly.
After configuring the authentication methods, it’s wise to conduct a trial run by registering a YubiKey for personal use and attempting to log in. Tweak Entra settings as needed to balance stringent security measures with user accessibility. Ensure that the setup meets all organizational security standards while remaining user-friendly.
By following these steps, you can effectively secure your Microsoft 365 and Azure environment with YubiKeys, leveraging our EZCMS platform for streamlined management and operational efficiency. Ready to start? Visit our documentation / setup guide for more detailed instructions or schedule a consultation to speak with one of our experts.






