
Is Certificate Authentication Considered MFA?
Are you trying to secure your organization with phishing-resistant credentials but are confused by all the options? You have come to the right place! In this post, I will explain if Certificate-Based Authentication is considered MFA as well as the different types of phishing-resistant credentials you can set up in Entra ID.
What is Multi-Factor Authentication (MFA)?
Multi-Factor Authentication (MFA) is any type of authentication that depends on at least two different types of factors to authenticate a user. This protects against attacks where the attacker compromises one factor but not other factors.
But what do we mean by factors? Authentication factors (all of them, certificate, password, fingerprint, etc.) can be boiled down two three types: something you know (for example, a password, or a PIN), something you have (for example, a YubiKey, smartcard, phone, or PC) and something you are (for example, fingerprint, face ID, iris scan, etc.). So, simply put, multifactor authentication requires two out of the three ways to authenticate.
Is Certificate Authentication Multi-Factor Authentication?
Now to the question of whether certificate authentication is multifactor, and the answer (as with everything in cybersecurity) is: it depends. While certificate-based authentication is one of the most secure ways to authenticate due to the dependency on hard-to-brute-force cryptographic keys, how you protect the private key is what ultimately defines if CBA is MFA. Looking back at the MFA authentication factors, the certificate counts as something you have (the place where the certificate is stored; for example, the YubiKey, the computer if you are pushing it using Intune SCEP, or another MDM or using Windows Hello For Business), if the certificate is protected by another factor such as a PIN (something you know), or a biometric factor such as fingerprint or face ID (something you are), then it is considered MFA. On the other hand, if you can just use the certificate from, for example, the Windows certificate store, then it is considered to be single-factor.
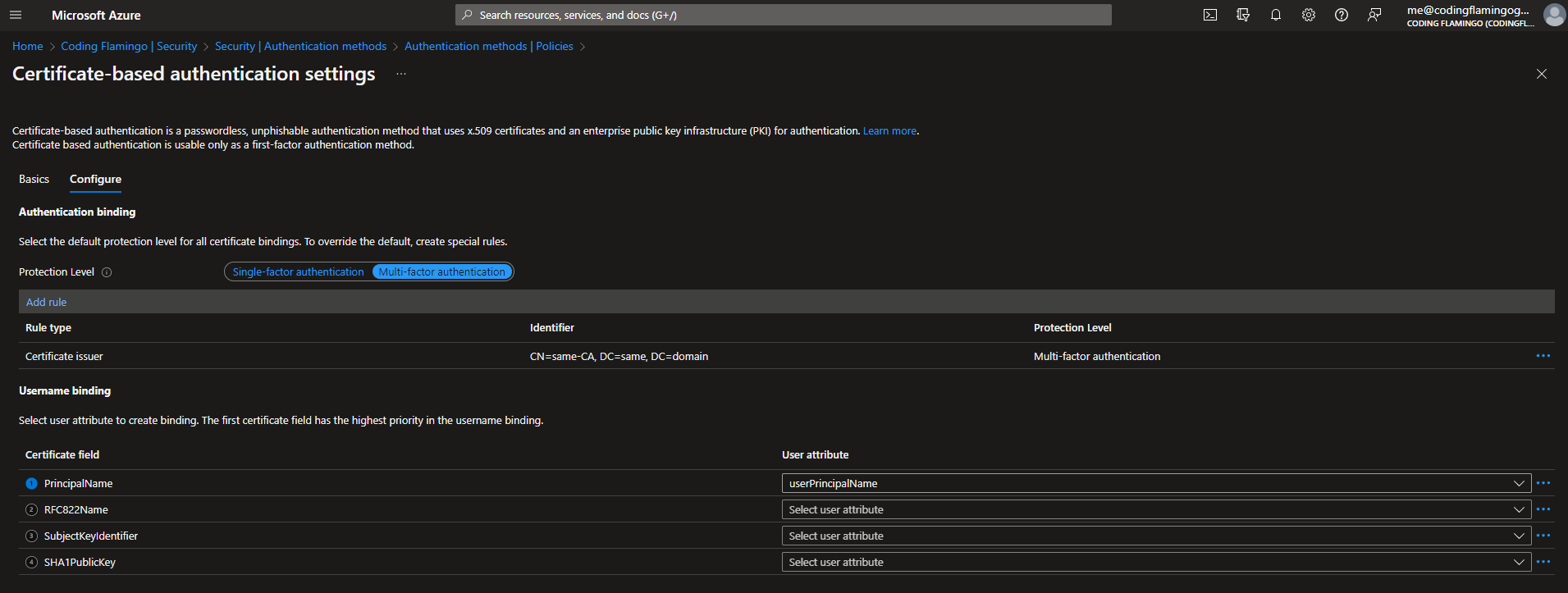
Why Does Entra CBA Have Both Multi-Factor and Single Factor Authentication?
When you are setting up Entra CBA, you probably saw that it has the option to set up certificate authentication as either as a multi-factor authentication method or as a single factor authentication method. The reason for that is because, when you authenticate with a certificate, Entra ID does not know how you are protecting the hardware key of that certificate; therefore, it gives you the ability to define whether to treat the certificates issued by each certificate authority as either a single factor or multifactor authentication.
TL;DR: if your certificates are protected by either a PIN or a biometric factor, set Entra CBA for that CA as multi-factor, otherwise set it as single factor. This will tell Entra ID to ask for a second factor when the user uses a certificate for authentication.
Is Certificate Authentication Phishing-Resistant?
The next question we usually get asked is, “Is CBA phishing resistant?” The answer is mostly yes, but it depends on how you protect your key; if the certificate is protected by a hardware that makes it impossible to export the key (such as a YubiKey, Smartcard, or TPM), then certificate-based authentication is considered phishing resistant since the attacker cannot steal the private key of the certificate.








