
What is SCEP and How Does it Work?
Introduction - How Users and Devices Get Their Digital Identities
In the world of digital security, it’s crucial for every user and device to have a unique digital identity. For user identities, you might be familiar with your username and password. Entra ID, OKTA, and other identity providers create your account, and you use your username and password to log in to your email, work tools, and more. If you work in government or other security-critical industries, you might even have a smart card with a digital certificate that serves as your digital ID instead of a password.
But what about devices? How do their identities work? Just like user accounts, devices also need a way to prove who they are when they connect to a network or access resources. Entra ID and Mobile Device Management (MDM) systems like Microsoft Intune create device identities with unique IDs for every device. For authentication, devices use digital certificates (just like smart cards) which prove their identity and allow them to securely connect to networks and resources.
Both user and device certificates are issued by a Certificate Authority (CA), which is a trusted entity that verifies identities and issues digital certificates. The process of obtaining and managing these certificates can be complex, especially in large organizations with many devices. This is where the Simple Certificate Enrollment Protocol (SCEP) comes into play, providing a streamlined way to automate the issuance and management of certificates for devices. Let’s dive into what SCEP is and how it works!
Automate Certificate Issuance with SCEP
It would be way too much work for IT teams to manually create and manage certificates for every device in an organization. Imagine having to set up a certificate for every single laptop, smartphone, router, and other network devices! This is where Simple Certificate Enrollment Protocol (SCEP) comes in. It automates the process of issuing and managing certificates, making it much easier for IT teams to ensure that all devices have the necessary digital identities to connect securely.
SCEP was created by VeriSign and was published as an Internet Draft by the Internet Engineering Task Force (IETF) in 1999. It was initially built to enable creation and management of X.509 certificates in large-scale environments. At its core, it’s a protocol used to automate the issuance and management of certificates within a Public Key Infrastructure (PKI) environment. SCEP is primarily designed for certificate enrollment on devices such as routers, switches, and other network devices.
How Does SCEP Certificate Issuance Work?
For a digital ID to be valid, it needs a stamp of approval from the Certificate Authority (CA) which creates (issues) it. For more information on certificate authorities, check out our blogs on public vs private CAs and root vs issuing/subordinate CAs. SCEP helps devices and systems talk smoothly with this authority using a web link and a shared code. This makes the whole process quicker and cuts down on manual work.
Here is an easy 4-step breakdown of how SCEP works:
Step 1: Devices Connect to the SCEP Endpoint to Initiate Certificate Enrollment
Certificate Authorities (CAs) set up to issue certificates with SCEP offer a SCEP URL, allowing a device to connect for the purpose of obtaining an enrollment certificate. These endpoints can be hosted internally within your local network (such as an Active Directory Certificate Services (AD CS) SCEP server) or externally in the cloud (such as EZCA, our Azure-based PKI solution). The SCEP URL serves as the gateway for devices to request and obtain certificates from the CA.
Step 2: Devices Present a SCEP Shared Secret
To secure the communication between a device and the SCEP server, a case-sensitive password functions as a SCEP shared secret. It is used for mutual authentication between the Certificate Authority and SCEP server, verifying the identities and domains linked to the CA certificate.
There are two types of SCEP shared secrets: static and dynamic. A static shared secret is a fixed password that remains the same for all devices, while a dynamic shared secret is generated uniquely for each device or enrollment session, providing an additional layer of security. The shared secret is typically distributed to devices through secure channels, such as during device provisioning or through Mobile Device Management (MDM) systems.
Step 3: Devices Generate a SCEP Certificate Signing Request (CSR)
Once the SCEP gateway is established and the shared secret is communicated, the device generates a Certificate Signing Request (CSR). Within the device, a private key + public key pair is created, and the CSR is generated using the public key. The CSR contains information about the device, such as its identity and the public key, which is then sent to the SCEP server for validation and certificate issuance. The private key remains securely stored on the device and is never transmitted to the SCEP server, ensuring that only the device has access to its private key.
Step 4: The SCEP CA Validates and Issues the Certificate
After receiving the CSR, the SCEP CA validates the request by checking the shared secret and ensuring that the device is authorized to receive a certificate. If the validation is successful, the CA issues a certificate based on the information provided in the CSR, by signing the CSR with the CA’s private key. The issued certificate is then sent back to the device, which can use it for secure communication and authentication purposes.
Why is SCEP the Industry Standard for Certificate Enrollment?
SCEP has been a popular choice for certificate enrollment for over two decades. If you’re reading this blog post on your corporate laptop, smartphone, or tablet, chances are that SCEP is being used in the background to manage the certificates that allow your device to connect securely to your company’s network and resources. But why is SCEP so popular, and why is it considered the industry standard for certificate enrollment?
Mostly, it’s because SCEP is free, simple, and widely supported. It provides a standardized way for devices to request and obtain certificates from a CA, without the need for complex manual processes. There’s no need to fix or replace what isn’t broken, and SCEP has been working well for many organizations for years. SCEP is supported by a wide range of devices and operating systems, making it a versatile solution for certificate enrollment in diverse environments. From Windows and Linux to Apple’s iOS and MacOS, SCEP is compatible with various platforms, ensuring that organizations can implement it across their entire device ecosystem.
In today’s cloud-first and hybrid world, SCEP also works well with a large array of Mobile Device Management (MDM) systems like Microsoft Intune, ManageEngine MDM Plus or Jamf use SCEP to help laptops, phones, and tablets connect safely to business tools. Devices like routers, Wi-Fi spots, and VPN tools also use SCEP to get their digital IDs.
How Does SCEP Work with Microsoft Intune?
We have a whole separate blog dedicated to teaching you SCEP is implemented within Microsoft Intune, but here’s a quick overview of how Intune customizes the SCEP process to work with its certificate management system.
If you’re using Intune, you’re probably trying to move away from legacy on-premises technology and move your security to the cloud. To create a secure and compliant CA for Intune, you can use EZCA, the Azure-based PKI. EZCA connects to Intune using their third-party APIs and enables you to create SCEP certificates for Intune without the overhead of managing a complex PKI.
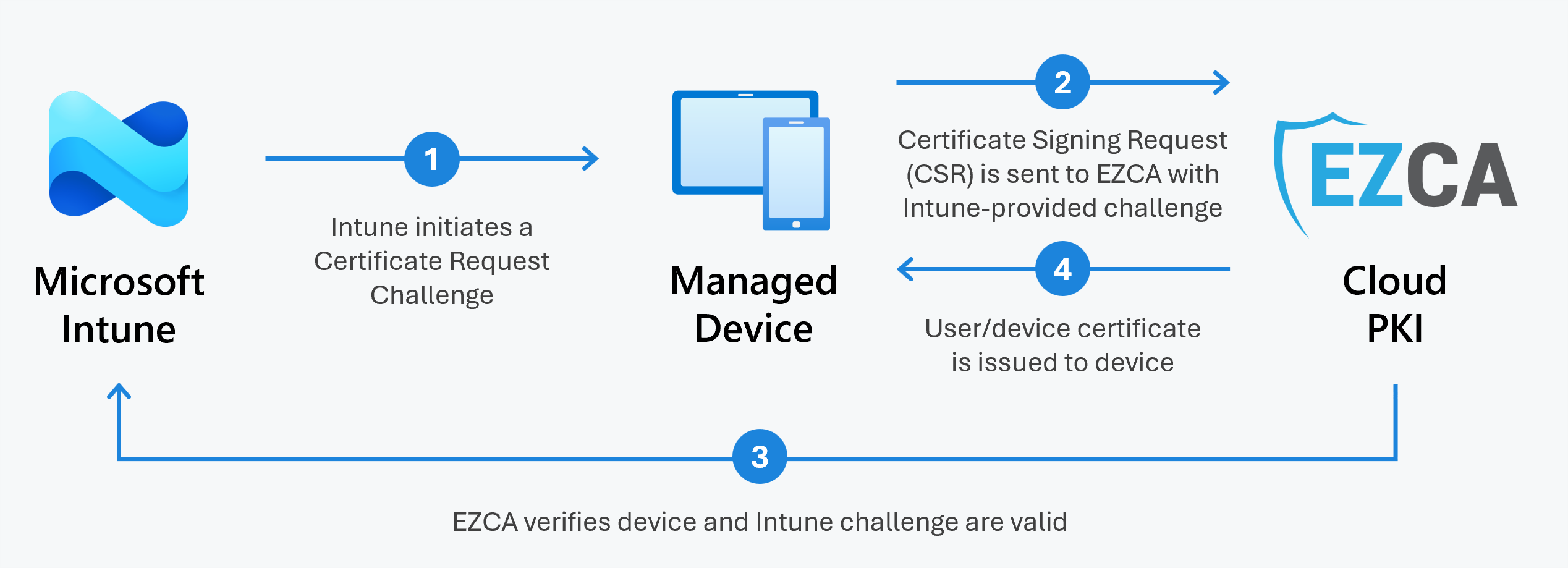
Intune starts the certificate creation workflow by sending a challenge to the client device. Then, the device creates a private key and a Certificate Signing Request (CSR) and sends it with the challenge to EZCA. EZCA then validates with Intune whether this request is valid; once Intune approves the request, EZCA creates the certificate and Intune installs the resulting certificate in the device.
Conclusion - Why SCEP is Essential for Certificate Management
Certificates are excellent when it comes to digital security, but obtaining and managing them can be a nightmare. Doing this manually is painfully slow and leaves plenty of room for error. Think about it: setting up a single certificate might take hours. Now imagine doing this for thousands of devices! If done manually, organizations risk system outages, security breaches, and cyber-attacks. Plus, certificates can be forgotten or mismanaged, leading to more issues.
That’s where SCEP shines. It automates getting and setting up these digital ID cards, removing the need for human work. This means fewer mistakes, less risk, and cost savings for businesses.
While SCEP certainly has its advantages, it’s important to remember that, like any technology, it needs to be configured correctly and managed properly to provide maximum benefit. Negligence could lead to security vulnerabilities and operational inefficiencies. For instance, using SCEP in conjunction with additional protocols or security layers can provide enhanced security. However, organizations should be aware of these limitations when deploying SCEP and ensure they are following best practices for secure certificate management.
To learn more about how EZCA can help you create a secure Intune CA and create SCEP certificates for Intune, schedule a FREE consultation with one of our ex-Microsoft PKI experts today!
Schedule a Free Consultation







