FIDO2 vs. Smartcard Authentication
What is the Difference Between FIDO2 and Smartcard Authentication?
In today’s digital world, secure authentication is more important than ever. With the rise of online threats and cyber-attacks, organizations need to ensure that their systems and data are protected from unauthorized access. To do this, they often use authentication methods such as passwords, two-factor authentication (2FA), or biometric authentication; however, these methods can have their own drawbacks, such as the need for additional hardware or the potential for users to forget or lose their credentials.
One solution to this problem is the use of FIDO2 and smartcard authentication. These methods are considered unphishable credentials since they provide strong secure authentication without the need for passwords, making it impossible for a user to unwillingly give away their credentials. In this article, we will explain the difference between FIDO2 and smartcard authentication and discuss the benefits and potential drawbacks of each.
What is Smartcard Authentication?
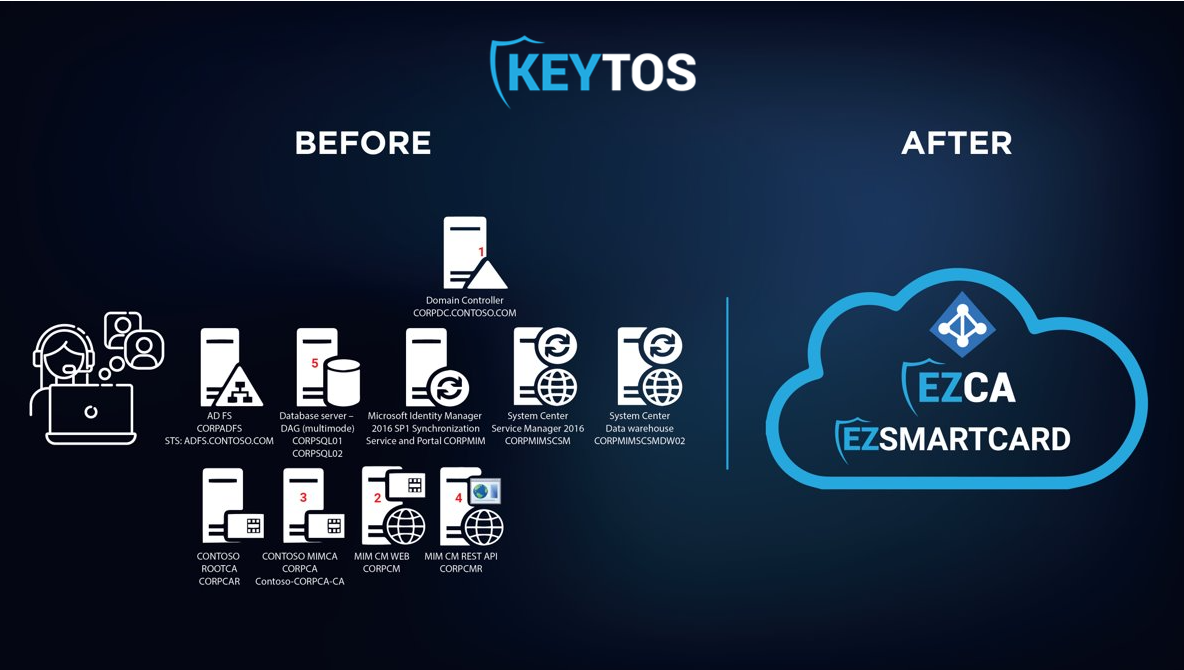
Smartcard authentication is the first passwordless authentication method ever created, it is based on X509 certificates and has been used by governments around the world for over 2 decades. Smartcard authentication is the most secure authentication method available today; however, it is also the most complex to implement and manage. In the past, stamps with 10+ servers were required for a simple smartcard authentication solution. To solve this complexity the FIDO alliance came up with FIDO2.
What is FIDO2?
FIDO2 is a new authentication standard that was created by the FIDO Alliance. It is based on public-key cryptography and provides strong authentication without the need for passwords. FIDO2 is a much simpler solution than smartcard authentication, since it does not require all the infrastructure that smartcard authentication requires since instead of using X509 certificates the cloud provider registers the specific key id of the public key of the hardware token and does key based authentication.
Azure CBA Making SmartCard Authentication Easy
During the US executive order 14028, the government deemed that while FIDO2 is good for most scenarios, it did not meet the highest security requirements of the government due to it’s decentralized key management (instead of revoking one certificate, the key must be removed from all providers that accept that key), so they recommended the use of smartcard authentication for the highest security scenarios. This forced the cloud providers to improve the ease of implementation of smartcard authentication, and now smartcard authentication is easier than ever to implement.
Smartcard Authentication vs FIDO2 Which is Better?
If you are using Azure, you might be inclined to use FIDO2 since it is the more popular passwordless authentication method. However, as we talked about in the article about FIDO2 for on premise AD, FIDO2 is not compatible with all legacy systems. Our recommendation is to obtain a hardware token such as the Yubikey 5 series keys that support both FIDO2 and smartcard authentication, this way you can use FIDO2 for most scenarios and smartcard authentication for the scenarios where FIDO2 is not supported. Luckily for you, we have created a step by step guide on how to implement smartcard authentication in Azure to be able to enable FIDO2 credential and smartcard onboarding transparent to the user by using an azure based passwordless CMS enabling to setup industry leading passwordless authentication without any extra infrastructure.
Ready to Go Passwordless?
Passwordless is not just more secure but also easier for the users. Watch the webinar below where we talk with Microsoft about how you can go passwordless with Azure and EZCMS.








