How-To: Automate GlobalSign MSSL Certificate Lifecycle for Free
Prerequisites
- Registering the application in your tenant
- Selecting a Plan (This is only available in premium plans)
Overview - How to Automate GlobalSign MSSL Certificate Lifecycle For Free
If you are happy with EZCA’s certificate management capabilities and are looking to implement the same capabilities for your public SSL certificates, EZCA can help you with that. EZCA has a built-in integration with GlobalSign MSSL platform that allows you to issue and automate the lifecycle of your public SSL certificates, the best part? If you are a EZCA premium subscriber, there is no extra cost!
How To EZCA to GlobalSign MSSL
The first step to automating your GlobalSign MSSL public certificate issuance is to connect EZCA to GlobalSign. The following steps will guide you through the process of connecting EZCA to GlobalSign MSSL.
-
Navigate to your EZCA instance and select “Settings”
-
Login with an account that is registered as a PKI Admin in EZCA.
-
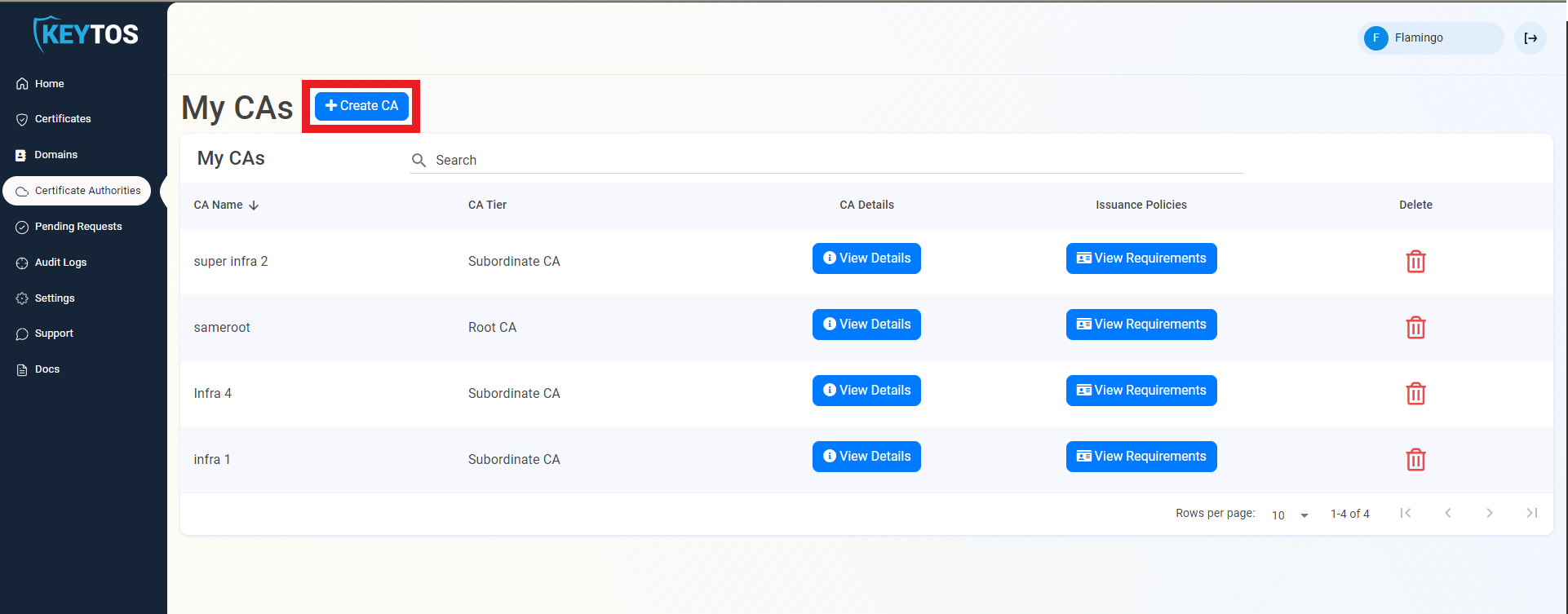
Navigate to Certificate Authorities.
-
Click on the “Create CA”
-
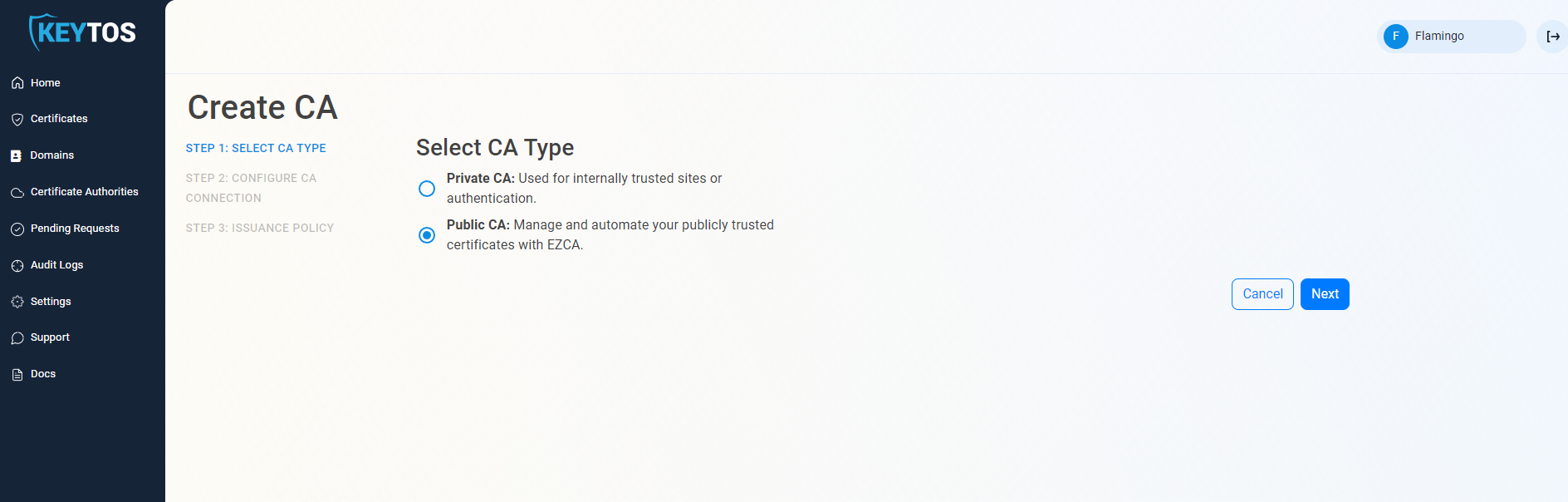
Select “Public CA”
-
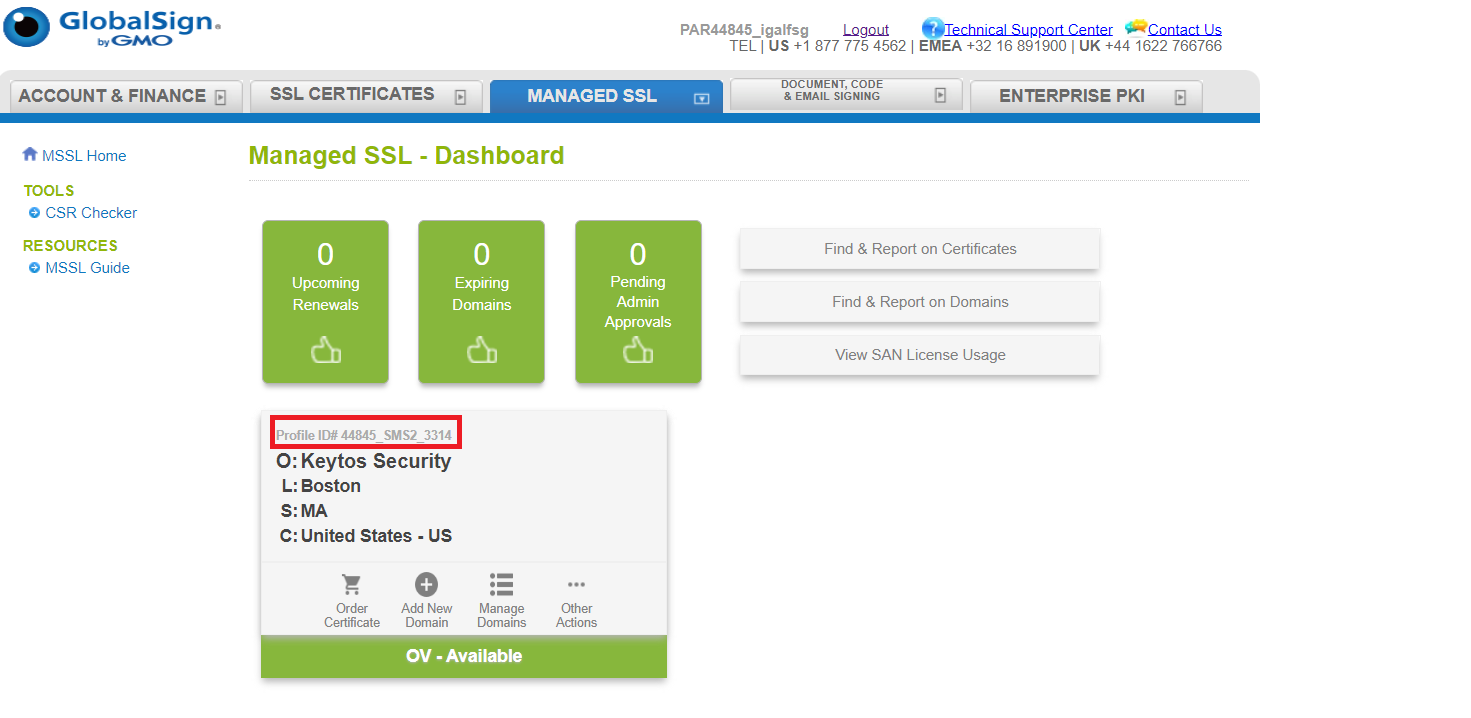
Select “GlobalSign”
-
Enter your MSSL Profile ID. This profile ID can be found inside your globalsign account. under the managed SSL tab.
-
Now you need to enter the GlobalSign credentials that you have assigned to EZCA.
NoteTo Avoid security breaches or outages and to maintain separate accounts we highly recommend creating a special login for EZCA and not using your own credentials.
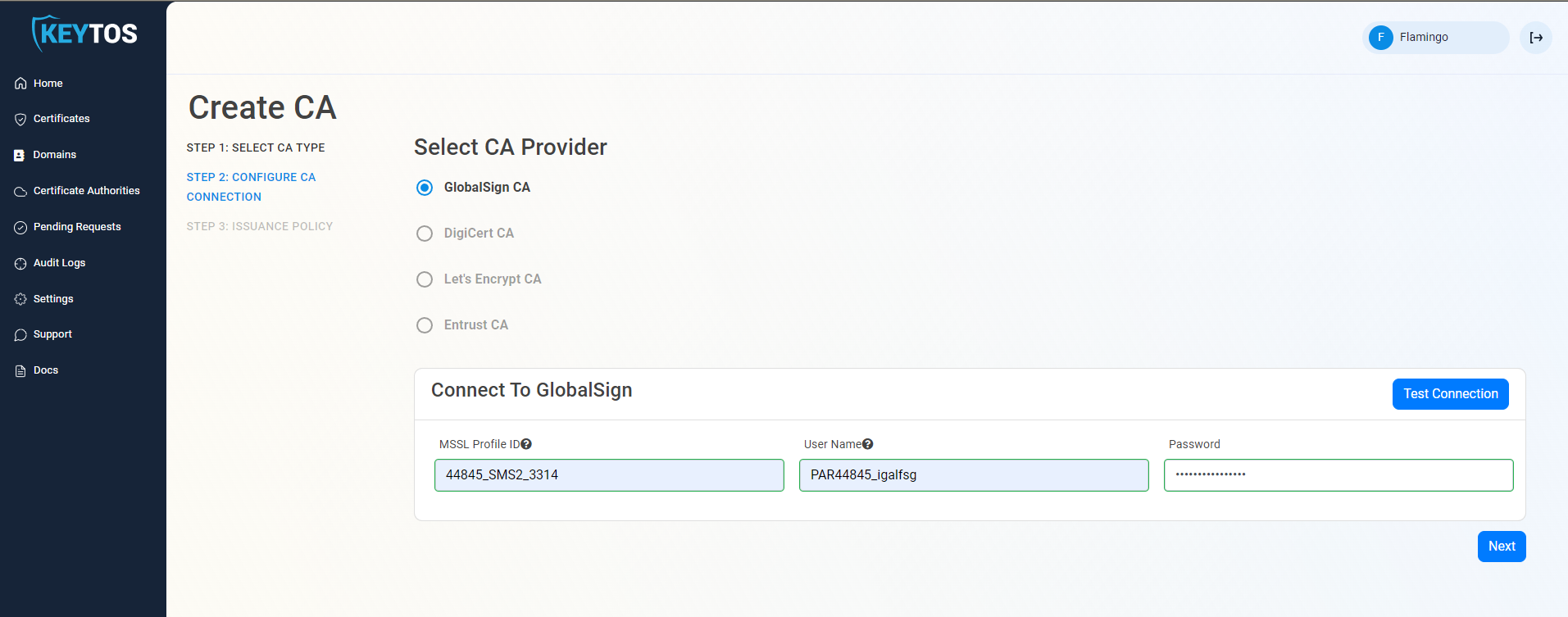
-
Click on “Test Connection”. Once the connection is successful, click on “Next”.
-
While all PKI administrators will get emails regarding this CA connection, we also allow for you to add an extra email such as your team’s distribution list where we will also send the alerts. Enter the email address under “Notification Email”
-
Below you can see the list of all the domains that available for this CA. You can select the ones you want to enable by clicking the “manage domain” button.
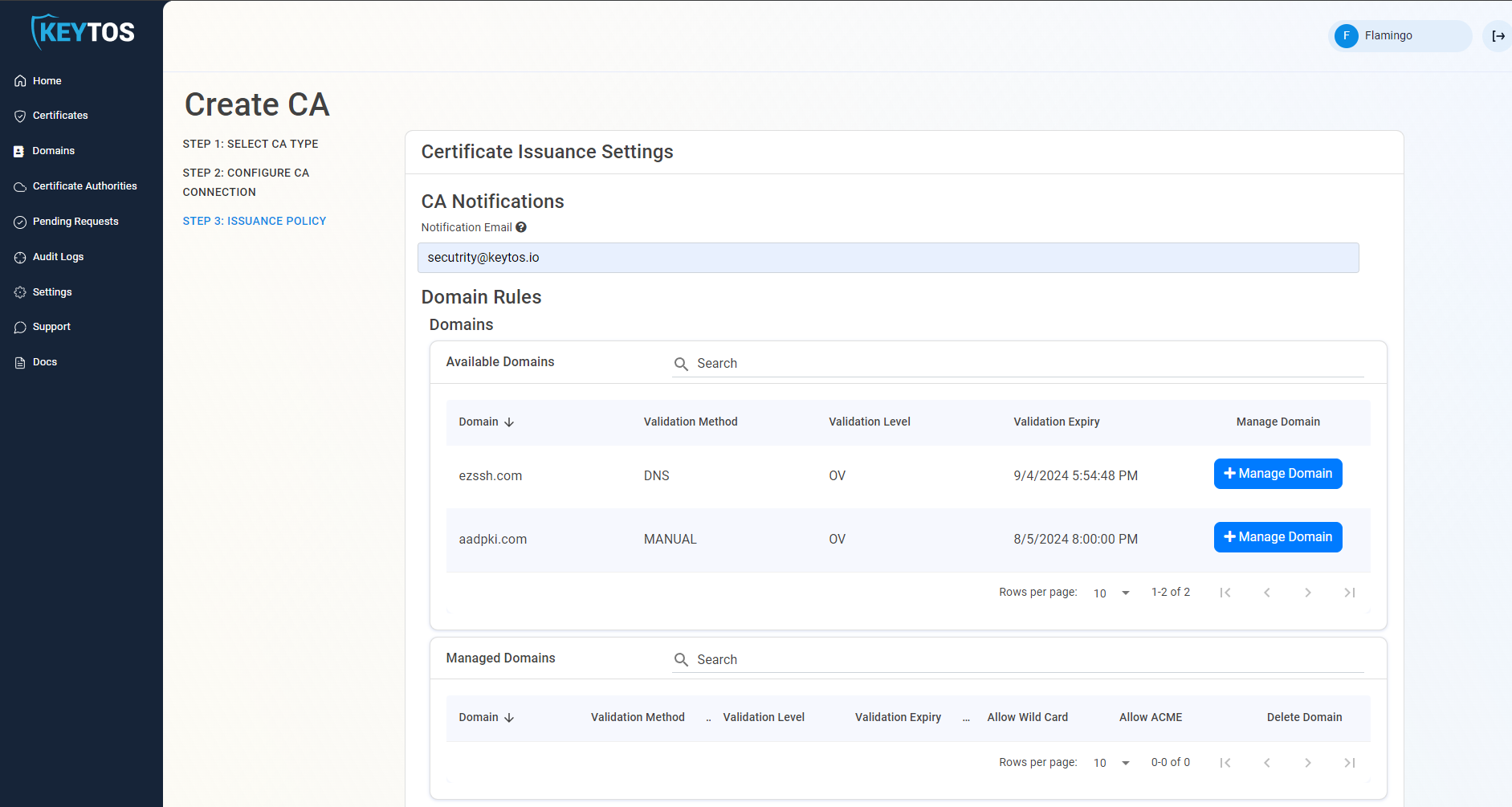
-
Once you have added the domains that you want EZCA to manage, you can setup your issuance rules.
Certificate Issuance Rules
To enable more granular control who can request domain ownership in EZCA, we created to extra knobs PKI administrators can adjust to control domain ownership.
- Require domain registration approval. This option enables PKI administrators to set a group of approvers that must approve each domain registration before a user or group of users are registered as domain owners.
- To enable this option select the “require approval” option.
- Enter the users or AAD groups that can approve domain requests.
- The second way PKI administrators can control the registration of domains is to only allow specific users to request domains. This option enables PKI administrators to set a list of users that can request domains for this CA.
- To enable this option deselect the “Allow all users” option.
- Enter the users or AAD groups that can register domains.
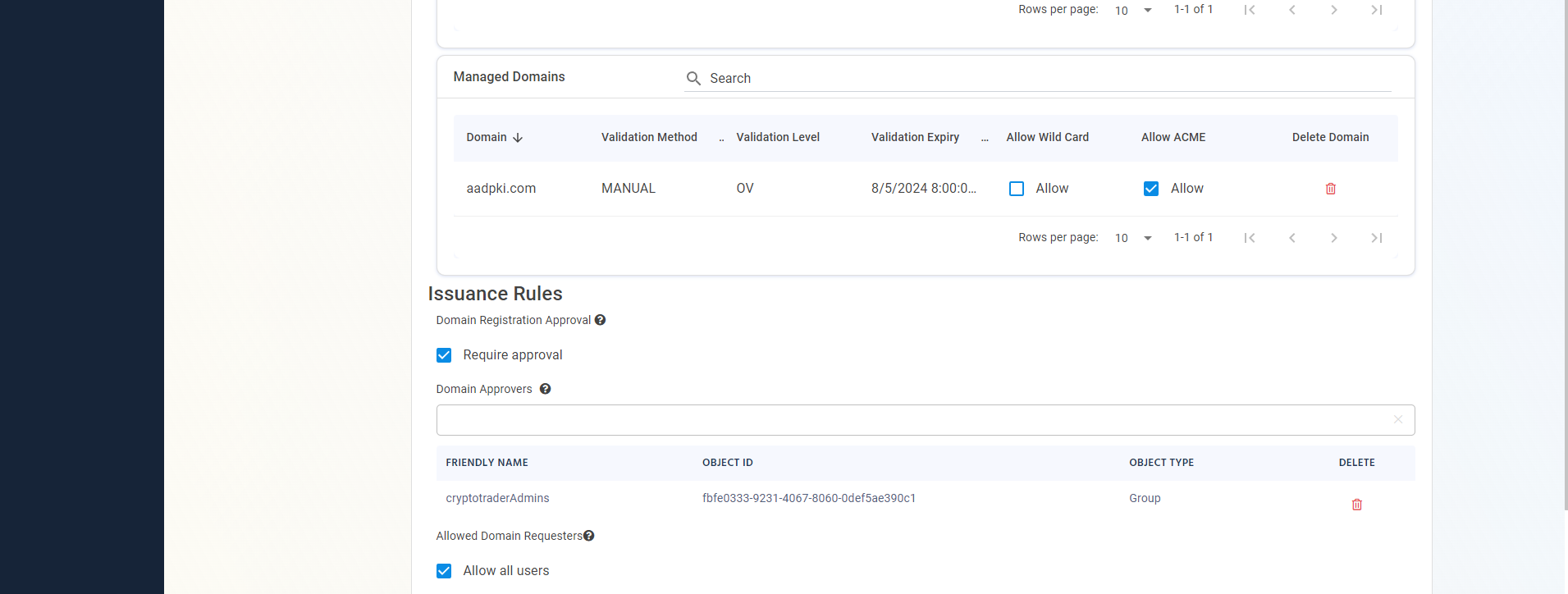
- Select the issuance rules you require.
Certificate Lifecycle
The last step before creating your GlobalSign MSSL connection, is to setup your maximum certificate validity period. This is the maximum validity period that EZCA will allow for certificates issued by this CA. By default this is set to 90 days which is the maximum validity period allowed by the new Google requirement for 2024. However, if you are still not ready for this change you can set it to the number of days you would want your certificates.
GlobalSign MSSL platform does the management in months, so for a year, instead of 365 days, you would need to enter 359 days.
Connect to GlobalSign MSSL
Now we are ready to connect your CA to EZCA. Click on “Create CA” and your CA will be created.
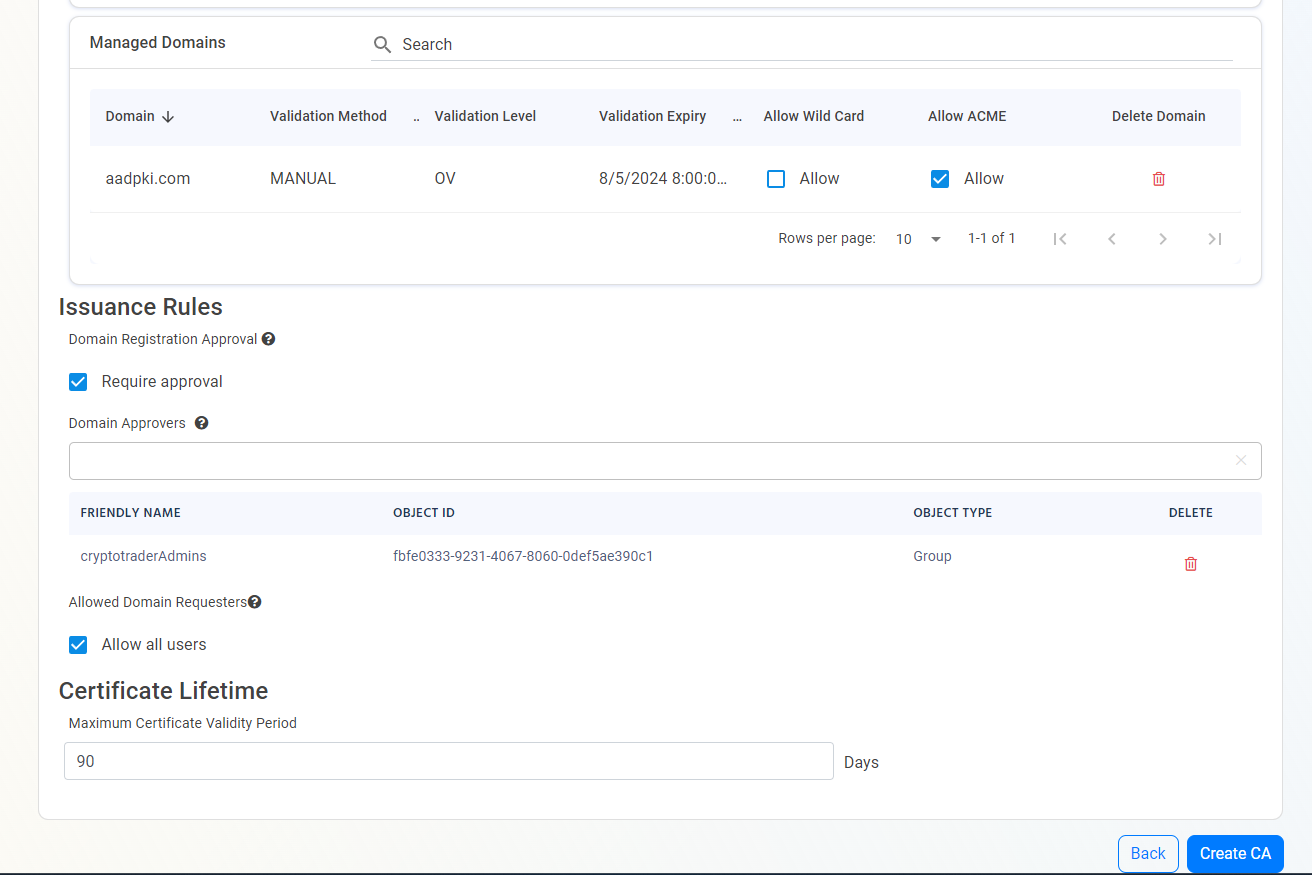
- Now that your CA is connected, you are ready to register your first domain owner and issue your first certificate.