How-To: Create Cloud RADIUS Network Policies for Certificate Authentication
Prerequisites
- The Keytos Entra applications are registered in your tenant
- You have an active EZRADIUS plan
- You are a Subscription Owner or Network Administrator on your EZRADIUS plan
How to Create Cloud RADIUS Network Policies - Video Tutorial
Introduction to Managing Cloud RADIUS Network Policies in EZRADIUS
The Policies page in EZRADIUS allows you to create and manage your Cloud RADIUS network policies. Each policy defines the conditions under which a user or device can connect to your network, including authentication methods, accepted certificate authorities, and access policies.
Visit the Manage RADIUS Policies guide to learn more about the Policies page layout and features.
How to Create Cloud RADIUS Network Policies with Certificate Authentication
Now that you are familiar with the layout of the Policies page in EZRADIUS, you can set up a new RADIUS network policy that uses Certificate Authentication for authentication. The following steps will guide you through the process.
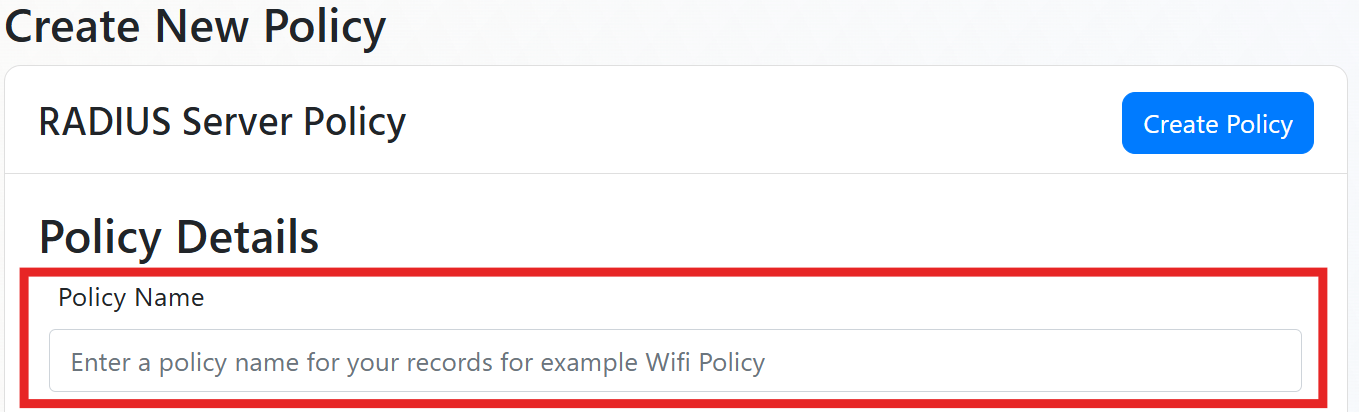
Step 1: Name Your RADIUS Server Policy
Begin by entering a friendly name for your RADIUS server policy. This name is for your records to help you identify the policy later. Behind the scenes, EZRADIUS will create a unique identifier for the policy, so feel free to choose a name that makes sense to you.
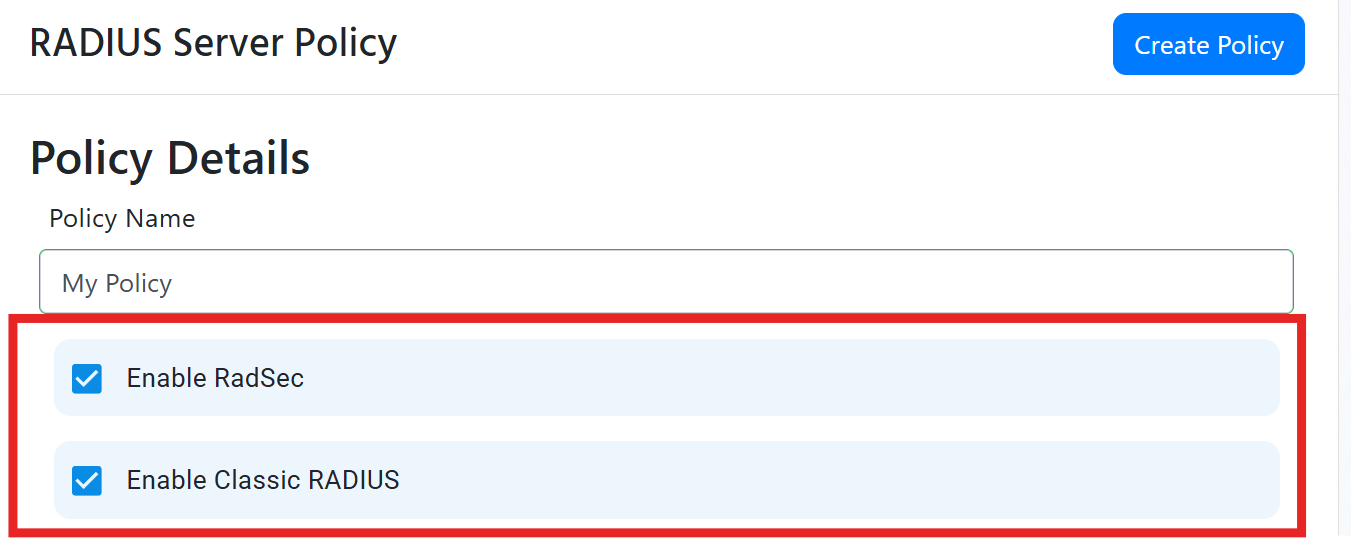
Step 2: Enable RadSec and/or Classic RADIUS
Next we have to enable which authentication methods you are going to use, you can use RadSec, Classic RADIUS, or both.
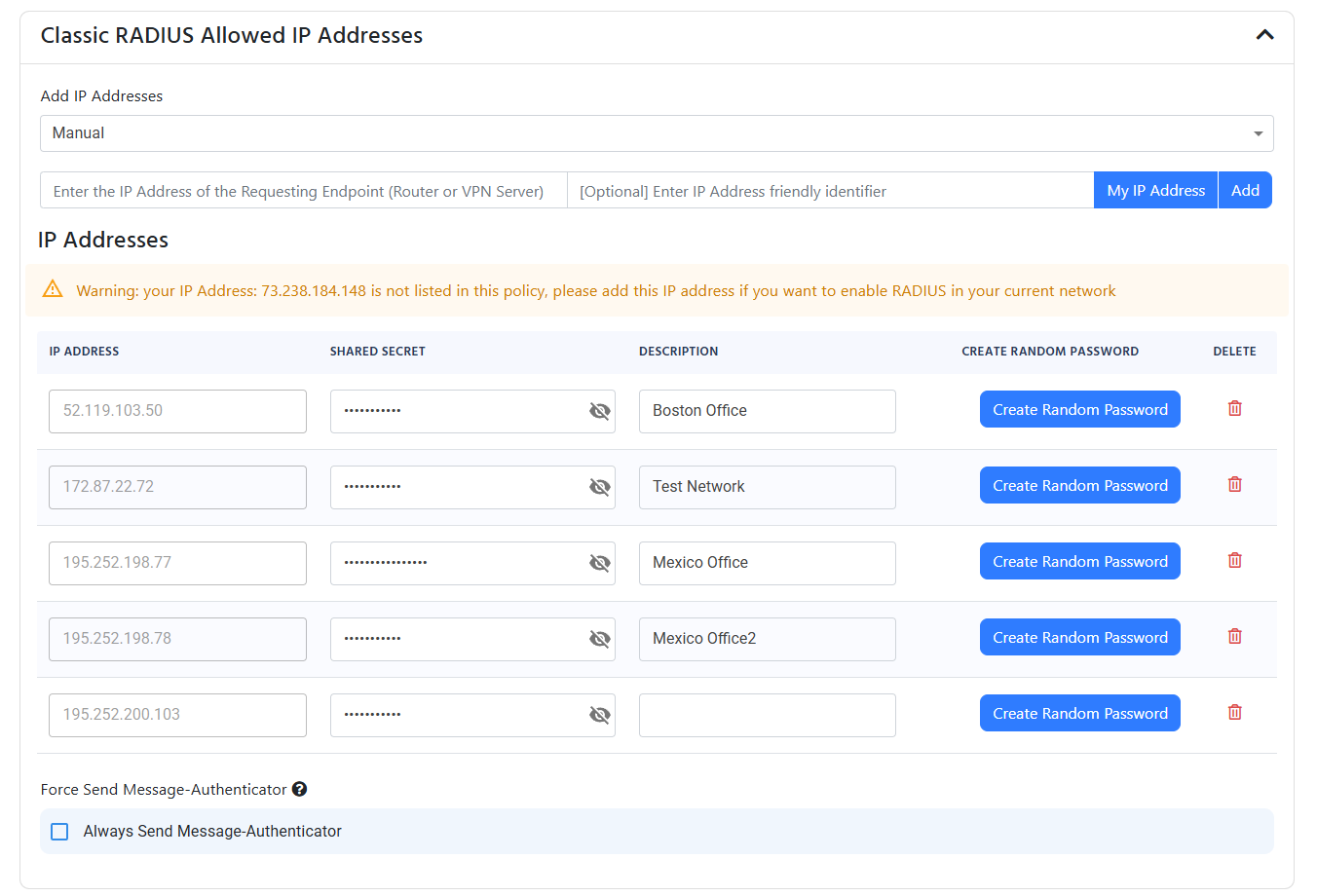
How to Set Up Classic RADIUS for Cloud RADIUS
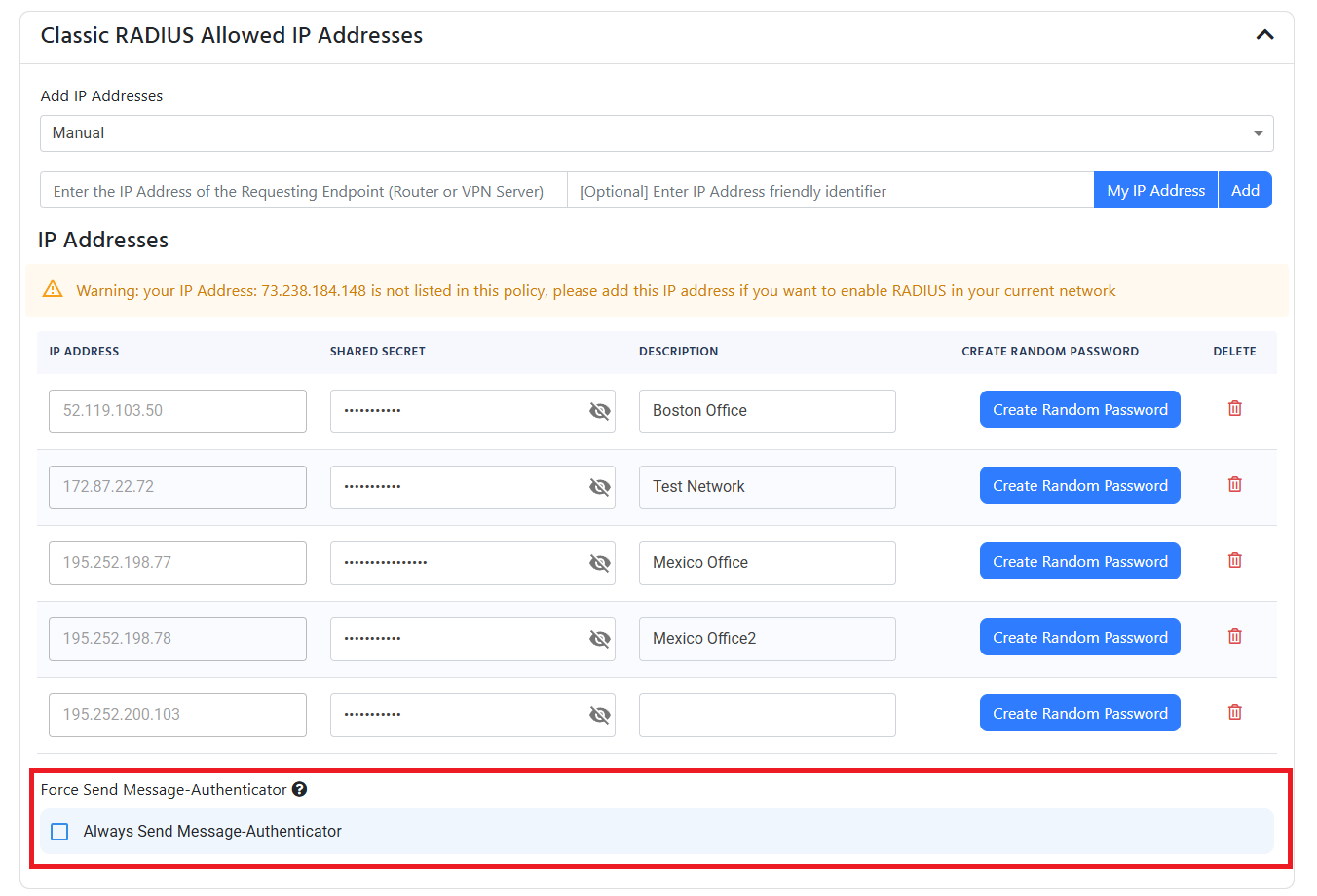
For Classic RADIUS, you need to specify the IP addresses of your RADIUS clients (e.g., access points, switches). These are the public IP addresses that will be allowed to communicate with your Cloud RADIUS server. We also use these IP addresses to attribute RADIUS requests to the correct policy for audit logs and reporting.
When specifying an IP address, make sure to use the external IP address for your network. It should not start with 192.168.***, 10.0.***, 172.16.***, or any other private IP address range. If you’re unsure, visit What is my IP to find your public IP address, or click the My IP Address button in the EZRADIUS portal to automatically add your current public IP address if you’re connecting from within your network.
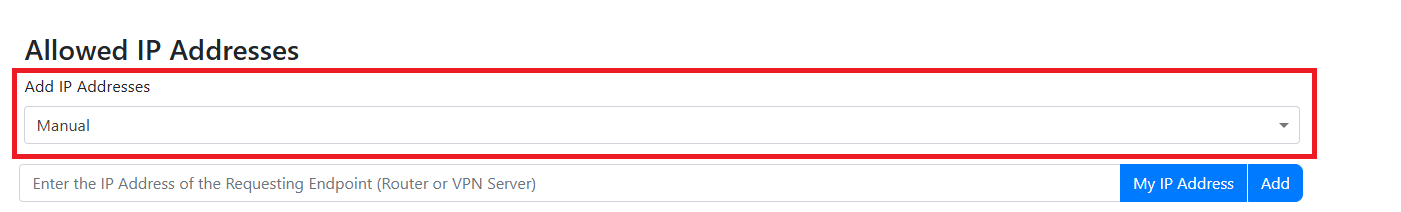
There are two ways to add IP addresses to your RADIUS policy: manually adding them one by one or uploading a CSV file for multiple IP addresses.
- Select “Manual” from the dropdown.
- Enter the public IP address of your router or VPN server.
- Provide a friendly name for the IP address (for your records).
- Click Add to add the IP address to the list of allowed RADIUS clients.
- A randomly generated shared secret will be created for the IP address. You can change this shared secret if needed. Note that every IP address must have a unique shared secret.
- Repeat the process for each additional router or VPN server you want to add.
If you have multiple IP Addresses you can add them using a CSV file (if you have an CIDR range and want to convert it to IP range, use this site).
CSV File Format
The CSV file must have the format IP Address,Friendly Name,Shared Secret, without headers. For example, a CSV file with two IP addresses would look like this:
12.12.12.12,First Name,SharedSecret1
12.12.12.13,Second Name,SharedSecret2
Make sure you do not include headers in the CSV file, as this will cause an error during the upload process.
Uploading the CSV File
- Begin by creating a CSV file with your IP addresses, friendly names, and shared secrets and saving it to your computer.
- Drop down the ‘Add IP Addresses’ menu and select ‘CSV File Upload’.
- Either drag-and-drop your CSV file into the upload area or click on the area to browse and select your CSV file.
(optional) Always Send Message Authenticator
Depending on your networking device, you may need to enable the “Always Send Message Authenticator” option. This is required by some devices to ensure proper RADIUS communication, especially for devices from Fortinet.
If using Fortinet devices, After Fortigate 7.2.10 you will need to enable the “Always Send Message Authenticator” option in the RADIUS server settings.
How to Configure RadSec for Cloud RADIUS
If you enabled RadSec, you have to add a certificate authority or certificate that is accepted by the RADIUS server. This is dependant on your networking device (for example, if you are using a Cisco device, you will need to add the Root CA of the certificate that signed the certificate of the device. If you are using a Ubiquiti device, it allows you to upload your own certificate from your CA).
Each EZRADIUS policy can only be claimed by one RadSec CA. If you are a Managed Service Provider (MSP) or have multiple customers sharing a public IP address, each customer must use a distinct CA in their EZRADIUS policy. EZRADIUS identifies which policy a RadSec request belongs to by the CA that signed the client certificate — so two policies using the same CA cannot coexist. The recommended MSP topology is to issue each customer’s network devices certificates from a separate CA (one CA per EZRADIUS policy). All customers can share the same public IP and EZRADIUS region — EZRADIUS routes each request to the correct policy based on the CA used by the connecting device.
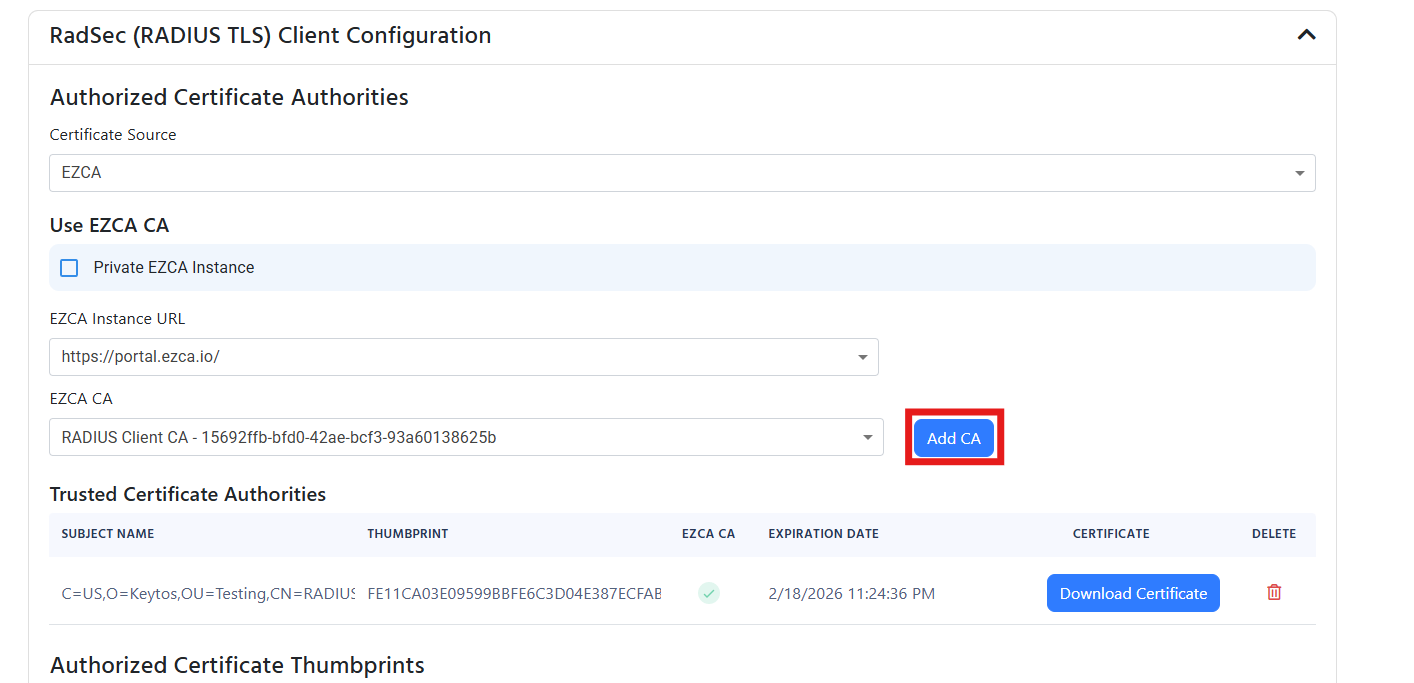
Add Certificate Authorities to RadSec Using EZCA
If your RadSec certificate is issued by your EZCA Certificate Authority, then you can easily add the CA to the cloud RADIUS server by:
- From the “Certificate Source” dropdown, select “EZCA”.
- Under the “EZCA Instance URL” dropdown , select your EZCA instance.
- Under the “EZCA CA” dropdown, select the CA you want to add.
- Click Add CA to add the CA to the RADIUS server.
- Your CA will now be listed under the “Trusted Certificate Authorities” section.
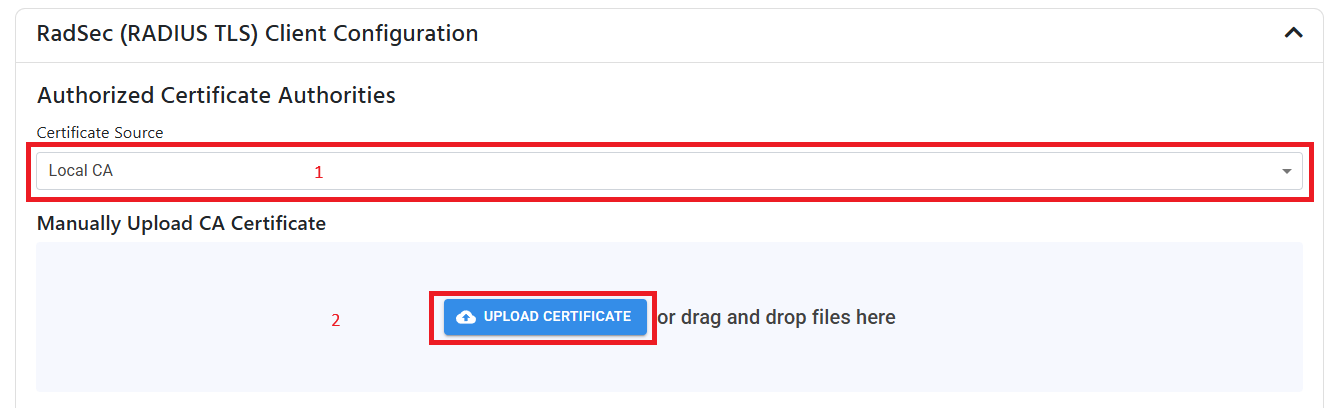
Add Certificate Authorities to RadSec Using 3rd Party CA
If your device uses a certificate from a 3rd party CA, you can add the CA to the cloud RADIUS server by:
- From the “Certificate Source” dropdown, select “Local CA”.
- Upload your CA certificate in PEM format.
- Your CA will now be listed under the “Trusted Certificate Authorities” section.
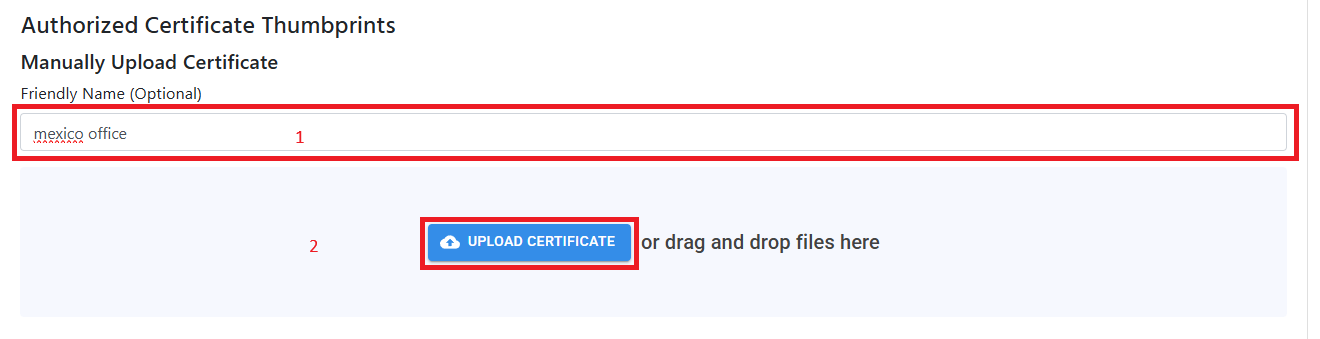
Add Self-Signed Certificate to RadSec
If your networking device only supports self-signed certificates for RadSec, you can upload the single certificate to your cloud RADIUS policy by:
- Leave the “Authorized Certificate Authorities” section empty. You don’t need to add any CAs for self-signed certificates.
- Under “Authorized Certificate Templates”, enter a certificate Friendly Name (This is just for your records, useful if have multiple locations).
- Upload the certificate in PEM format.
- Your certificate will now be listed under the “Trusted Certificates” section.
Step 3: Add Certificate Authorities to RADIUS for Certificate Authentication
If you are only using username and password from Entra ID, please skip this part and move to the server certificate section. This step is only needed if you are using certificate authentication for some of your users or devices.
If you are using Certificate Authentication (highly recommended if using an MDM due to the extra security and seamless user experience), you must add your trusted Certificate Authorities to the RADIUS policy.
If you are using EZCA, our cloud based Certificate Authority, there is a built-in integration to select your CA in just a few clicks. if you are using a different CA, you can upload the CA certificate in PEM format.
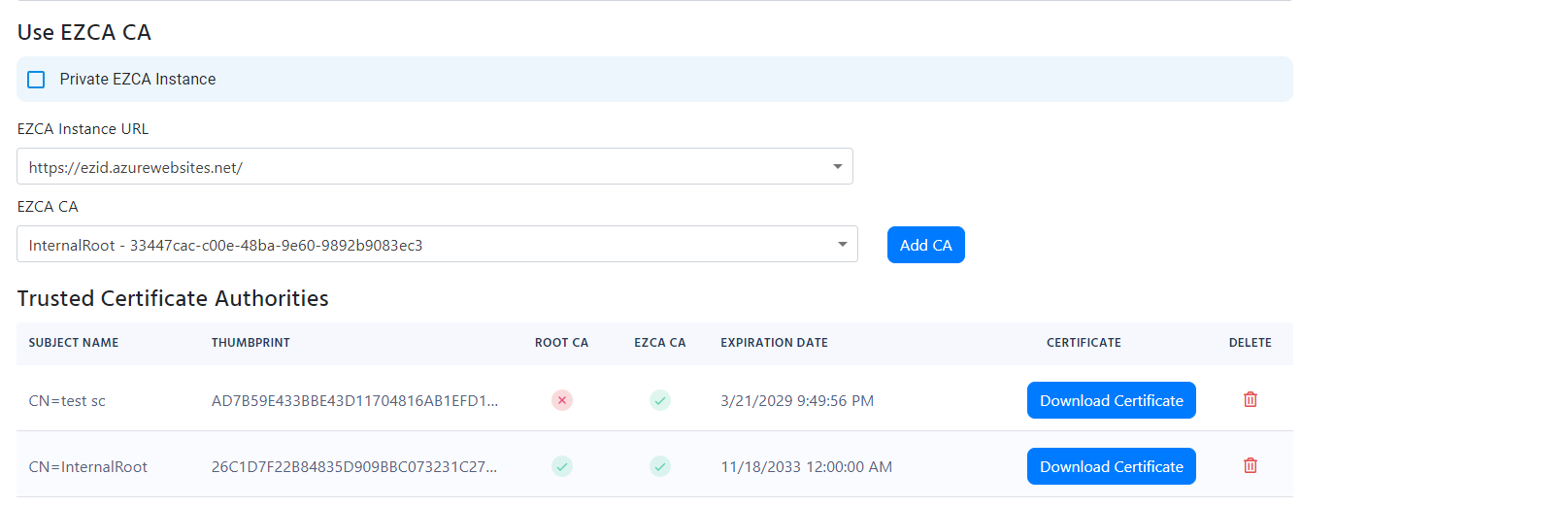
Add Certificate Authorities to RADIUS Using EZCA
- From the ‘Certificate Source’ dropdown, select ‘EZCA’.
- If you’re using a private EZCA instance, check the ‘Private Instance’ checkbox and enter your EZCA URL.
- Under the ‘EZCA CA’ dropdown, select your EZCA CA.
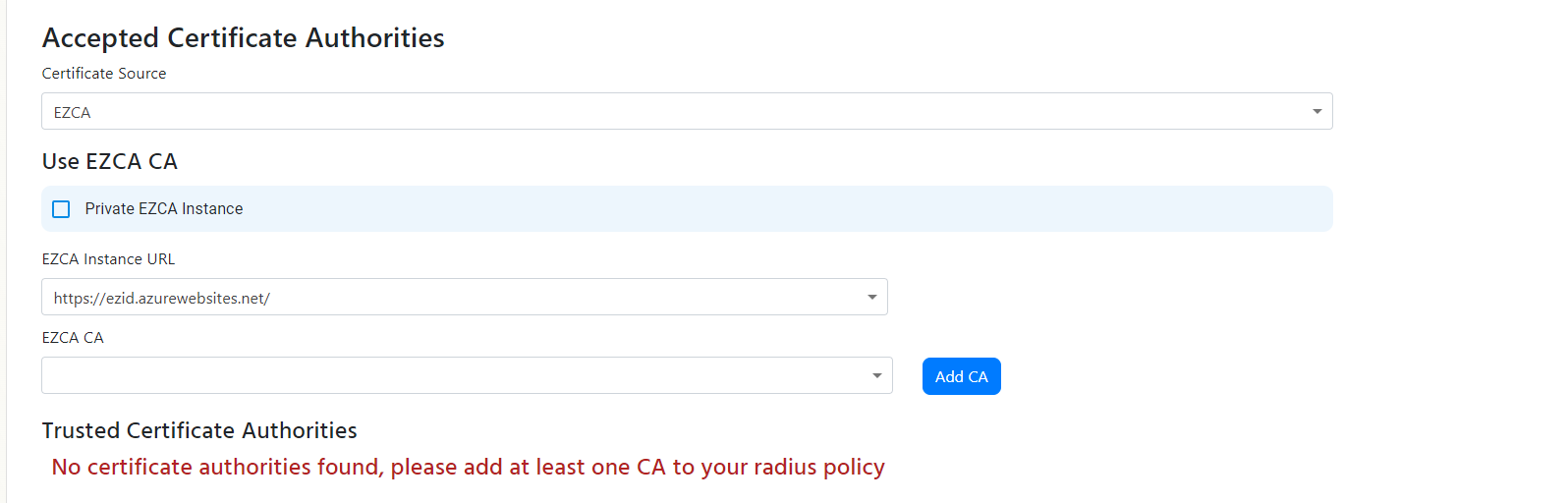
- Click the Add button to add the CA.
- If you have a 2 tier hierarchy, add both your Root CA and your Issuing CA.
- You should now see your CA(s) listed under your ‘Trusted Certificate Authorities’:
Add Certificate Authorities to RADIUS Using 3rd Party CA
- From the ‘Certificate Source’ dropdown, select Local CA.
- If you are uploading a Root CA, check the Root CA checkbox. If you are uploading an Issuing CA, leave the checkbox unchecked.
- Click on the Upload Certificate button and select the CA certificate in PEM format.
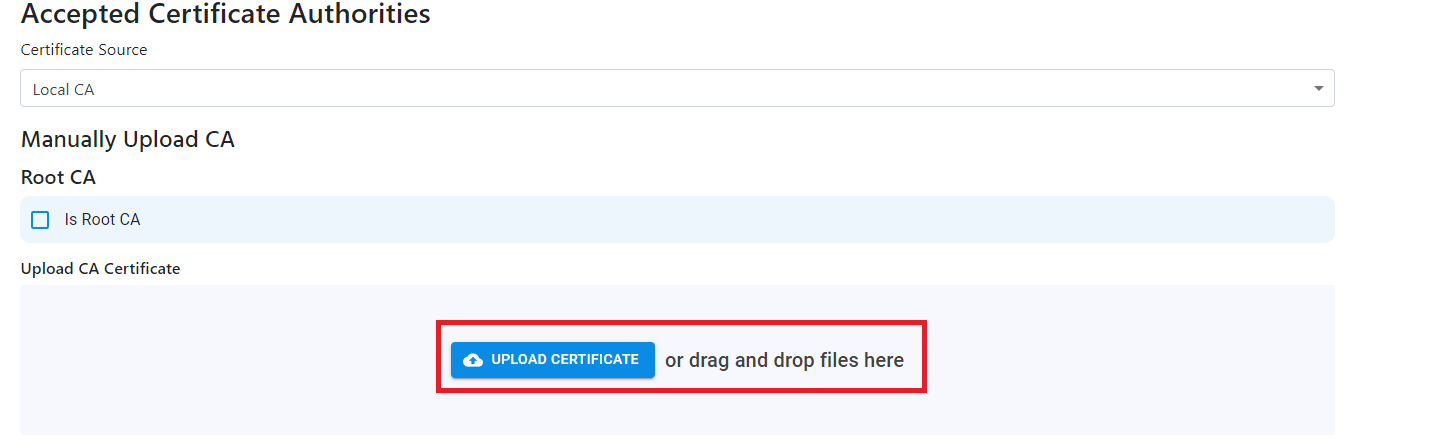
- If you have a 2 tier hierarchy, add both your Root CA and your Issuing CA.
- Repeat the process for each additional CA you want to add.
Step 4: Add Server Certificate to RADIUS
A certificate is required to uniquely identify the RADIUS server to the devices connecting to the network. Without it, your clients will not be able to connect and will return errors. There are three ways to add a server certificate:
- Use a free, auto-generated certificate
- Use EZCA to create and manage the certificate
- Upload a certificate from a 3rd party CA.
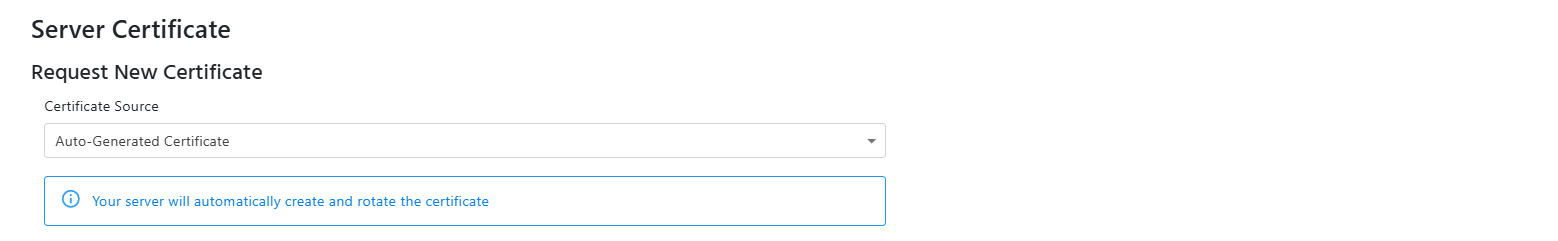
Create a Free Certificate with EZRADIUS’ Integrated Certificate Authority
If you do not have a your own CA, you can use EZRADIUS’ integrated CA to create a free certificate. The certificate will be automatically created and renewed by EZRADIUS.
- From the ‘Certificate Source’ dropdown, select Auto-Generated Certificate.
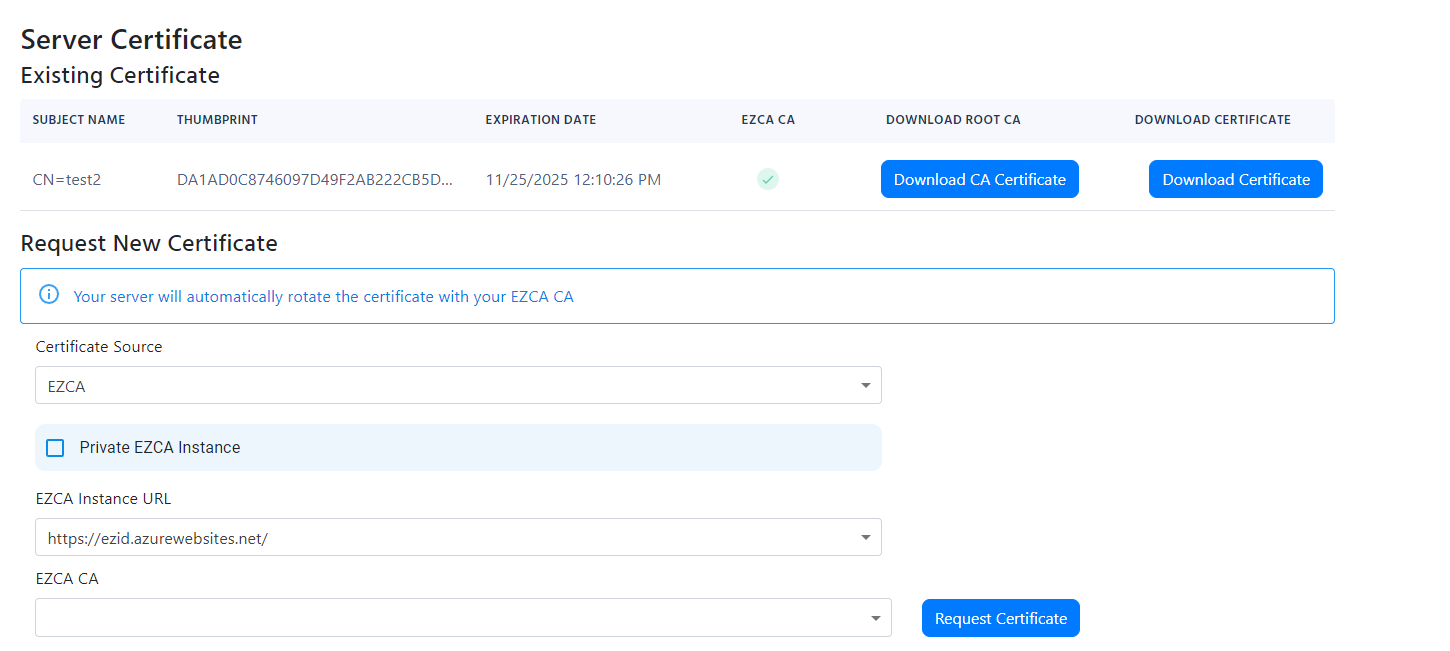
Add Server Certificate to RADIUS Using EZCA
If you are already an EZCA customer, you can leverage your existing EZCA CA to issue a RADIUS server certificate.
- From the ‘Certificate Source’ dropdown, select EZCA.
- If you are using an EZCA private instance, select the Private Instance checkbox and enter your EZCA Issuance URL.
- From the ‘EZCA CA’ dropdown with the certificates authorities you have in your EZCA instance, select the CA you want to use.
- Click Request Certificate to create a new RADIUS server certificate. EZRADIUS will automatically create the certificate for you. You do not need to specify an existing certificate or create a CSR. The certificate will be automatically renewed before it expires.
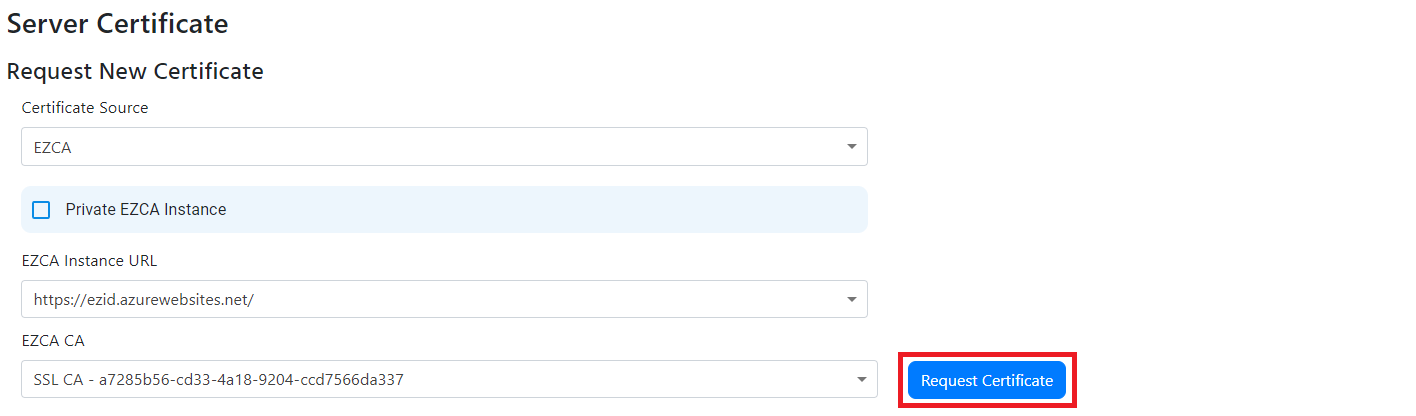
- You should now see the certificate in the list of certificates:
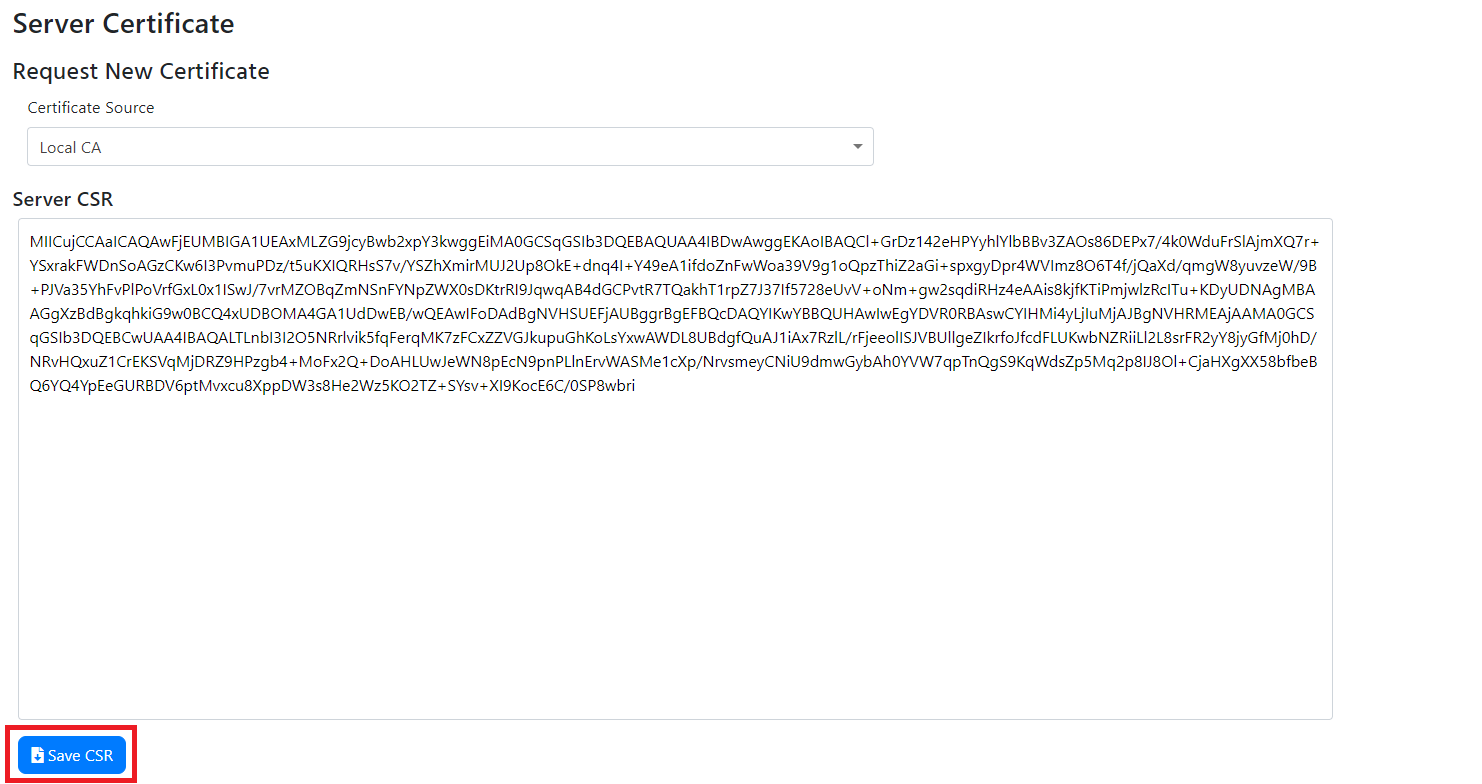
Add Server Certificate to RADIUS Using 3rd Party CA
If you are using a 3rd party CA, you can generate a CSR in EZRADIUS, submit it to your CA, and then upload the signed certificate back to EZRADIUS.
- From the ‘Certificate Source’ dropdown, select Local CA.
- Click the Create CSR button.
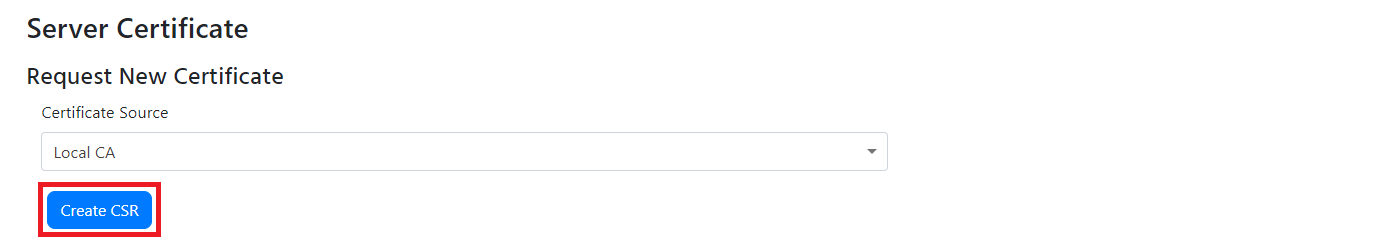
- Download the CSR by clicking the Save CSR button.
- Submit the CSR to your CA and download the certificate.
- Also download the certificate of your root CA.
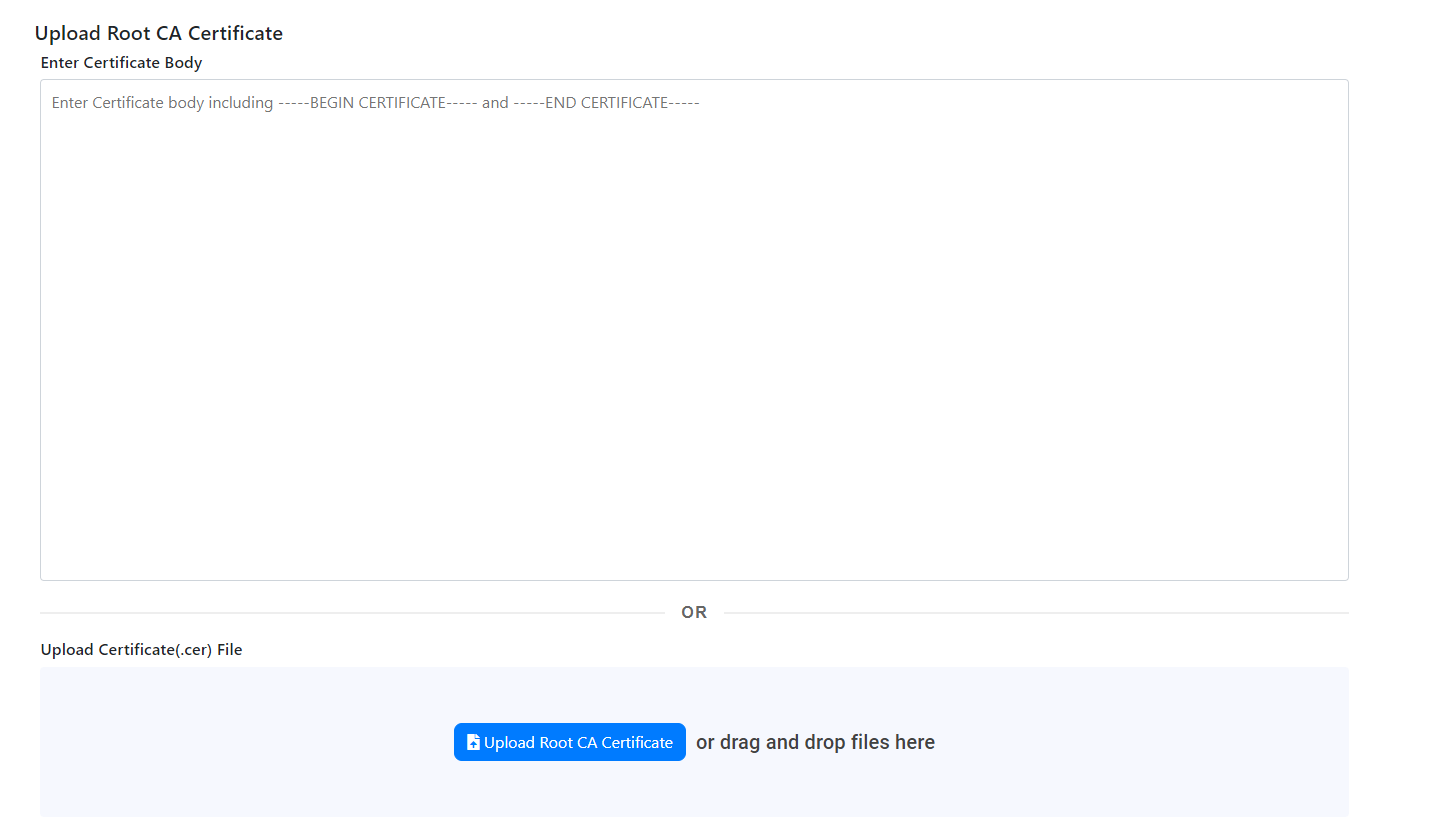
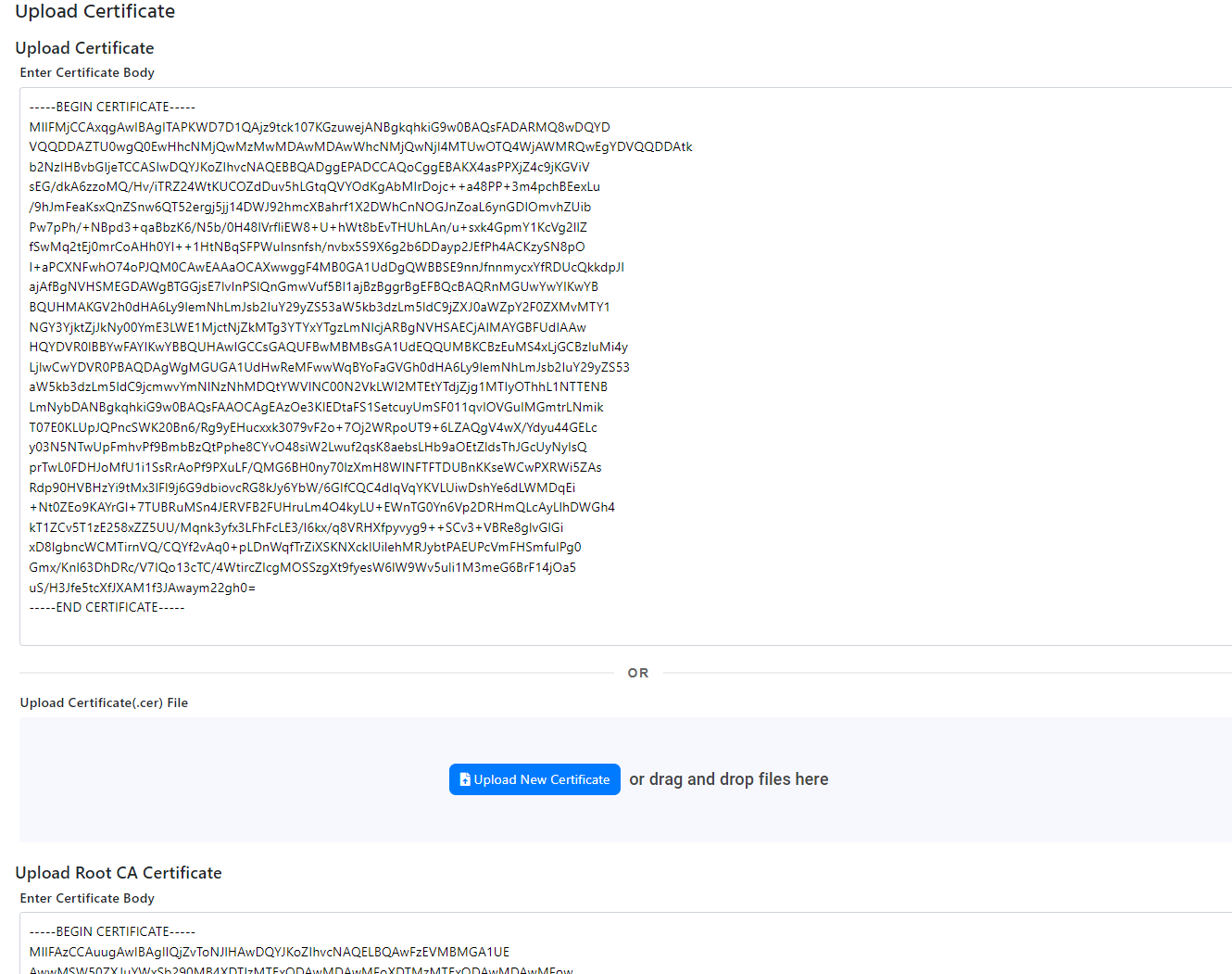
- Once you have the certificate, scroll down and either copy and paste the certificate PEM content or click on Upload Certificate and select the certificate in PEM format.
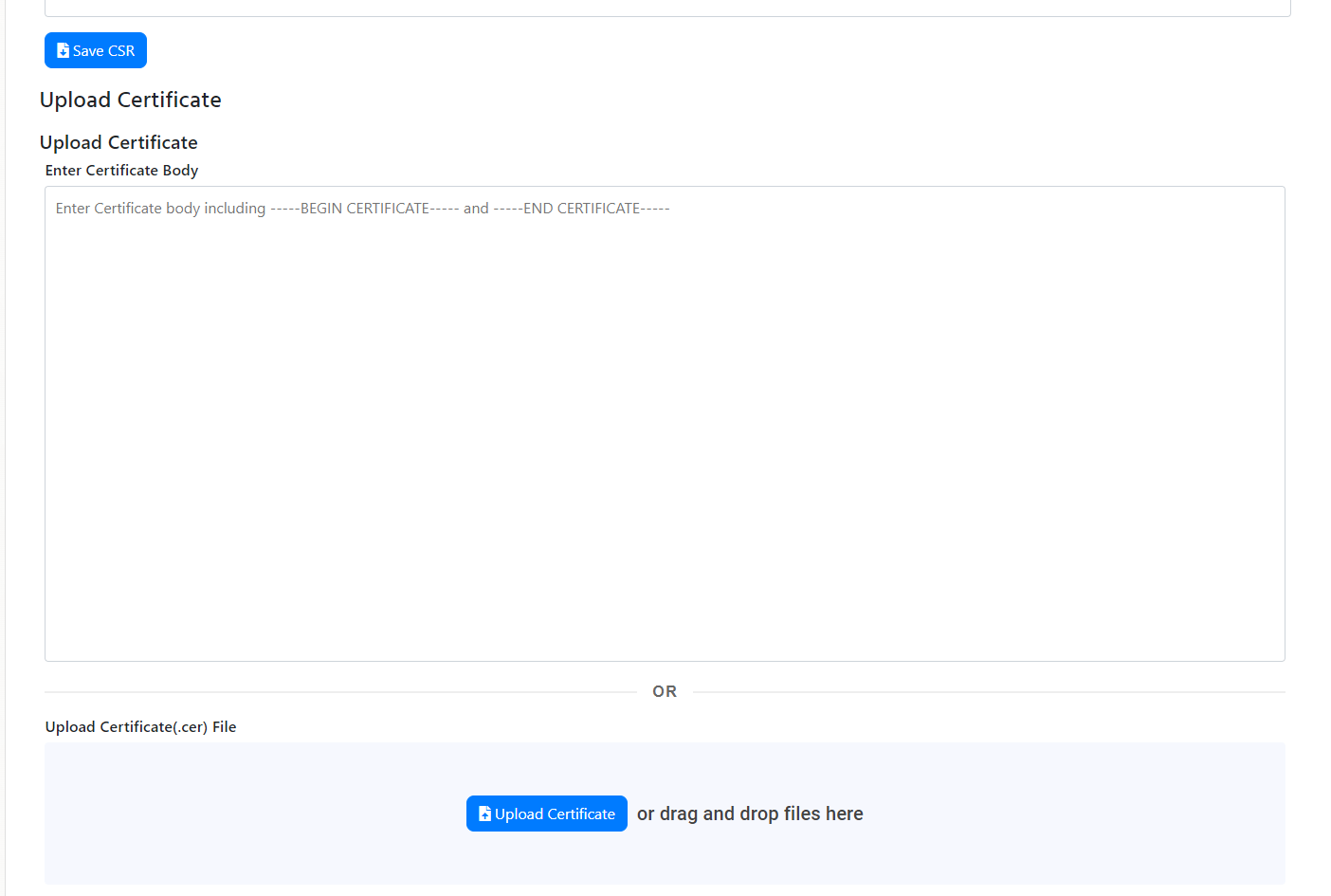
- After you upload your certificate, you must upload the certificate of the Root CA that signed the certificate. Scroll down and either copy and paste the certificate PEM content or click on Upload Root CA Certificate and select the certificate in PEM format.
- You will now have both the RADIUS server certificate and the Root CA certificate listed under your certificates.
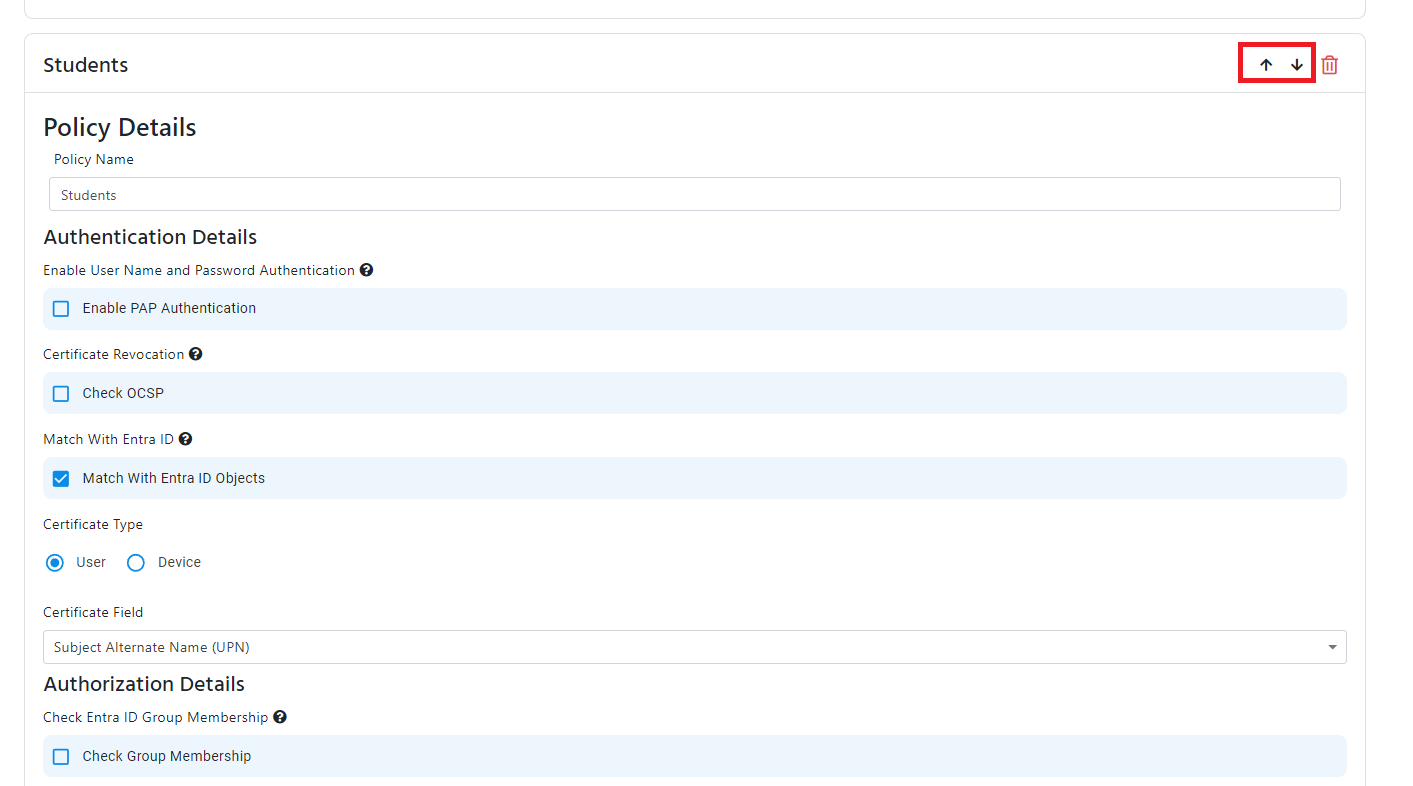
Step 5: Add Certificate Access Policy to RADIUS Network Policy
Now that you have configured Classic RADIUS and/or RadSec, setup your CAs, and added the server certificate, you can add your access policies. Access policies define the conditions under which a user or device can connect to your network. Each policy can have multiple access policies and they are evaluated in the order they are sorted.
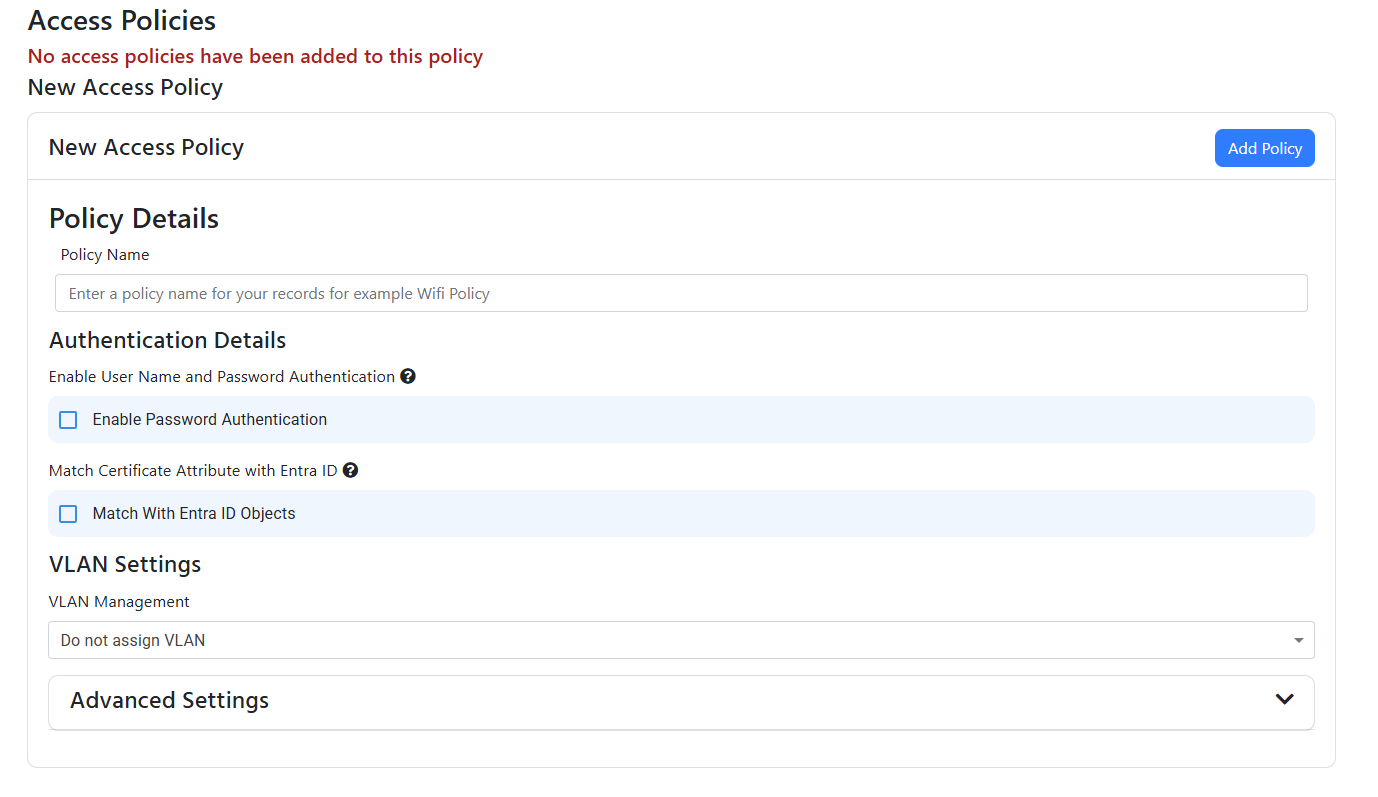
- Begin in the Access Policies section of the RADIUS network policy. By default, there will be no access policies listed.
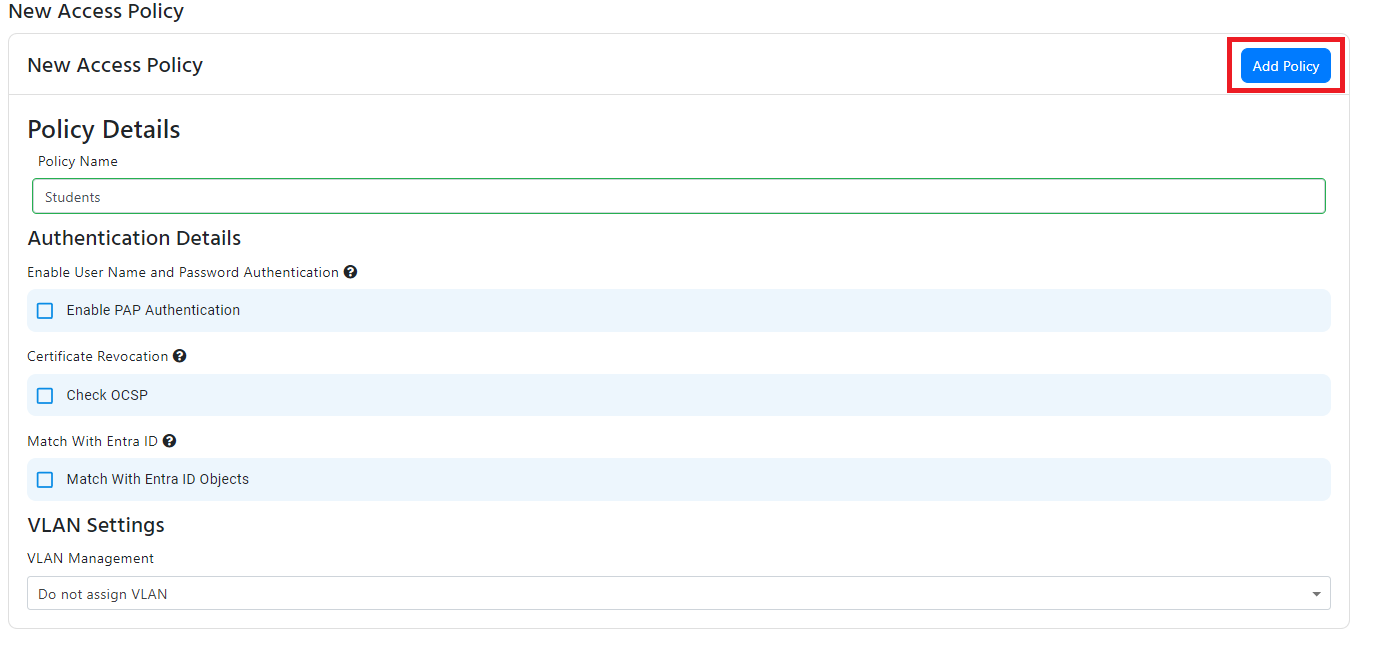
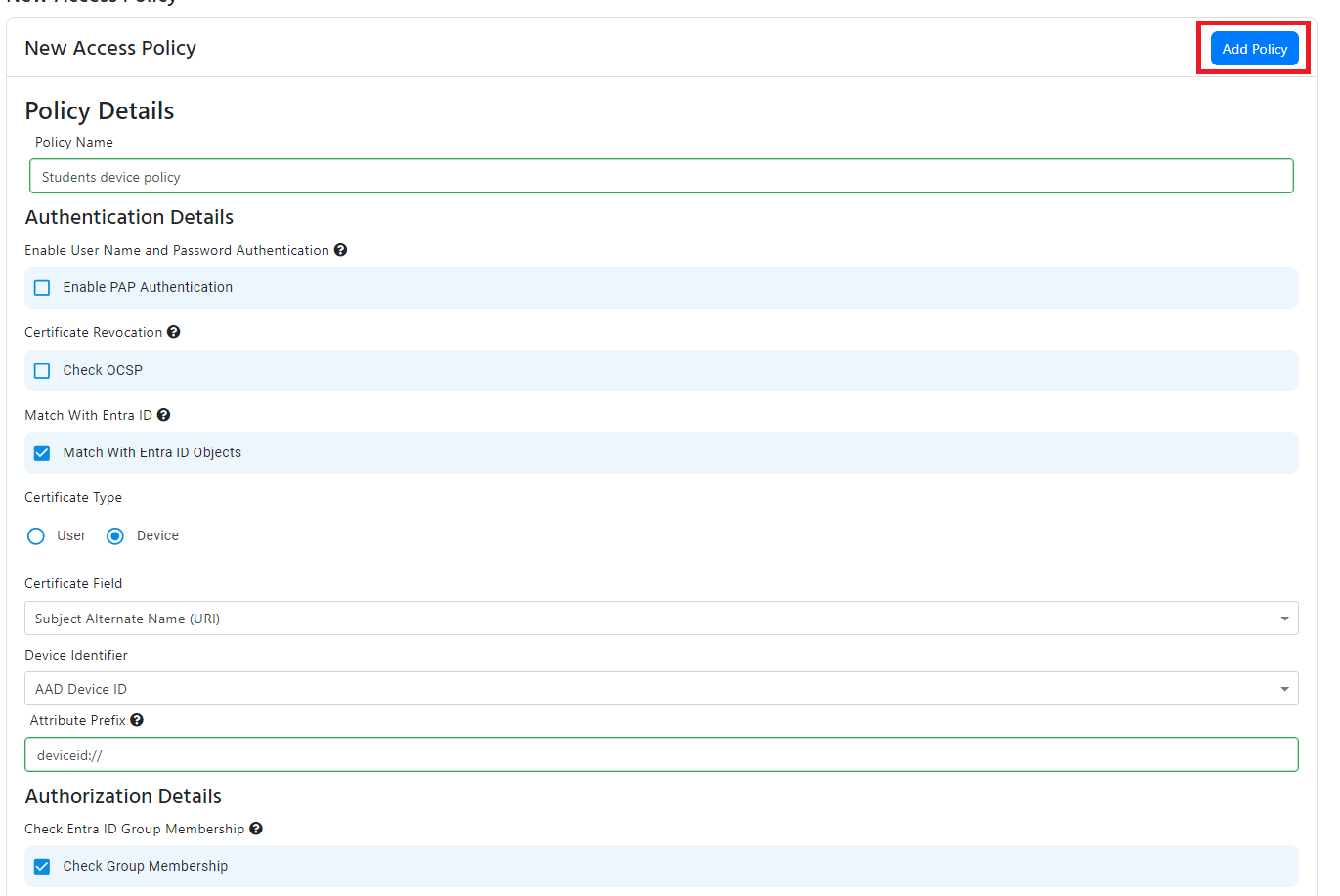
- Enter the friendly name of the access policy which is used for your records to easily identify the policy. In this example we’ll configure the RADIUS server as if it was for a school, so we will name the access policy “Students”. Replace this with a name that makes sense for your use case.
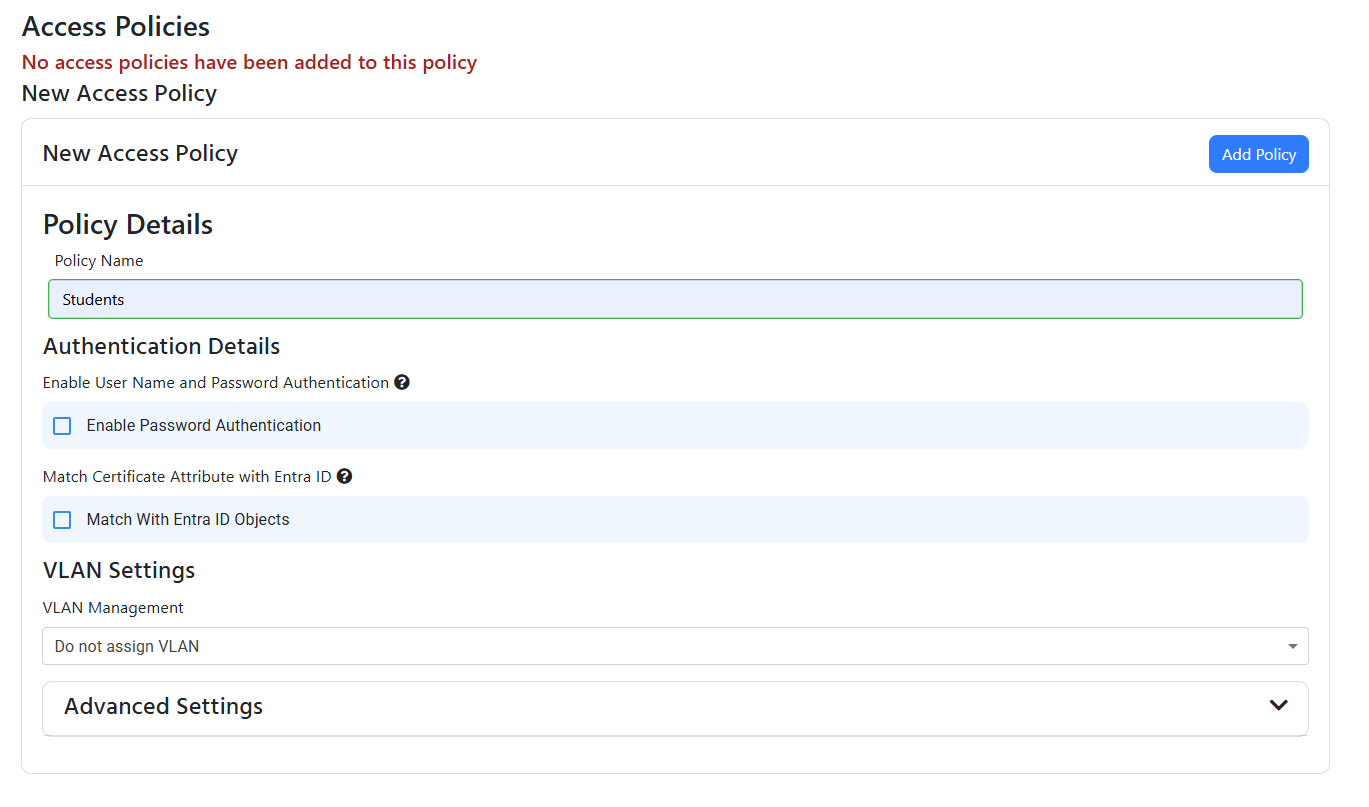
- For this policy we only want to enable EAP-TLS, so we will leave the Enable Password Authentication checkbox unchecked.
Configure Certificate Matching Options for Cloud RADIUS Policies
There are a few different ways you can match the certificate presented by the user or device to the access policy. In this guide we will focus on the four most common methods:
- CA Matching: If you only issue certificates for students from these CAs, then you can leave everything unchecked. and just assign the VLAN if required.
- Entra ID User Matching: EZRADIUS can extract the user UPN or user ID from a field of the certificate and validate with Entra ID that the user exists and even assign VLAN based on the groups the user is a member of.
- Entra ID Device Matching: EZRADIUS can extract the Entra ID device ID from a field of the certificate and validate with Entra ID that the device exists and even assign VLAN based on the groups the device is a member of.
- Intune Device Matching: EZRADIUS can extract the Intune device ID from a field of the certificate and validate with Intune that the device exists and is compliant with your Intune policies.
CA Matching for Cloud RADIUS
- If you want to only use CA matching and allow any certificate from the CAs you have added to the policy, you can leave the “Match With Entra ID Objects” checkbox unchecked.
- If you want to assign a VLAN to this policy, jump to the VLAN assignment section of this document. Otherwise, click “Add Policy” to add the policy to the list of access policies.
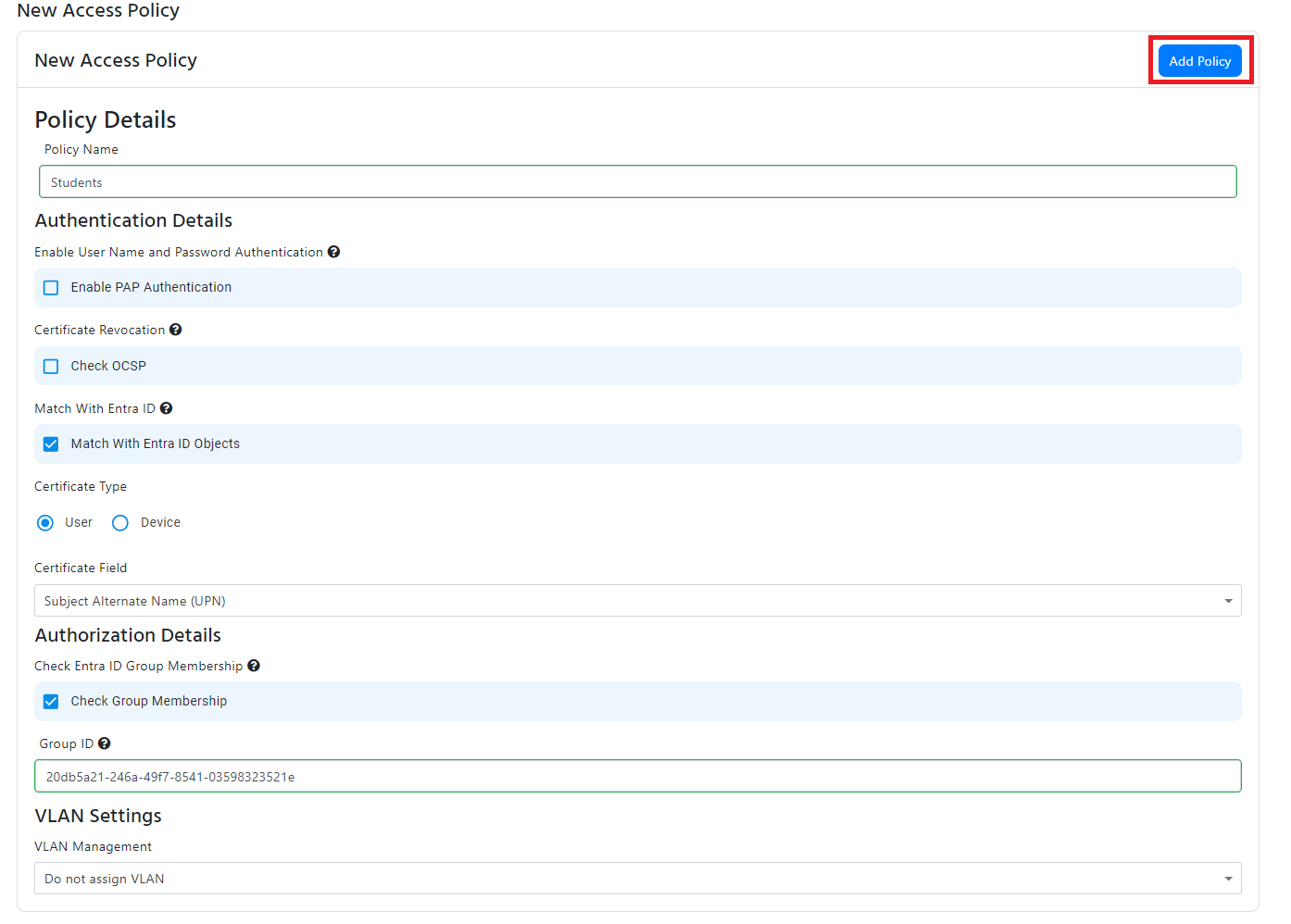
Entra ID User Matching for Cloud RADIUS
- If you want to match the user UPN or user ID from the certificate with an Entra ID user, check the Match With Entra ID Objects checkbox.
- Select User from the in the Certificate Type radio buttons.
- Select the field in the certificate that contains the user: usually UPN or user ID.
- By default, EZRADIUS will check that the user exists in Entra ID. If you want to also check if the user is a member of a group, check the Check Group Membership checkbox and enter the group name.
- If you want to assign a VLAN to this policy, jump to the VLAN assignment section of this document. Otherwise, click Add Policy to add the policy to the list of access policies.
Entra ID Device Matching for Cloud Radius
- If you want to match the device ID from the certificate with an Entra ID device, check the Match With Entra ID Objects checkbox.
- Select Device from the in the “Certificate Type” radio buttons.
- Select AAD Device ID from the “Device Identifier” dropdown, depending on which ID you are using in your certificates.
- Under “Certificate Field”, specify the value in certificate that contains the device ID.
- If you are using a Subject Alternative Name, it will also give you de ability to remove the prefix from the Device ID. For example, if your certificate has a prefix of
deviceid://you can enterdeviceid://as the prefix and EZRADIUS will ignore it when validating your certificates. - By default, EZRADIUS will check that the device exists in Entra ID. If you want to also check if the device is a member of a group, check the Check Group Membership checkbox and enter the group name. Note that the device must be a direct member of the group in Entra ID, nested groups are not supported
- If you want to assign a VLAN to this policy, jump to the VLAN assignment section of this document. Otherwise, click Add Policy to add the policy to the list of access policies.
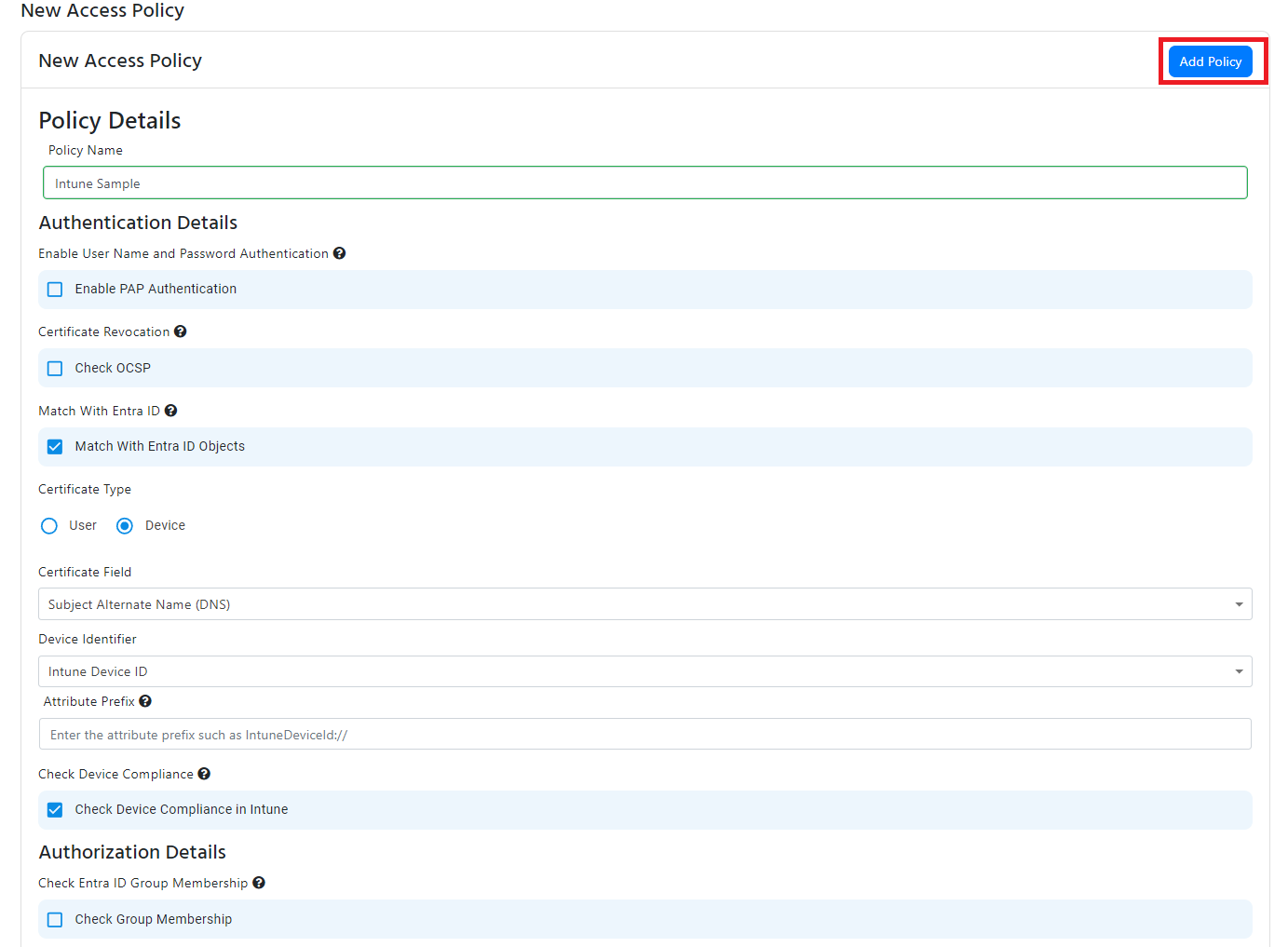
Intune Device Matching for Cloud RADIUS
- If you want to match the Intune device ID from the certificate with an Intune device, check the Match With Entra ID Objects checkbox.
- Select Device from the in the “Certificate Type” radio buttons.
- Select Intune Device ID from the in the “Device Identifier” dropdown.
- Under “Certificate Field”, specify the value in certificate that contains the Intune device ID.
- If you are using a Subject Alternative Name, it will also give you de ability to remove the prefix from the Device ID. For example, if your certificate has a prefix of
IntuneDeviceId://you can enterIntuneDeviceId://as the prefix and EZRADIUS will ignore it when validating your certificates. - By default, EZRADIUS will check that the device exists in Intune. If you want to also check if the device is compliant with your Intune policies, check the Check Device Compliance in Intune checkbox.
- If you also want to check if the device is a member of a group, check the Check Group Membership checkbox and enter the group name. Note that the device must be a member of the group in Intune, nested groups are not supported
- If you want to assign a VLAN to this policy, jump to the VLAN assignment section of this document. Otherwise, click Add Policy to add the policy to the list of access policies.
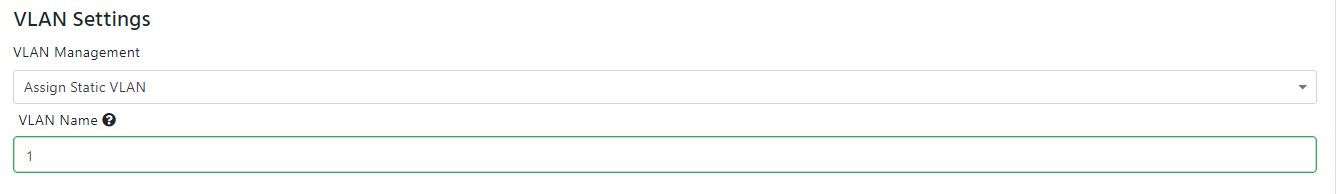
VLAN Assignment for Cloud RADIUS
By default, a VLAN is not set. If you want to assign a VLAN based on the access policy, you can do so in two ways:
-
Static VLAN Assignment: If you want to assign a static VLAN to the policy, you can select “Assign Static VLAN” from the drop down and you can enter the VLAN ID in the VLAN Name field.
-
Dynamic VLAN Assignment Based on Certificate Value: If you want to assign a VLAN based on a value in the certificate, you can do so by selecting the “Assign Dynamic VLAN (From Certificate Value)” from the VLAN management dropdown selecting the field in the certificate that contains the VLAN ID. Same as with the device ID, if you are using a Subject Alternative Name, it will also give you the ability to remove the prefix from the VLAN ID. For example if your certificate has
vlan://you can entervlan://as the prefix and EZRADIUS knows to ignore that when assigning your VLANs.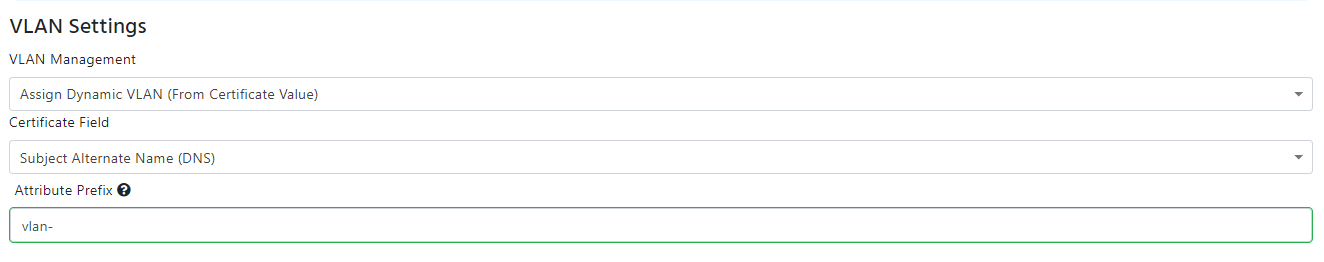
-
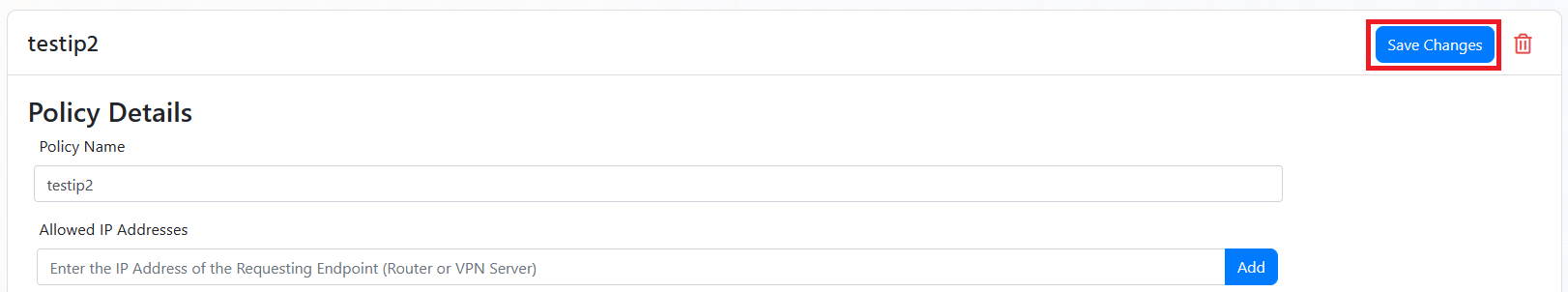
Once you have added the access policies and the VLAN assignment, scroll up to the top and click “Save Changes” to save the policy.
Make Sure to Save Your ChangesAfter adding the access policy, make sure to click Save Changes at the top right of the RADIUS network policy to save your changes. If you navigate away from the page without saving, your changes will be lost.
Done!
You have successfully created a Cloud RADIUS network policy that uses Entra ID Passwords for authentication. Make sure to test the configuration with a device to ensure everything is working as expected.
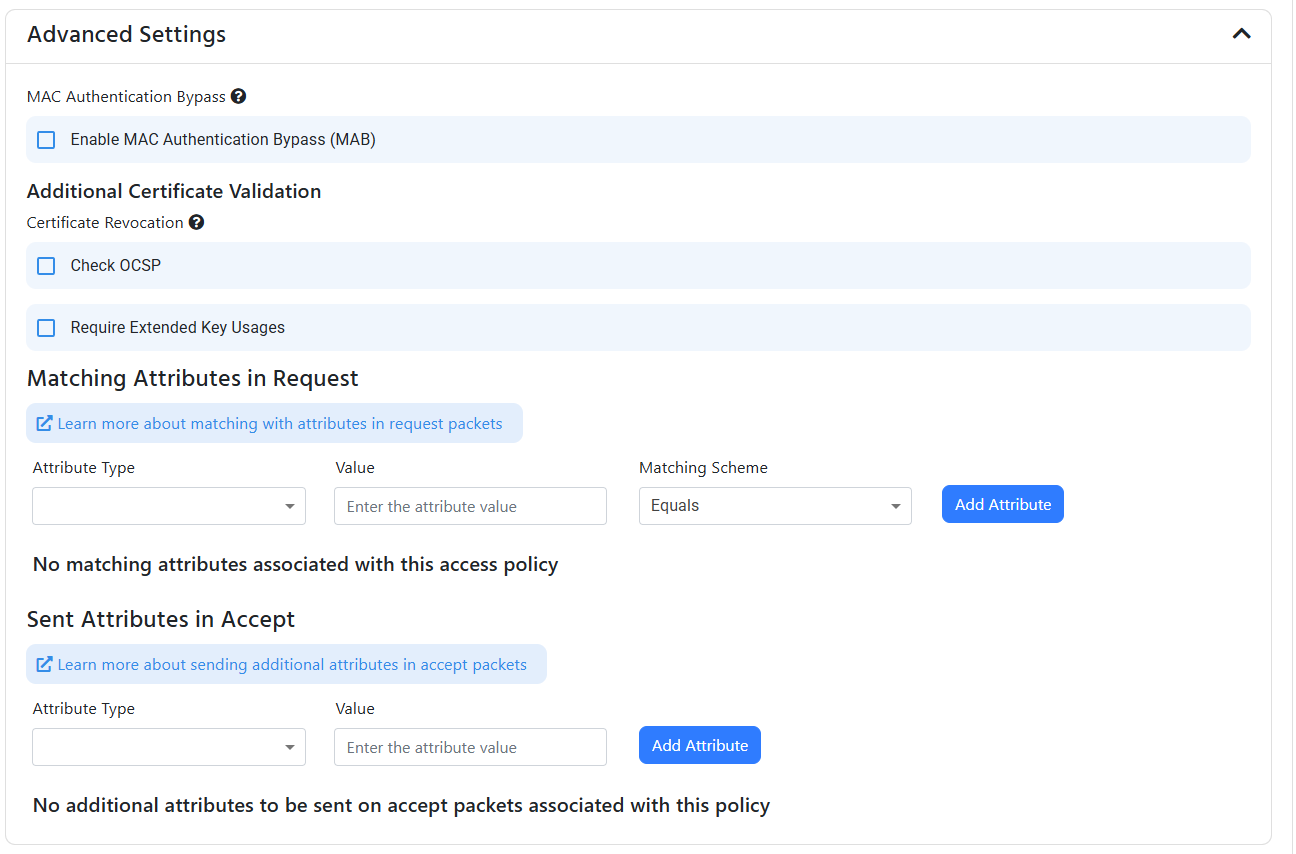
Advanced Settings
We try to keep the UI and policies as simple as possible but we understand that some of our customers have more advanced requirements, for this reason we have added some advanced settings that you can enable by expanding on the “Advanced Settings” tab.
- Enable MAC Authentication Bypass: If you want to enable MAC Authentication Bypass, you can check the “Enable MAC Authentication Bypass” checkbox, then you will have to whitelist the MAC addresses of the devices you want to allow to bypass the authentication.
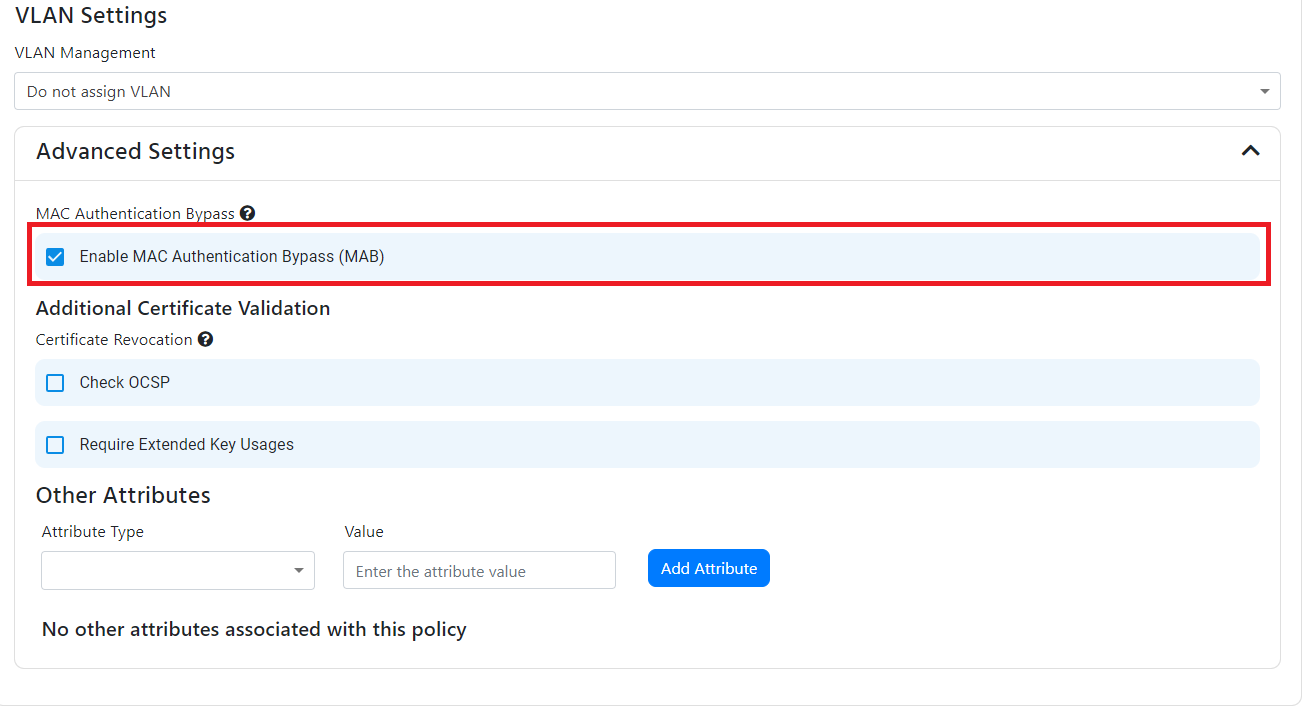
- Check OCSP: EZRADIUS check CRLs (Certificate Revocations Lists) by default, if in addition to CRLs you want to check OCSP, you can check the “Enable OCSP” checkbox. you can read more about the difference between CRL and OCSP here
- Require Extended Key Usage: If you want to require that the certificate has specific Extended Key Usages such as “Client Authentication”, you can check the “Require Extended Key Usage” checkbox.
- Matching Attributes in Request: If you want to match attributes in the request (for example, matching the SSID name sent as a calling station ID), you can add the attributes in the “Match Attributes in Request” and enter the value and the matching scheme (either contains or equals). Some common attributes to match are:
- Called-Station-ID: Usually set-up to contain the SSID of the network or the MAC address of a device when carrying out MAC-Authentication-Bypass
- NAS Identifier (NAS-ID): Usually set-up to contain the SSID of the network or the MAC address of a device when carrying out MAC-Authentication-Bypass
- Sent Attributes in Response: If you want to send attributes in the response (for example, sending the Filter-Id to the device), you can add the attributes in the “Sent Attributes in Response” and enter the value. Supported attributes are:
- Filter-Id: Can be used to assign a pre-defined access control list (ACL) to the user that successfully authenticates with the access policy
- Cisco-AVPair: Cisco-specific attribute
Priority Order of Access Policies
The access policies are checked in the order they are sorted, you can change the order of the access policies by clicking on the up and down arrows on the right side of the access policy.
- Once your policy is ready, click “Save Changes” at the top to save the policy changes.