How-To: Deploy Local RADIUS Proxy for Cloud RADIUS
What is the EZRADIUS Local RADIUS Proxy?
While EZRADIUS is designed with high-availability and geo-redundancy at its core, a fiber cut or internet outages may still disrupt your connection. When this happens, it’s vital that your devices and users are still able to connect to your networks and Wi-Fi.
The EZRADIUS Local Proxy is a free add-on to your cloud-based EZRADIUS service which can be hosted within your network and act as a proxy between your network and the EZRADIUS cloud servers. During normal operation, authentication results are cached on the local proxy and improve performance for subsequent connections during the cache period. During a service disruption or internet outage, users can continue to authenticate to your network until the connection back to the EZRADIUS cloud servers are restored.
🚀 Set Up a Local RADIUS ProxyAdvantages of Running Cloud RADIUS Proxy
- Reduced Latency: By handling authentication requests locally, you can reduce the latency associated with cloud communication, leading to faster authentication times.
- Increased Reliability: RADIUS was created using the UDP protocol, which might lose some packets when going through the internet. Using a local RADIUS proxy can help mitigate this issue by keeping that protocol local and sending the information to the cloud using a more traditional TCP connection. Additionally, in the event of a cloud outage or connectivity issue, a local RADIUS proxy can continue to authenticate users, ensuring uninterrupted access to critical services.
- Compliance: Some organizations may have compliance requirements that necessitate keeping authentication data on-premises. A local proxy can help meet these requirements while still leveraging cloud services.
- Security for Insecure Protocols: WWhile modern RADIUS authentication protocols are secure by default such as EAP-TLS (Certificate based authentication), or EAP-TTLS (Entra ID Password Authentication) some legacy protocols such as MAC Authentication Bypass are not secure to send unencrypted through the web (Radsec protects against this, but some networking gear does not support Radsec), our RADIUS proxy will do all the RADIUS authentication locally in your network and will securely connect to our RADIUS server using https with client certificate authentication.
Do I Need Local Proxy To Run EZRADIUS Cloud RADIUS?
No, the local proxy is an optional, free add-on. EZRADIUS cloud RADIUS can fully function without a local RADIUS proxy. In fact, most of our customers do not use one. However, we understand some organizations may require a local proxy for compliance, performance, or redundancy reasons for highly critical workloads that have to work even if the connection to the cloud is lost.
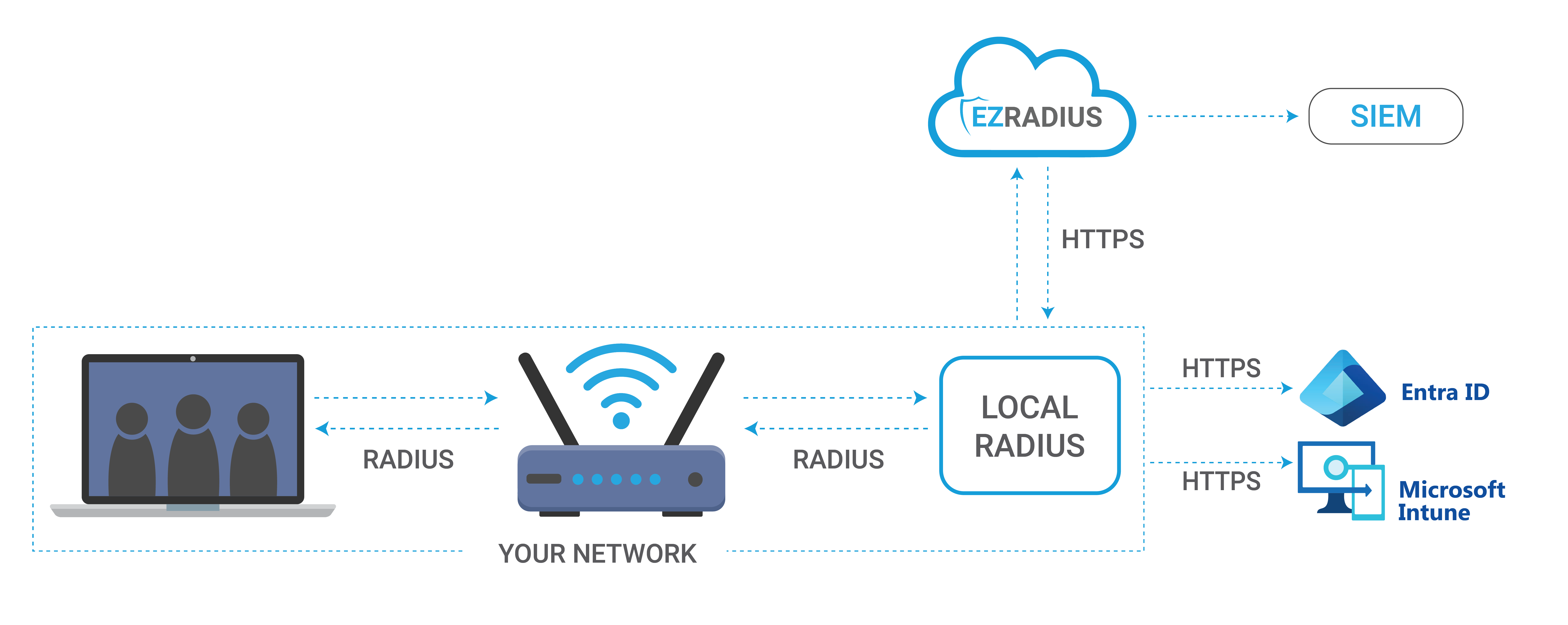
How EZRADIUS Local RADIUS Proxy Works
EZRADIUS Local RADIUS Proxy acts as an intermediary between your network devices (like VPNs, Wi-Fi access points, and firewalls) and the EZRADIUS Cloud RADIUS servers. You run it on-premises within your network, either on a dedicated machine, in a VM, or on an embedded device like a Raspberry Pi. Once it’s up and running, it receives authentication requests from your devices, processes them locally, and then forwards them to the cloud for validation. Since this setup has a configurable cache, it ensures that even if there are connectivity issues with the cloud, your local proxy can still handle authentication requests.
What Happens if Local RADIUS Proxy is Down?
One of the reasons people move to the cloud, is for the higher availability tools like EZRADIUS provide. This is why while Local RADIUS is beneficial, we recommend to not set it up as a single point of failure. If the local RADIUS proxy goes down, your networking gear should point to the EZRADIUS IP address directly to ensure continued authentication capabilities.
How Can I Setup Redundant Cloud RADIUS Proxies?
To set up redundant Cloud RADIUS proxies, you can deploy multiple instances of the EZRADIUS Local RADIUS Proxy in different locations within your network. These instances will be completely independent and since they are backed by the same cloud infrastructure, they can share the same authentication data. This ensures that if one instance goes down, the others can continue to handle authentication requests without interruption. Additionally, you can use load balancers (Note: make sure the load balancers are stick during the authentication to ensure that the backend server doesn’t change mid-authentication) to distribute authentication requests across the available proxy instances, further enhancing reliability and performance.