How-To: Export EZSSH Logs to CloudWatch
Prerequisites
How To Export Your EZSSH Audit Logs To CloudWatch
How To Enable Log Export in EZSSH Portal
-
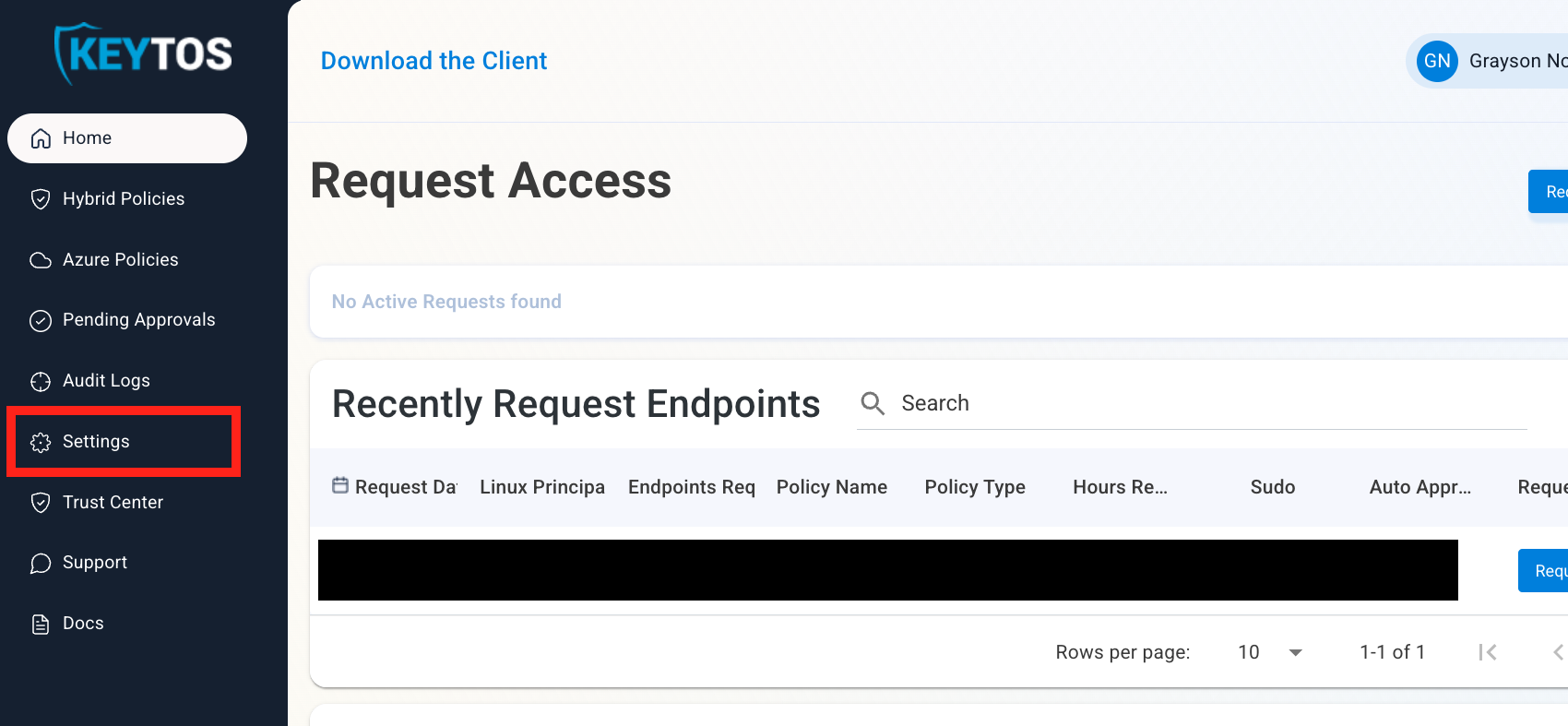
Go to the EZSSH Portal.
-
Click on Settings.
-
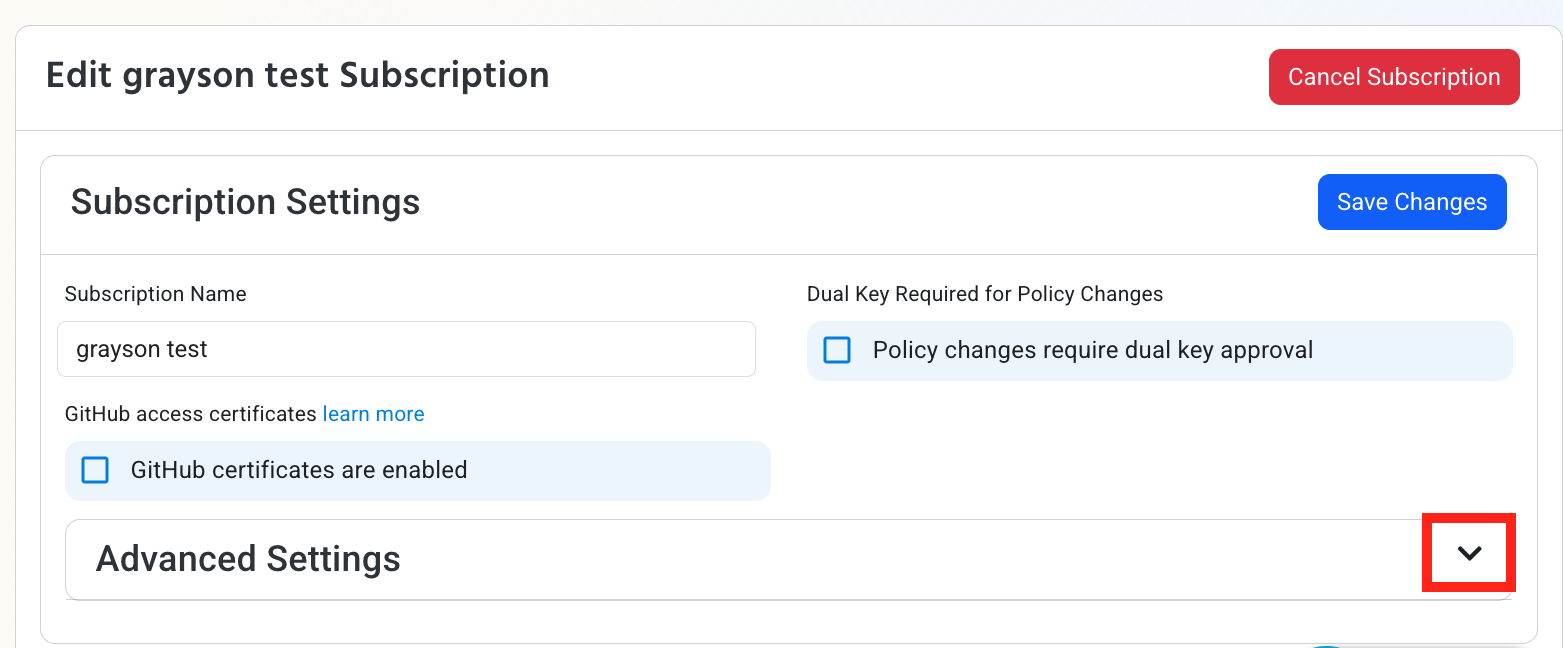
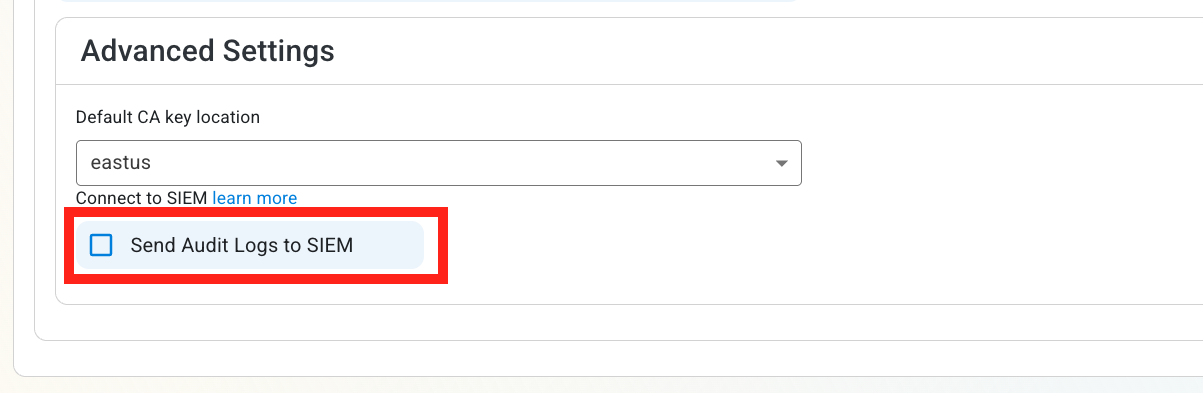
Expand your subscription’s Advanced Settings.
-
Enable the Send Audit Logs to SIEM option.
How To Configure the CloudWatch Exporter in the CloudWatch Portal
-
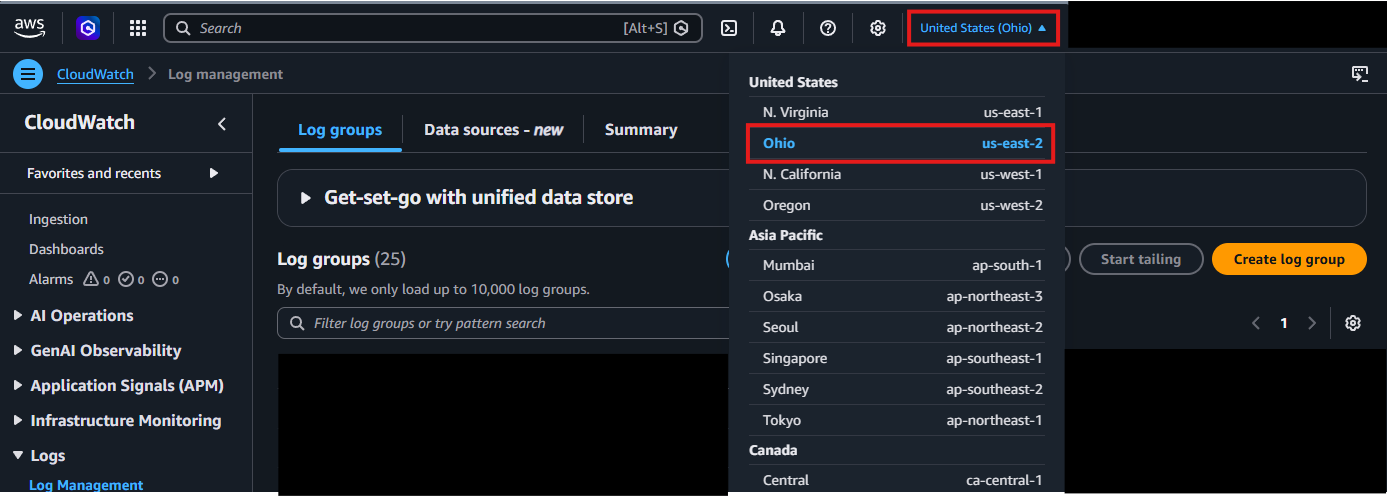
Open your CloudWatch Portal in a new browser tab.
-
In the top right corner, locate your AWS Region and make a note of it.
-
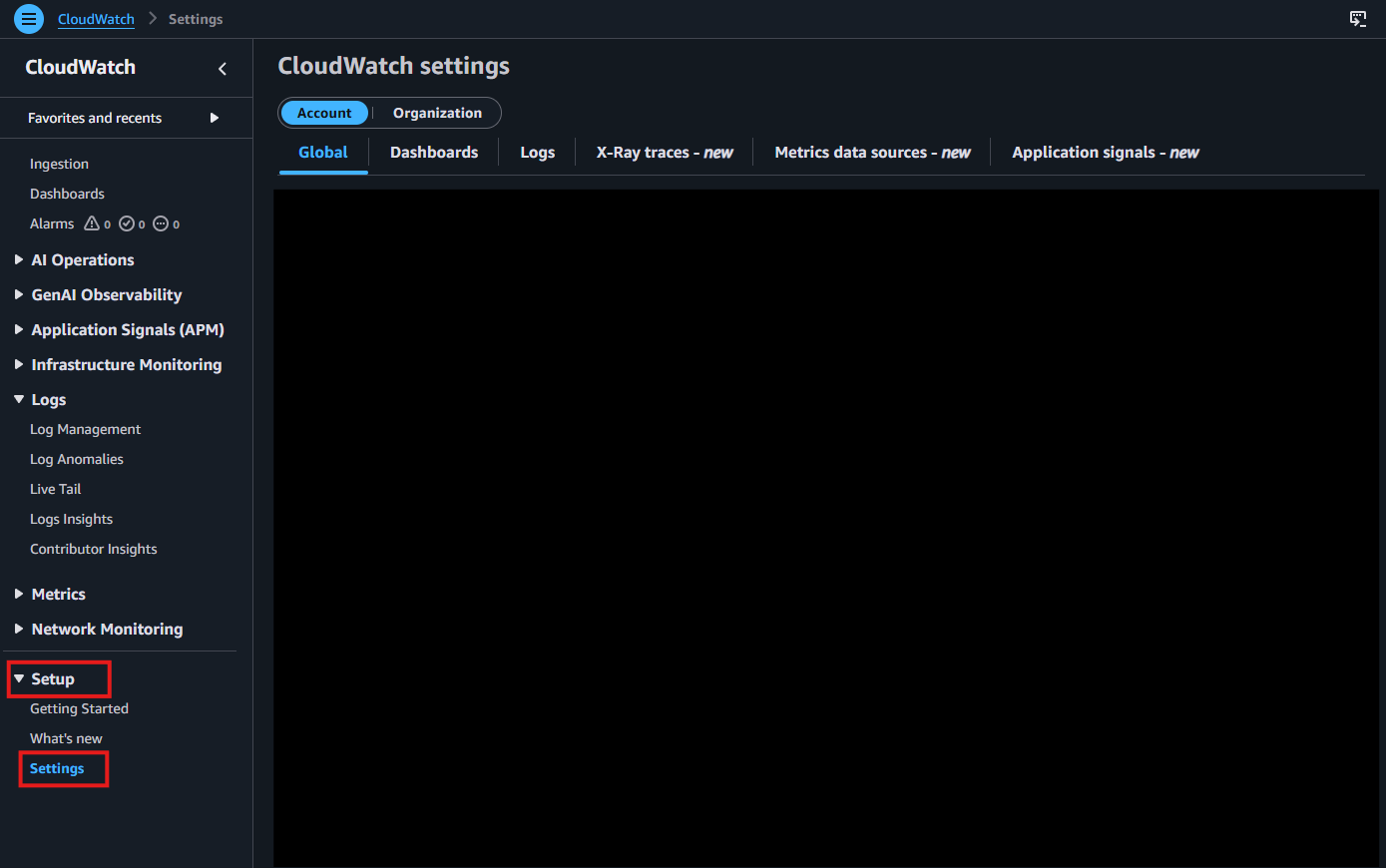
From the left-hand menu, under Setup, click on Settings.
-
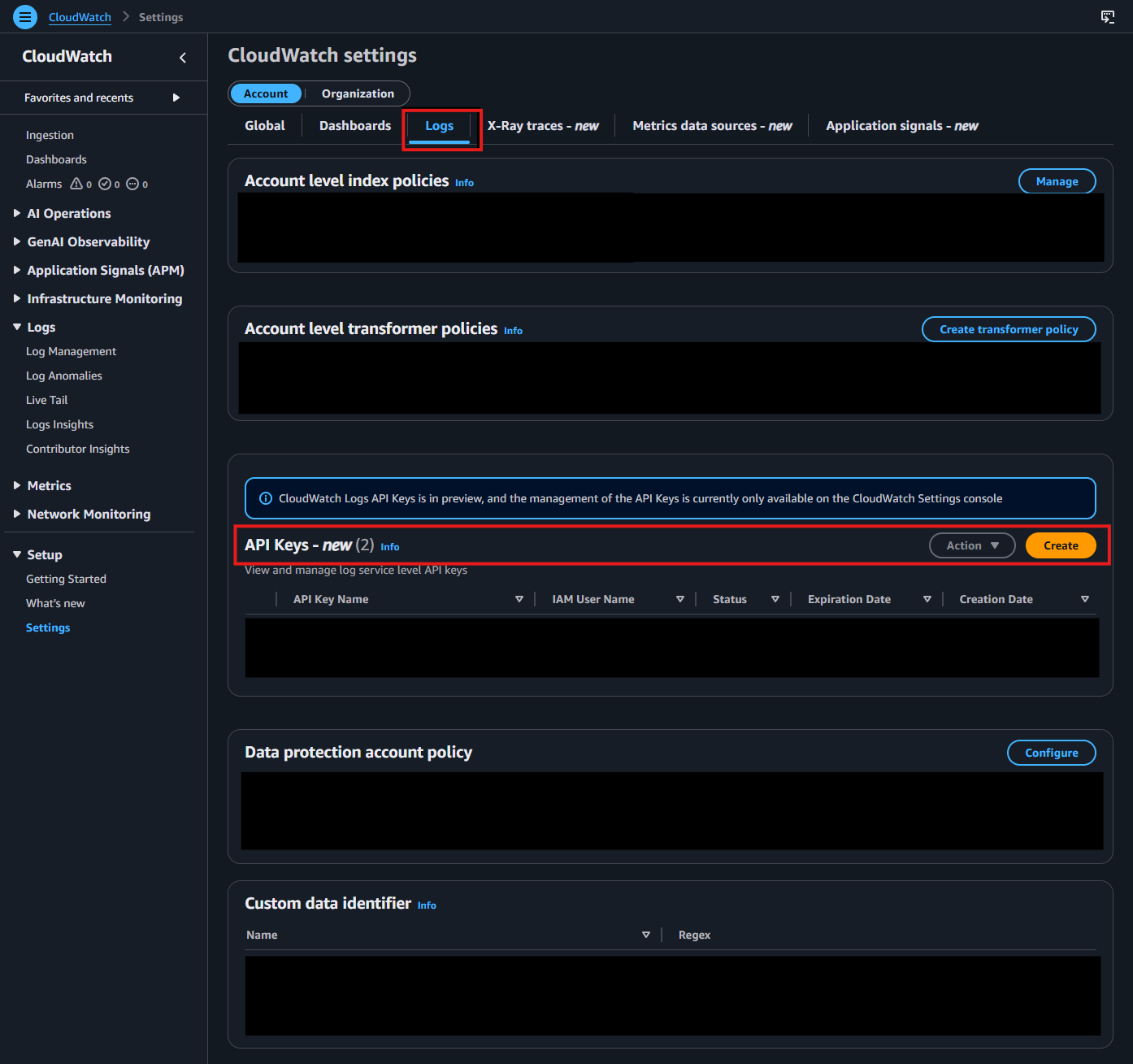
Go to the Logs tab. In the API Keys section, click Create.
-
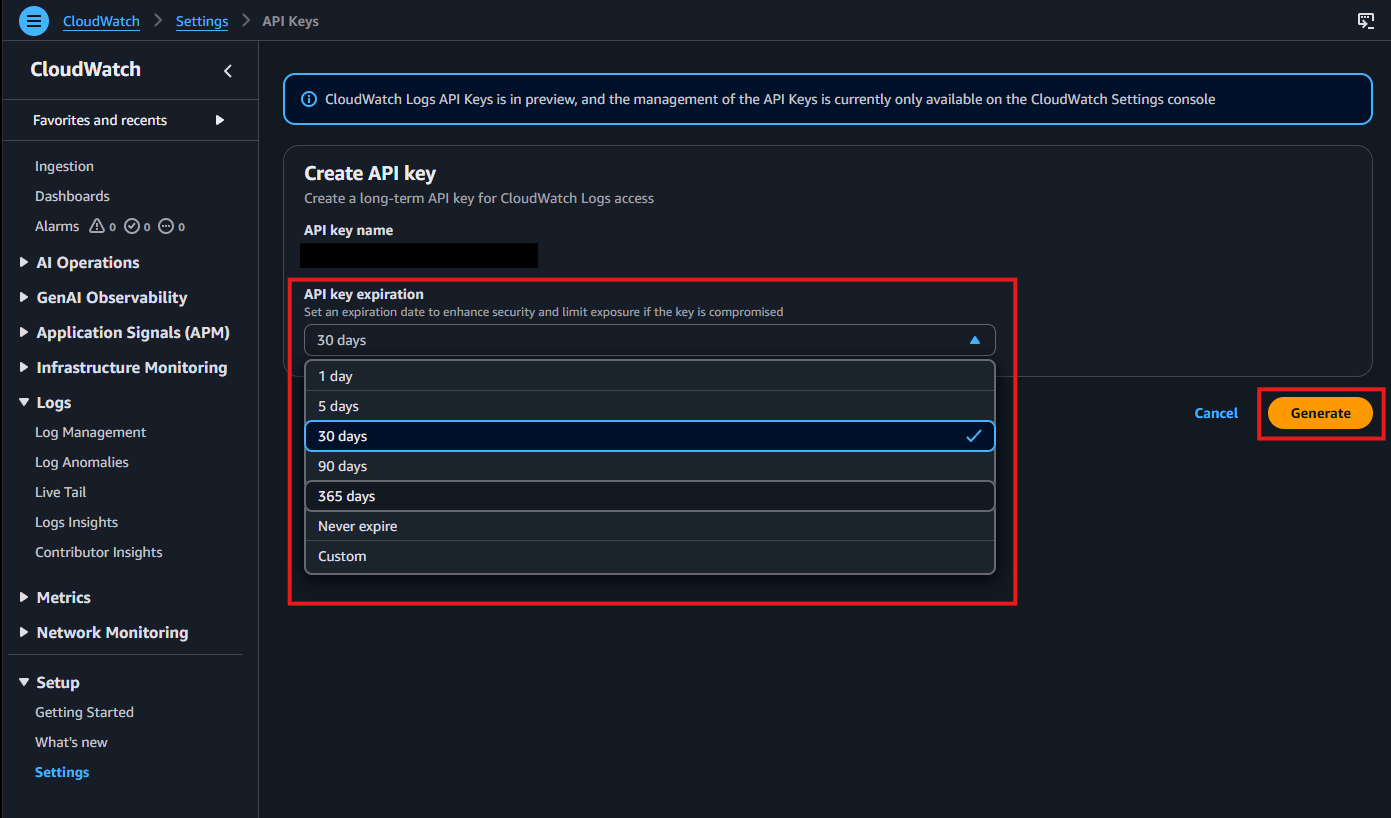
Choose your preferred API key expiration, then click Generate.
-
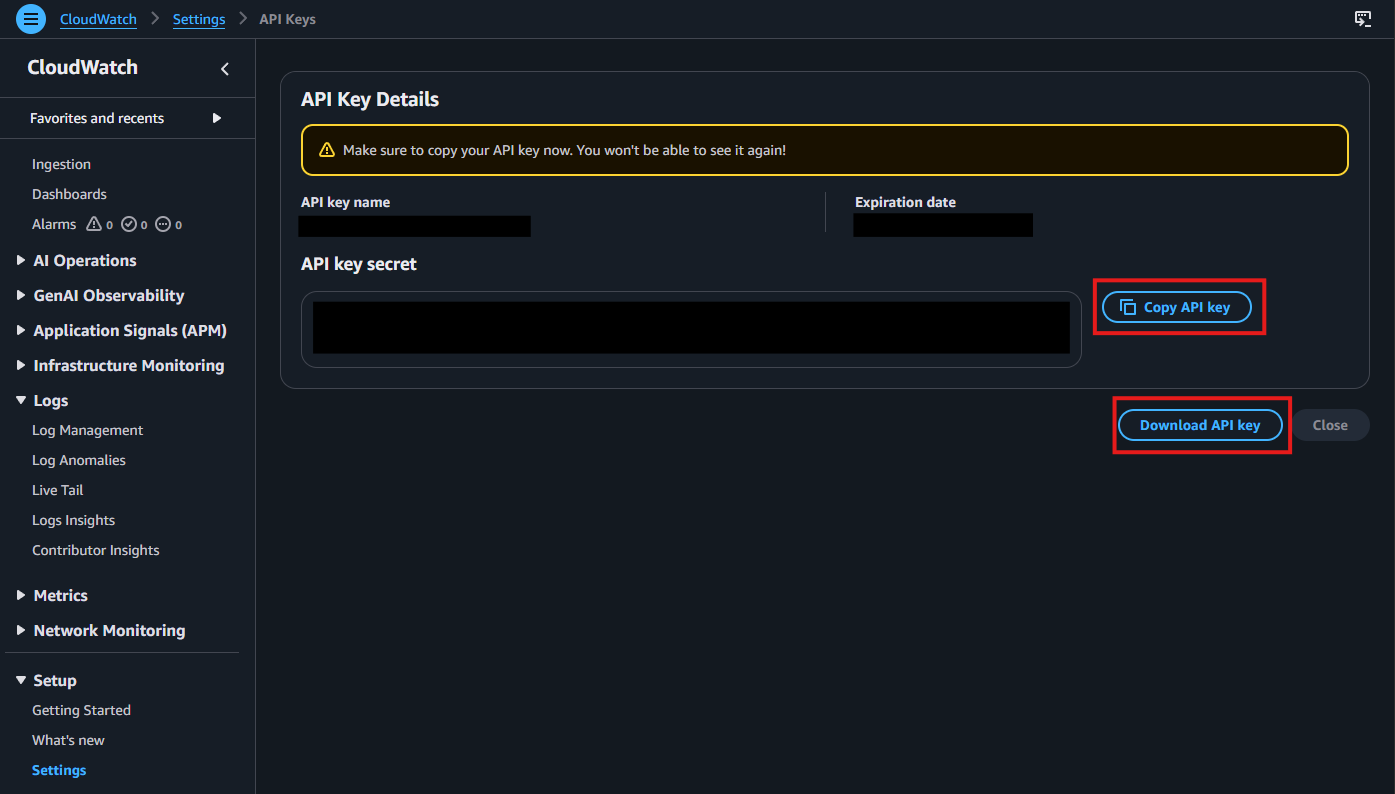
After the key is generated, copy and save it immediately. You will not be able to view it again after leaving this page.
-
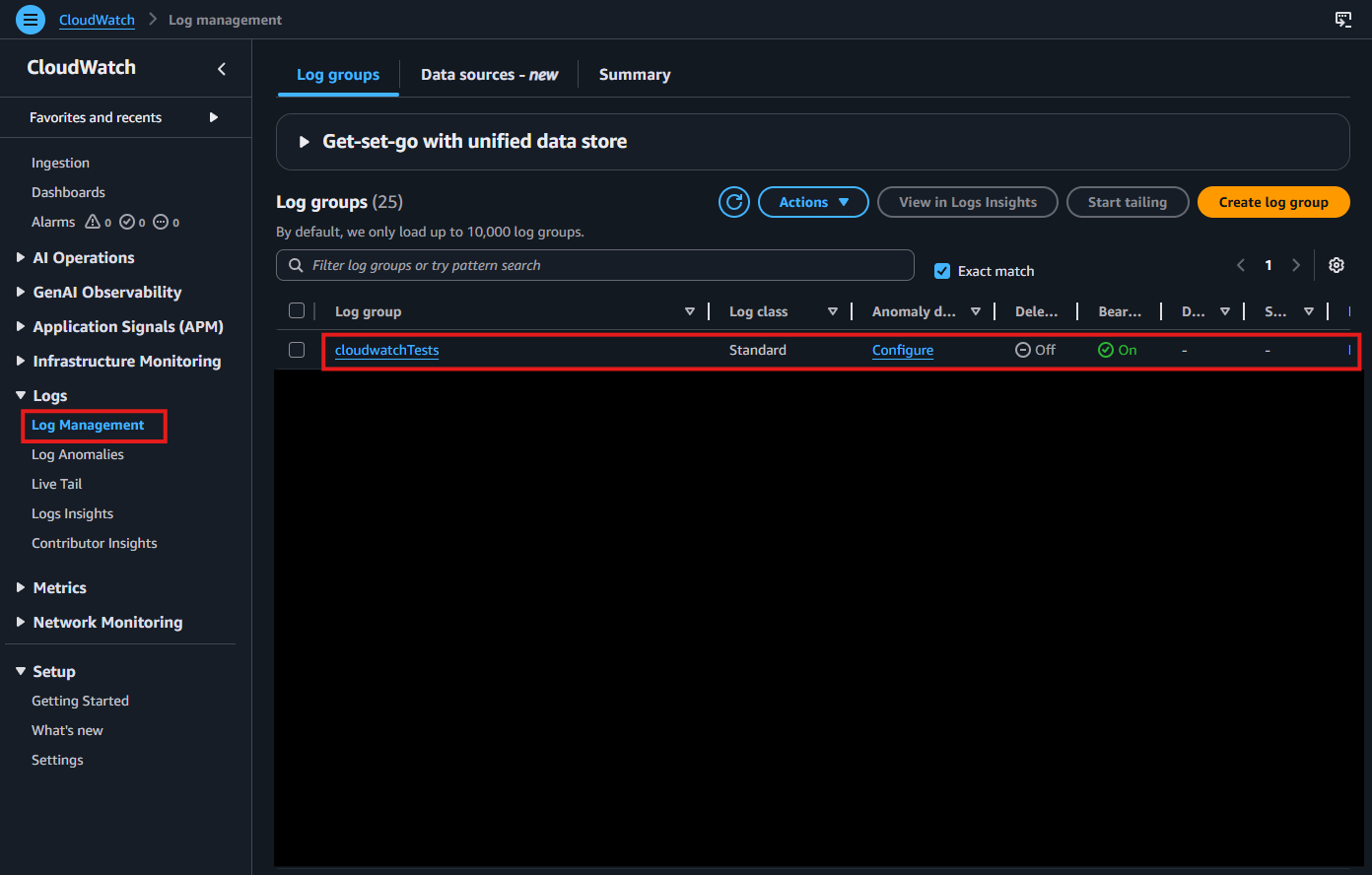
Navigate to Log Management under Logs in the left-hand menu. Select the Log Group where you want to deliver your logs.
-
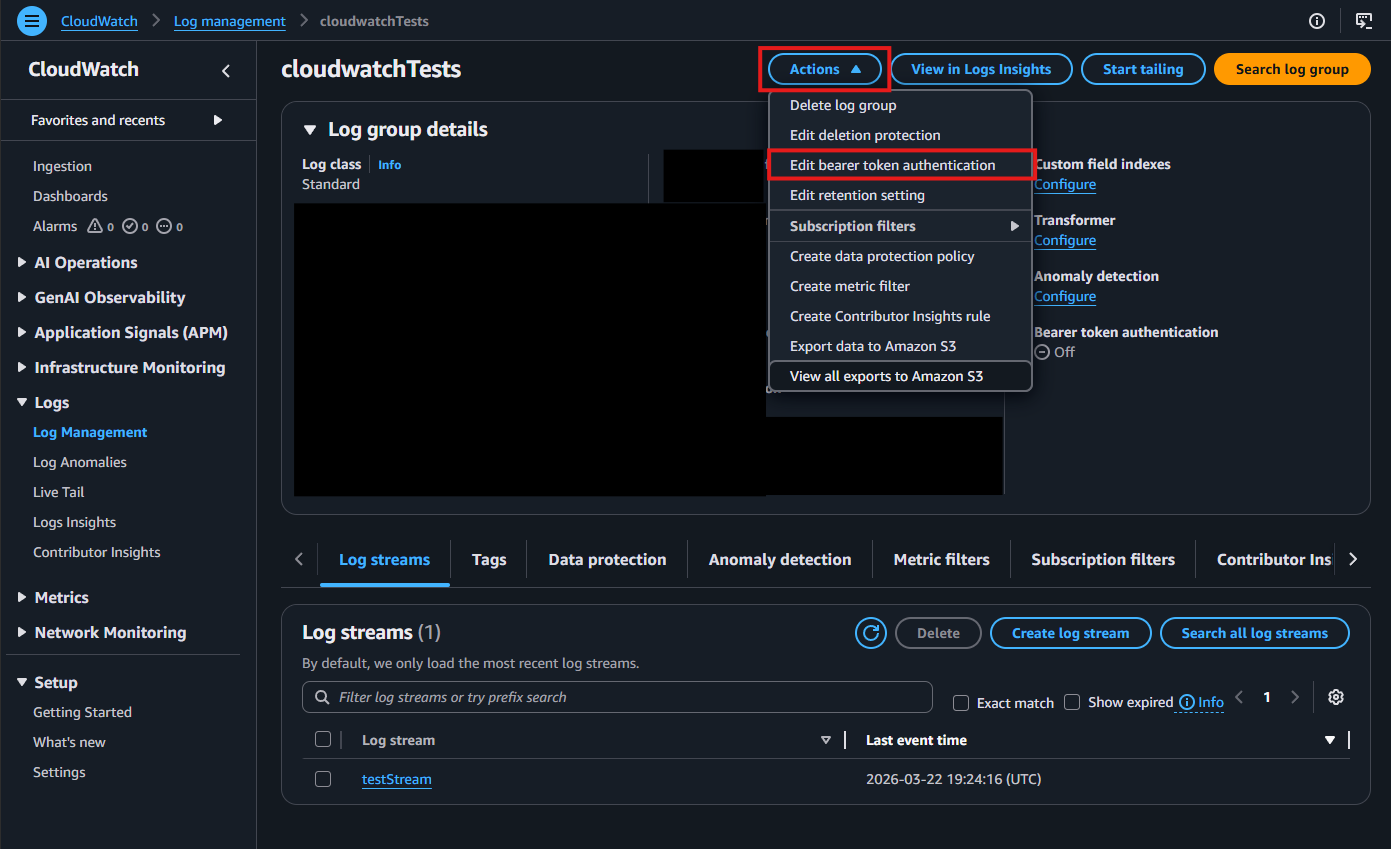
Click the Actions dropdown, then select Edit bearer token authentication.
-
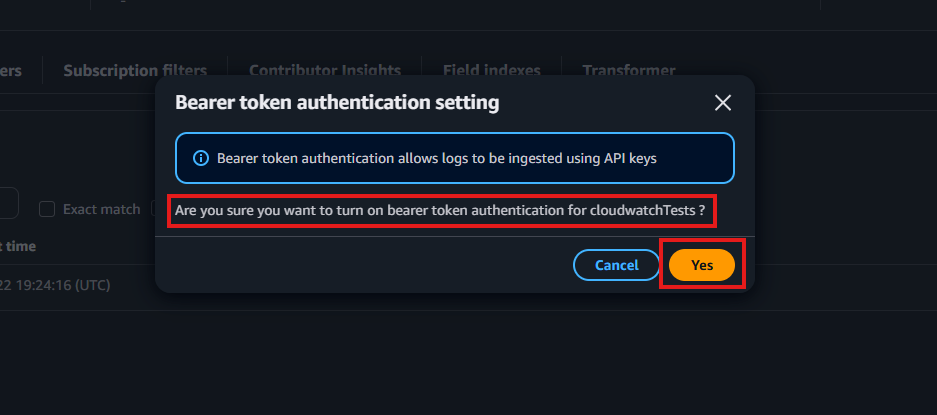
When prompted, enable bearer token authentication by selecting Yes.
-
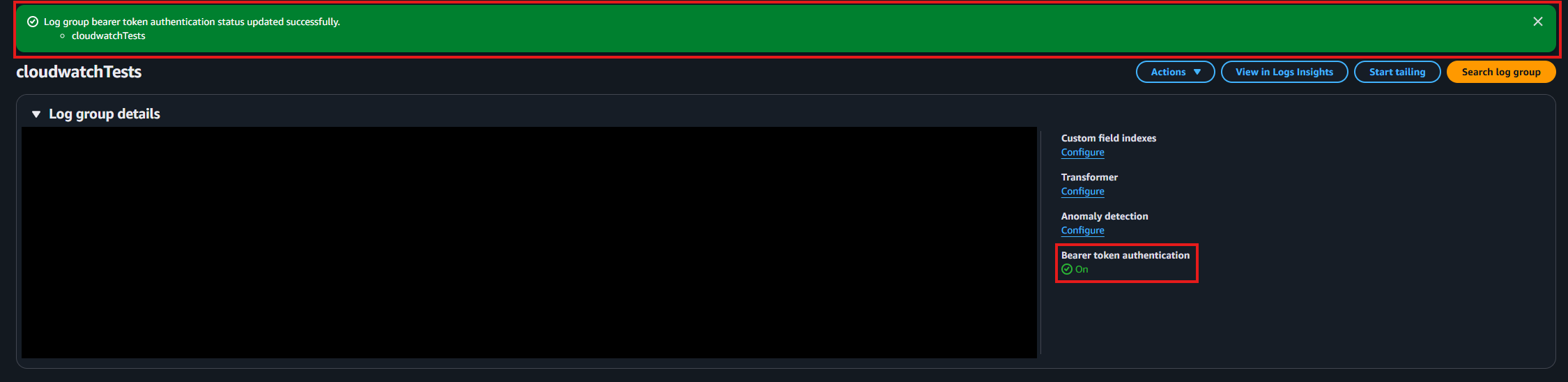
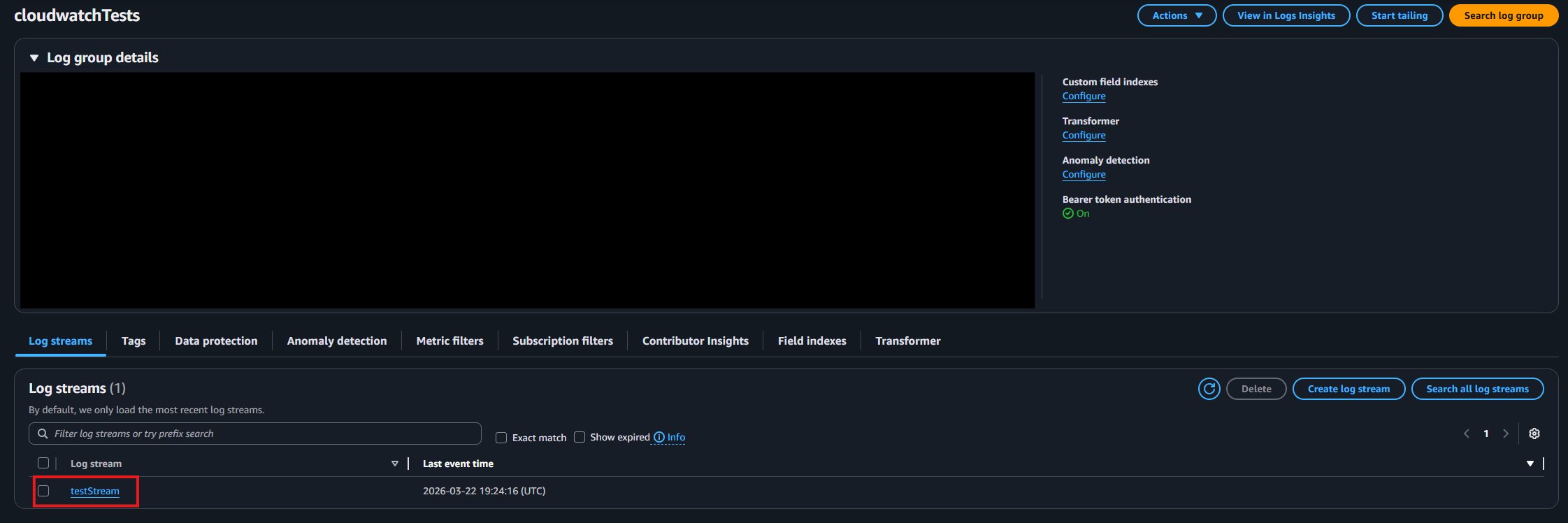
Confirm that bearer token authentication is enabled.
-
Identify and note the log stream where you want your logs delivered.
How To Configure the CloudWatch SIEM in EZSSH Portal
-
Now go back to the EZSSH Portal.
-
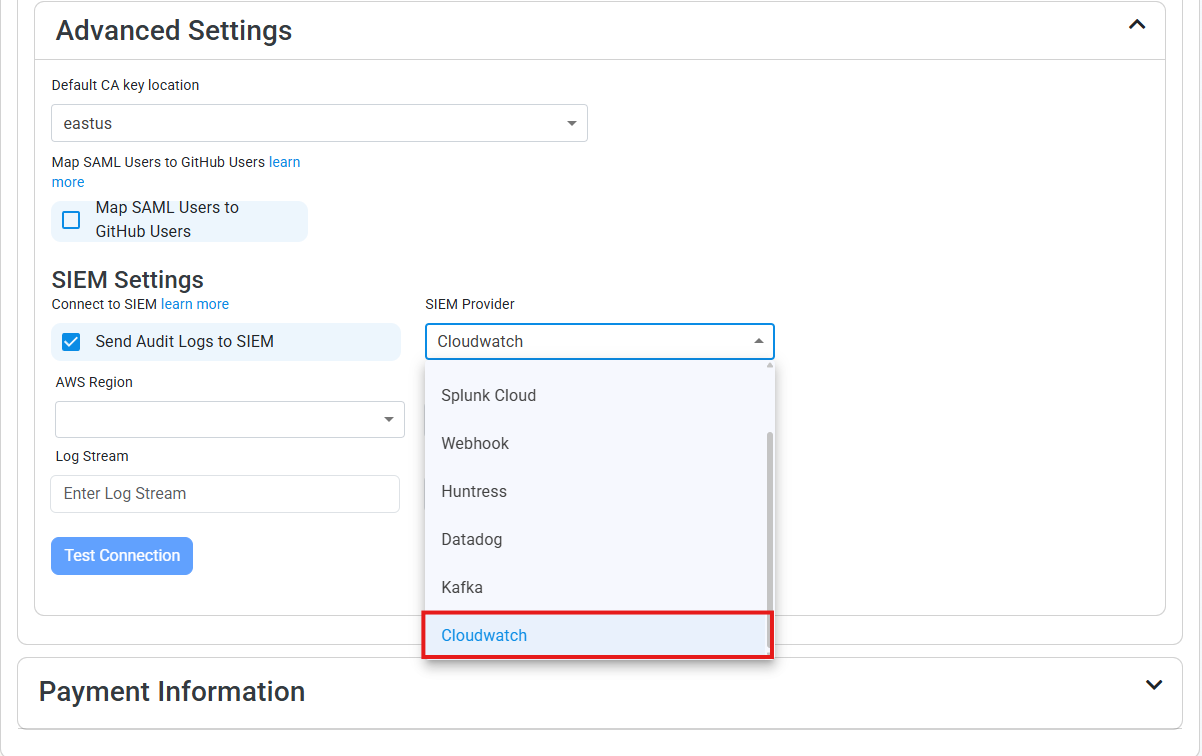
Select CloudWatch as the SIEM Provider.
-
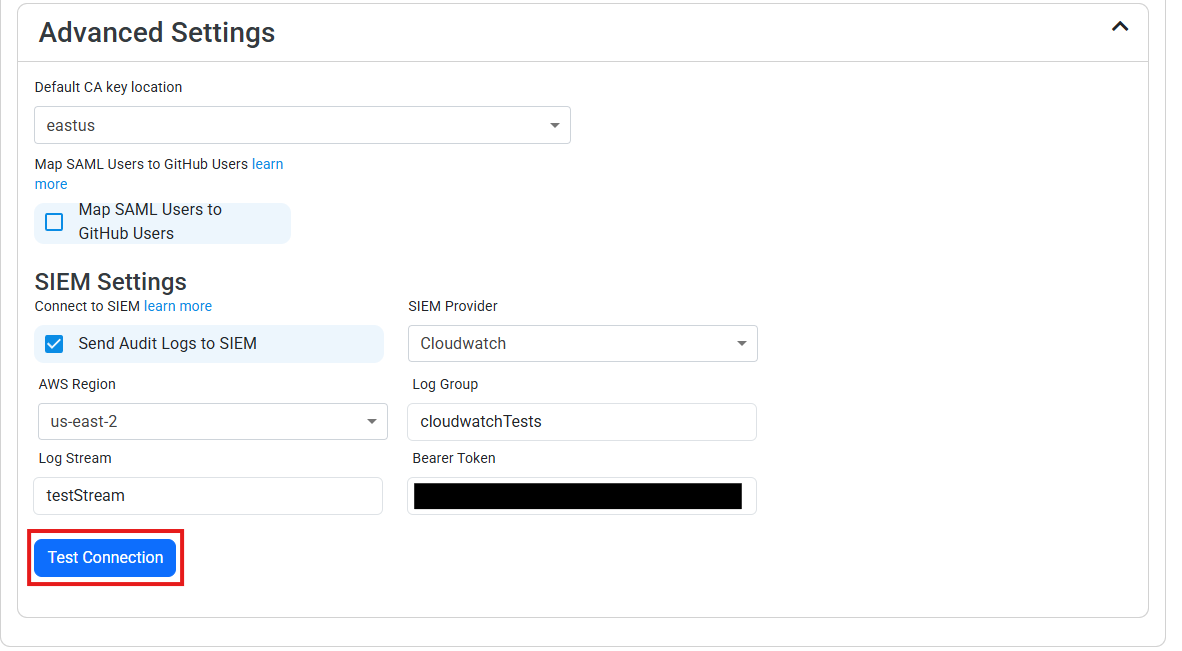
Input the values that you copied from the CloudWatch portal. Then, click Test Connection. This will create a test log in your CloudWatch SIEM (please allow a few minutes for the log to show up in the CloudWatch portal).
-
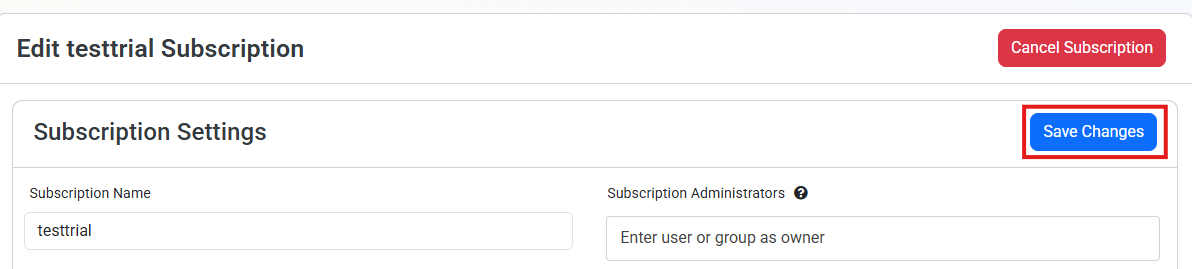
If the connection test is successful, click Save Changes.
-
EZSSH will now send your security alerts to your SIEM. If an error occurs it will email your subscription administrators. See below to see the different events EZSSH will send.
How To Create Alerts in CloudWatch to Monitor Your SSH Activity
We recommend setting up alerts for any high criticality event, and closely monitor medium and low events. To setup alerts in CloudWatch go to Actions -> Create metric filter within your log group. Here are some example filters to get you started:
Detect if a User Is Reusing SSH Keys
To detect any user that has reused an SSH key, set an alert if there are repeat instances of the UserPublicKey field:
fields event.UserPublicKey
| filter source = "EZSSH"
| stats count() as usageCount by event.UserPublicKey
| filter usageCount > 1
Get All SSH Requests that Granted an SSH Certificate
To get all the requests that created an SSH certificate, run the following query:
{ $.source = "EZSSH" && $.sourcetype = "EZSSH_SSH" && $.event.ActionPerformed != "Test Connection" && $.event.Certificate != "NA" }
This query can be then used to correlate with SSH logins to verify that all logins are done with an EZSSH certificate.
Get the Count of Git Certificates Requested by User
To get the number of git certificates a user has requested, run the following query
fields event.RequestorFriendlyName
| filter source = "EZSSH" and sourcetype = "EZSSH_SSH"
| stats count() as certRequests by event.RequestorFriendlyName
| sort certRequests desc
This query is useful to find anomalies on a user requesting a higher number of certificates than usual.